It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
share:
There are nineteen (19) towers identified in this article I just read. The conclusion in the article discount the NSA as the culprit because they
have easier and more complete ways to do this and dont need these towers.
They intercept the calls, then hand them off to real towers in the area - after having access to the handset and account to install whatever they like.
Interceptor Cellphone Towers being confirmed around the nation
Is this part of the same Android story being reported, or is it something else?
They intercept the calls, then hand them off to real towers in the area - after having access to the handset and account to install whatever they like.
Interceptor Cellphone Towers being confirmed around the nation
Is this part of the same Android story being reported, or is it something else?
edit on 3-9-2014 by Leonidas because: (no reason given)
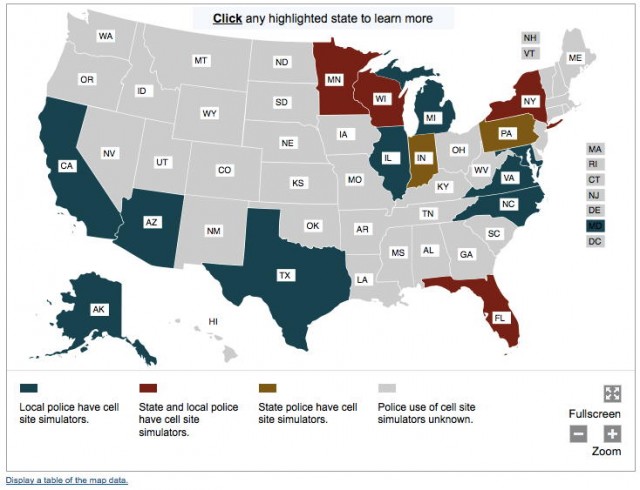
DHS Purchase Police StingRay Trackers
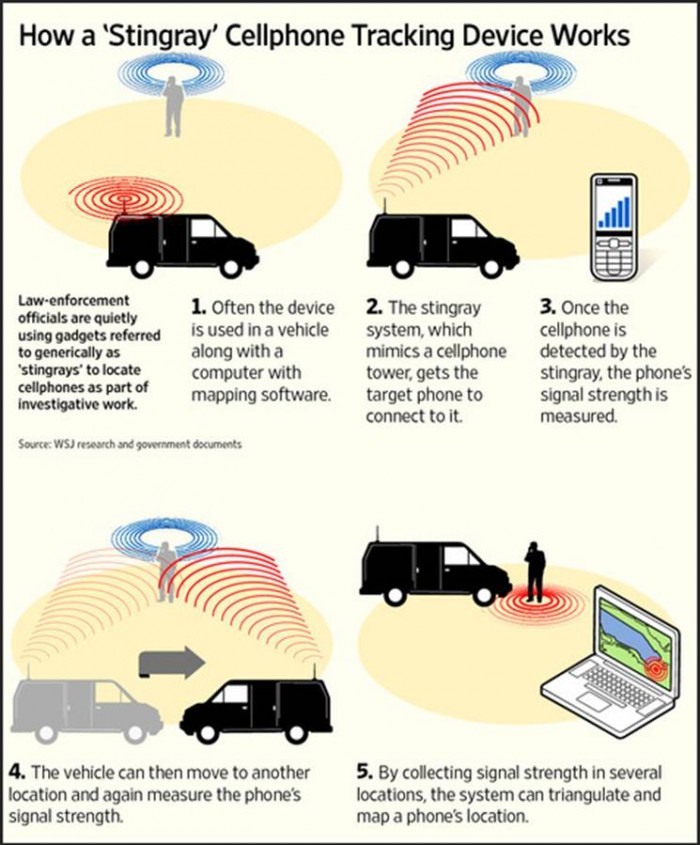
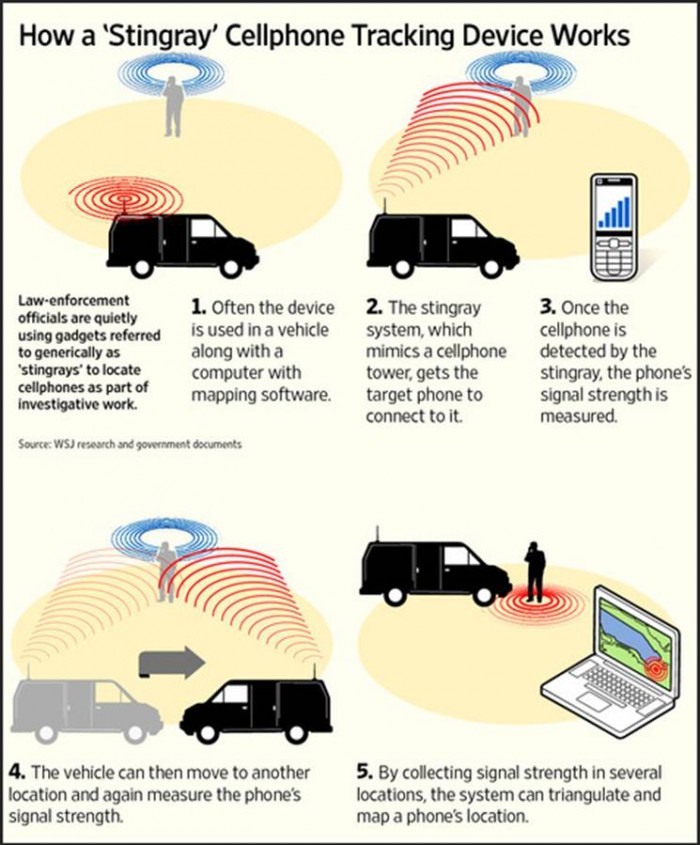
They can easily triangulate your position once they lock onto your signal. With a strong enough antenna, they could probably eliminate mobile stingray operations or already have. Turning off your GPS doesn't help either.
