It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
share:
NebraskaGunOwner welcome to ATS!
I wonder if this could be communication between Hilley and her Women’s Leadership Council for Team Hillary, such a file could open whole new batch of legal troubles!
I have been curious about the current status and members Women’s Leadership Council for Team Hillary since I first learned of them after the Iowa caucus.
"voting stuff" - that does pique my interests!
For me, it was not like the Hillary Clinton server, it was like an email server she and others were using with political voting stuff," Guccifer said.
I wonder if this could be communication between Hilley and her Women’s Leadership Council for Team Hillary, such a file could open whole new batch of legal troubles!
I have been curious about the current status and members Women’s Leadership Council for Team Hillary since I first learned of them after the Iowa caucus.
"voting stuff" - that does pique my interests!
a reply to: AlaskanDad
I hope that NebraskaGunOwner was not so insulted that he is not coming back.
His research was interesting.
I hope that NebraskaGunOwner was not so insulted that he is not coming back.
His research was interesting.
And you can be sure Bill has 'doodled' a lot more women other than Hill.
originally posted by: UnBreakable
And you can be sure Bill has 'doodled' a lot more women other than Hill.
...and that Hill has doodled a few women with Bill too
originally posted by: UKTruth
originally posted by: UnBreakable
And you can be sure Bill has 'doodled' a lot more women other than Hill.
...and that Hill has doodled a few women with Bill too
But she wants them all for herself.
My dialogue with my sources left me with no doubt Tuesday night (Oct. 30) that Hillary’s made passes at women and that Muslim Huma Abedin is Hillary’s most likely source of romantic and sexual love.
www.lukeford.net...
She deleted her private stuff, fair enough, that should not be disclosed by TFOIA, BUT, there could be some personal stuff that could compromise her
if the server was indeed hacked. It would have been more prudent to hand everything over to the FBI. They are better equipped to identify possible
threats to a candidate for the next Prez of the most powerful country in the world. Why did she delete it, did she have something to hide? And the
process of deleting 10's of thousands of mails probably lead to non private stuff being deleted too. This whole thing stinks of a cover-up, only fools
won't see it. Smoke, fire stuff.
PS, anyone in the US needing email instructions to watch a TV show is not qualified to be president.
originally posted by: introvert
a reply to: NoCorruptionAllowed
Could you be more full of crap? I've never lied about Hillary.
Yes you did. You said she was "a woman of such renowned criminality".
She has never been convicted of a crime.
It is also irrelevant that no convictions have happened. Why? Because we all know she is guilty of lots of crimes.
Not only is that a logical fallacy, specifically an alleged certainty fallacy, she has not been convicted of a crime. A conviction is necessary.
Having no convictions doesn't mean she isn't guilty of committing crimes, and it also doesn't mean anyone should support her just because no convictions. Some rapists have got off Scott free, so because they weren't convicted, then you will support them too?
Support is irrelevant. I would still not call them a criminal unless they were convicted.
Get a dose of reality sonny.. Your arguments have no value.
I'm sure it doesn't have any value to someone that will lie about people and use logical fallacies, which have no place in a logical debate. But we all know (yes, i used your own logical fallacy) logic is rare round these parts.
You are mixing up two entirely different things. Being a criminal vs being convicted of a crime. You seem to be stating that if a person hasn't been convicted of a crime that they are not a criminal. If so...you are mistaken.
How many criminals do you know that haven't been convicted? How many people drive drunk but don't get caught...they are criminals. Illegal aliens are here only because they broke the law...they are criminals. They haven't been convicted, they simply broke the law. Here is the definition for you:
crim·i·nal
ˈkrimənl
noun
1. a person who has committed a crime.
See how easy that was! If you commit a crime you are a criminal. You don't have to be convicted. And besides...with the corrupt government of the USA, far too many criminals are never convicted yet alone tried in a court of law.
Yes...OJ is a criminal. Yes...Hillary is a criminal. So are many of us here. Anyone here get high once in a while? So instead of playing games with definitions (which you were wrong about anyway), how about dealing with the guts of the argument.
Hillary Clinton is a lying, cheating, bitch that has committed hundreds of crimes (or hired others to do so which is also a crime). If there were justice...she would have been hung so many times they would be digging up her corpse to hang her again. But there isn't justice, there isn't a justice department and there isn't a supreme court. There are just tools of the government. And those who wield the tools decide what they do.
edit on 5/9/2016 by WeAreAWAKE because: (no reason given)
I remember when the fellow was extradited from his country to the US by his countries allowance to be extradited... it was due to his peering into
Mrs. Clintons server. So there shouldnt really be any doubts requiring doodles as proof although they may not contain Top Secret materials like Mrs.
Clintons unprotected server or stripping Top Secret labels to email them to those without clearance... sort of like insider trading but with
information to eyes not cleared for viewing.
The real thing I am most concerned about, is his family back in his home country his wife and child depend on him as a bread winner, and being pulled to the US and being in a very remote part of the world, providing for his family used to take place through electronic means... of course when one is pulled in under suspicions of hacking such as Lorax was an Australian fellow lifeguard that setup and tested system securities through various pings was hauled in as they tried to gather evidence against him as one of the pings during the security test hit an off limits server...
The same deal, they tried to bankrupt him in legal fees and hold im as an example... but at the detriment of peoples families and incomes. Adam aka Lorax was finally cleared from charges after a couple years of battle and like Guicfer is and will be barred from using electronic devices, Adam can of course use them for online work but barred from them for anything else entirely. Im not sure how Guicfers country will handle the electronic medium but it will likely follow the US recommendation since they allowed extradition... if Guicfer has not had a gofundme or other crowd sourced fund setup to help his family, in the exposing of this corruption at the heart of the Clinton scandal... it would be nice if someone did so.
People should remember that at the very heart of anonymous is to remove corruption from politics to prevent totaliarianism and enquality in the masses as a sense of social justice and harmony. Meaning no matter how veiled corruption of bigbrother may be? Big brother has an even bigger brother watching them... and as their creedo goes? They do not forgive and they do not forget.
Power to the people then and now, especially when many governments and many officials have become so paranoid, of the very people that allow them power in the first place... it doesnt have to currupt obviously, and can be used as a greater sense of responsibility to the very people they are supposed to represent. When that does not happen? They only represent themselves and whhen it falls into justice? They say only a fool does such a thing.
As said in a previous post, I am not anonymous as I am transparent and wide open meaning I need no mask... but I do understand the cause and the fight very well as do many millions of people world wide as the internet is world wide and beyond borders... we can use this tecnology to connect each other as one family as many many do... or try to control it for their own personal gain and greed or fan flames of hate and division as many many do.
Thats the honest divide but since its really all one people... the world is already united, if you dont want to sit next to uncle Bob during a holiday meal its obvious you wouldnt have too, and thats just all part of freedom. Remove choices from adults and treat them like cildren and maybe they wont show up at the next holiday... thats just how that works as well. Nothing really to celebrate if it means living in misery when it should be a time of it yeah?
Hope everyone takes care of themselves and bares those in mind that have trouble doing so for various reasons and lend them a hand.
Good day/evening/night
The real thing I am most concerned about, is his family back in his home country his wife and child depend on him as a bread winner, and being pulled to the US and being in a very remote part of the world, providing for his family used to take place through electronic means... of course when one is pulled in under suspicions of hacking such as Lorax was an Australian fellow lifeguard that setup and tested system securities through various pings was hauled in as they tried to gather evidence against him as one of the pings during the security test hit an off limits server...
The same deal, they tried to bankrupt him in legal fees and hold im as an example... but at the detriment of peoples families and incomes. Adam aka Lorax was finally cleared from charges after a couple years of battle and like Guicfer is and will be barred from using electronic devices, Adam can of course use them for online work but barred from them for anything else entirely. Im not sure how Guicfers country will handle the electronic medium but it will likely follow the US recommendation since they allowed extradition... if Guicfer has not had a gofundme or other crowd sourced fund setup to help his family, in the exposing of this corruption at the heart of the Clinton scandal... it would be nice if someone did so.
People should remember that at the very heart of anonymous is to remove corruption from politics to prevent totaliarianism and enquality in the masses as a sense of social justice and harmony. Meaning no matter how veiled corruption of bigbrother may be? Big brother has an even bigger brother watching them... and as their creedo goes? They do not forgive and they do not forget.
Power to the people then and now, especially when many governments and many officials have become so paranoid, of the very people that allow them power in the first place... it doesnt have to currupt obviously, and can be used as a greater sense of responsibility to the very people they are supposed to represent. When that does not happen? They only represent themselves and whhen it falls into justice? They say only a fool does such a thing.
As said in a previous post, I am not anonymous as I am transparent and wide open meaning I need no mask... but I do understand the cause and the fight very well as do many millions of people world wide as the internet is world wide and beyond borders... we can use this tecnology to connect each other as one family as many many do... or try to control it for their own personal gain and greed or fan flames of hate and division as many many do.
Thats the honest divide but since its really all one people... the world is already united, if you dont want to sit next to uncle Bob during a holiday meal its obvious you wouldnt have too, and thats just all part of freedom. Remove choices from adults and treat them like cildren and maybe they wont show up at the next holiday... thats just how that works as well. Nothing really to celebrate if it means living in misery when it should be a time of it yeah?
Hope everyone takes care of themselves and bares those in mind that have trouble doing so for various reasons and lend them a hand.
Good day/evening/night
an update:
[Exclusive] Here’s PROOF Hillary lied about being hacked
source
Nice to see NGO's post is hitting the internet!
[Exclusive] Here’s PROOF Hillary lied about being hacked
Clinton has sworn up and down that her controversial, home-brewed email server was safe, secure and legal. She’s said there’s no proof at all that foreign hackers were able to break into it and peek at her top-secret emails containing critical national security data.
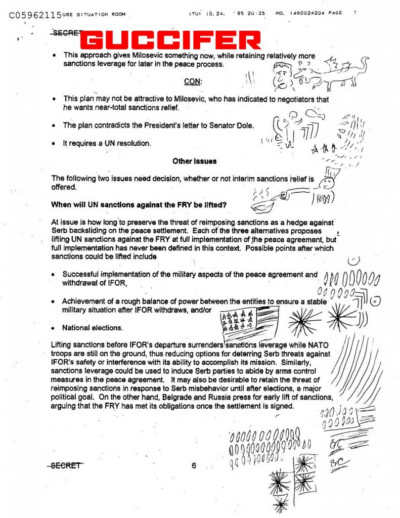
But Clinton’s biggest lie may have just been exposed in the most unlikely way possible: In a series of doodles drawn by husband Bill Clinton.
A shocking new revelation connects a hacker’s release of Bill Clinton’s silly White House drawings to what may be one of the biggest national security breaches in the nation’s history — one that comes with a 10-year jail sentence.
new evidence indicates that the stolen doodles came from the hacking into the former president’s personal server — the same server that was also being used to house wife Hillary’s emails.
source
Nice to see NGO's post is hitting the internet!
MORE evidence Guccifer was telling the truth:
lawnewz.com...
Deception Experts: Guccifer Telling Truth About Hacking Clinton’s Email Server
Phil Houston is CEO of QVerity, a training and consulting company specializing in detecting deception by employing a model he developed while at the Central Intelligence Agency. He has conducted thousands of interviews and interrogations for the CIA and other federal agencies. His colleague Don Tennant contributed to this report.
When Romanian hacker Marcel Lehel Lazar, also known as Guccifer, told NBC News senior investigative correspondent Cynthia McFadden that he had gained access to Hillary Clinton’s private email server, viewers worldwide were left to wonder whether his claim was true. Our analysis of Guccifer’s behavior in the interview left little doubt in our minds that—unfortunately—it was.
Let us be clear that in this case, the behavior available for analysis is quite minimal. Having said that, based on the lack of deceptive indicators exhibited by Guccifer in response to McFadden’s questions, we have concluded with a high degree of confidence that Guccifer was very likely successful in penetrating Clinton’s email server, as he claimed.
What remains unclear, however, is exactly what information resident in the server might have been compromised.
Guccifer told McFadden that Clinton had lied when she claimed her email server was absolutely safe—he stated categorically, “It’s not safe at all.” While we have concluded that that statement is likely truthful, and that Guccifer likely ascertained that himself, what we are unable to assess is whether or not he was able to access any classified information on the server. It’s equally unclear whether Guccifer was capable of identifying classified information, vs. unclassified information.
Our sense, based on Guccifer’s responses, is that there were some limitations to the access he was able to gain. We expect that as this story unfolds, and the investigation into Guccifer’s claims intensifies, U.S. authorities will identify those limitations—and exactly what vulnerabilities in the security of Clinton’s email server were identified by the Romanian hacker.
lawnewz.com...
edit on 9-5-2016 by IAMTAT because:
highlighting
Okay.
So it appears the Russians have copied tens of thousands of emails Guccifer hacked from Crooked Hillary's secret server.
There is currently a debate within the Kremlin about if and when to release them.
FULL ARTICLE (MUCH more interesting info.):
www.eutimes.net...
So it appears the Russians have copied tens of thousands of emails Guccifer hacked from Crooked Hillary's secret server.
There is currently a debate within the Kremlin about if and when to release them.
An intriguing Security Council (SC) report circulating in the Kremlin today suggests that a “war of words” has broken out between the Director of the Federal Security Service (FSB) Alexander Bortnikov and Chairwoman of the Council of Federation Valentina Matviyenko over the issue of releasing to the Western media tens-of-thousands of top secret and classified emails obtained by the Foreign Intelligence Service (SVR) from the private, but unsecured, computer (email server) belonging to former US Secretary of State, and present American presidential candidate, Hillary Clinton.
According to this report, beginning in 2011, SVR intelligence analysts began “serious/concerning” monitoring of a Romanian computer hacker named Marcel Lazăr Lehel (aka Guccifer) after he attempted, unsuccessfully, to break into the computer system of the Federation funded RT television network.
Following SVR procedures for the monitoring of international computer hackers, this report continues, Guccifer’s activities were followed and recorded (both physically and electronically) allowing these intelligence analysts, in 2013, to not only detect his breaking into the private computer of Secretary Clinton, but allowing the SVR to copy all of its contents too.
FULL ARTICLE (MUCH more interesting info.):
www.eutimes.net...
new topics
-
Where should Trump hold his next rally
2024 Elections: 2 hours ago -
Shocking Number of Voters are Open to Committing Election Fraud
US Political Madness: 3 hours ago -
Gov Kristi Noem Shot and Killed "Less Than Worthless Dog" and a 'Smelly Goat
2024 Elections: 3 hours ago -
Falkville Robot-Man
Aliens and UFOs: 4 hours ago -
James O’Keefe: I have evidence that exposes the CIA, and it’s on camera.
Whistle Blowers and Leaked Documents: 4 hours ago -
Australian PM says the quiet part out loud - "free speech is a threat to democratic dicourse"...?!
New World Order: 5 hours ago -
Ireland VS Globalists
Social Issues and Civil Unrest: 6 hours ago -
Biden "Happy To Debate Trump"
2024 Elections: 6 hours ago -
RAAF airbase in Roswell, New Mexico is on fire
Aliens and UFOs: 6 hours ago -
What is the white pill?
Philosophy and Metaphysics: 8 hours ago
top topics
-
A Warning to America: 25 Ways the US is Being Destroyed
New World Order: 16 hours ago, 21 flags -
Blast from the past: ATS Review Podcast, 2006: With All Three Amigos
Member PODcasts: 8 hours ago, 13 flags -
James O’Keefe: I have evidence that exposes the CIA, and it’s on camera.
Whistle Blowers and Leaked Documents: 4 hours ago, 12 flags -
Australian PM says the quiet part out loud - "free speech is a threat to democratic dicourse"...?!
New World Order: 5 hours ago, 11 flags -
Biden "Happy To Debate Trump"
2024 Elections: 6 hours ago, 10 flags -
Mike Pinder The Moody Blues R.I.P.
Music: 8 hours ago, 8 flags -
Ireland VS Globalists
Social Issues and Civil Unrest: 6 hours ago, 5 flags -
RAAF airbase in Roswell, New Mexico is on fire
Aliens and UFOs: 6 hours ago, 5 flags -
What is the white pill?
Philosophy and Metaphysics: 8 hours ago, 5 flags -
Putin, Russia and the Great Architects of the Universe
ATS Skunk Works: 12 hours ago, 4 flags
active topics
-
Krystalnacht on today's most elite Universities?
Social Issues and Civil Unrest • 11 • : TheWoker -
Remember These Attacks When President Trump 2.0 Retribution-Justice Commences.
2024 Elections • 59 • : TzarChasm -
Salvador Dali's Moustaches
People • 29 • : GENERAL EYES -
Mood Music Part VI
Music • 3111 • : TheWoker -
Where should Trump hold his next rally
2024 Elections • 12 • : StudioNada -
University of Texas Instantly Shuts Down Anti Israel Protests
Education and Media • 310 • : SchrodingersRat -
Candidate TRUMP Now Has Crazy Judge JUAN MERCHAN After Him - The Stormy Daniels Hush-Money Case.
Political Conspiracies • 815 • : Annee -
President BIDEN's FBI Raided Donald Trump's Florida Home for OBAMA-NORTH KOREA Documents.
Political Conspiracies • 35 • : Threadbarer -
2024 Pigeon Forge Rod Run - On the Strip (Video made for you)
Automotive Discussion • 8 • : WhitewaterSquirrel -
Gov Kristi Noem Shot and Killed "Less Than Worthless Dog" and a 'Smelly Goat
2024 Elections • 28 • : cherokeetroy