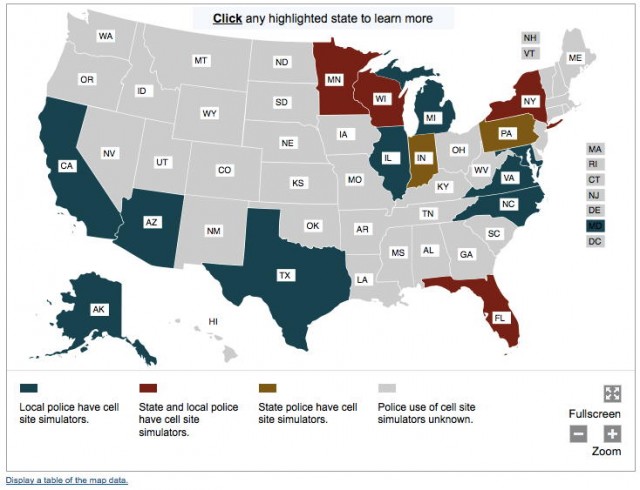
Media is reporting on “at least 25 police departments [who] own a Stingray” which allow those law enforcement entities to “tap into cellphone data in real time . . . capturing information about thousands of cellphone users at a time, whether they are targets of an investigation or not.”
The Electronic Frontier Foundation (EFF) explains that this IMSI catcher “tricks your phone into connecting to it. As a result, the government can figure out who, when and to where you are calling, the precise location of every device within the range, and with some devices, even capture the content of your conversations.”
They can easily triangulate your position once they lock onto your signal. With a strong enough antenna, they could probably eliminate mobile stingray operations or already have. Turning off your GPS doesn't help either.
edit on 3-9-2014 by eisegesis because: (no reason given)
a reply to: Leonidas
So these look like one of the odd things they installed at the rest stops along the highway, they did more because large trucks came and went and they worked for a year on each there was nothing wrong with the places they were all brand new and when they finished nothing changed except the grass and signs outside so i think they did some underground stuff.
One actually had a guard at the front blocked road the times I passed it and the other was blocked by cones but also by a truck parked sideways and a trail leading over a tunnel pass that cold let you walk across and to the rest area was also blocked.
So these look like one of the odd things they installed at the rest stops along the highway, they did more because large trucks came and went and they worked for a year on each there was nothing wrong with the places they were all brand new and when they finished nothing changed except the grass and signs outside so i think they did some underground stuff.
One actually had a guard at the front blocked road the times I passed it and the other was blocked by cones but also by a truck parked sideways and a trail leading over a tunnel pass that cold let you walk across and to the rest area was also blocked.
originally posted by: cdesigns
Very interesting, less than 2 miles away from my home there is a tower behind a house and is camoflauge as a big pine tree, I will take a picture later today.
Ah came across one I wish all towers looked like this.
www.govtech.com...

originally posted by: ANNED
NSA or a hacker looking for credit card numbers, passwords ect ect ect.
I only use my computer for anything important and use HTTPS Everywhere.
www.eff.org...
How many people out there use there iphones or Android to do banking or business without encryption.
Probably rather few.
For instance...my bank won't let me login unless I have a valid security cert. Example...a local grocery store was kind enough to build an "in-store" Wi-Fi for customers...no need to connect to phone network for data...The problem is; their proxy has an invalid security cert. I had to call the store management on that because customers can't get to their bank's site to conduct any required business. All this due to lack of proper security.
Very similar to a thread I saw last week.
A lot of implications that are not entirely supported by the facts.
This talks about fake “towers” and implies that the NSA is the operator of those towers.
Well that’s not the only possibility. Setting up a local cell is not that hard and not that costly.
There are companies that do it to improve connectivity in their campus for their employees.
They set up the tower and route the traffic over their corporate PBX. Their employees devices are authorized on the networks but all others are not.
So to your phone it looks like a fake tower.
There are other variations of this theme but it’s basically the same its cellular technology being used by legitimate businesses.
What they did not do is do some locating of one of these “towers” and then cross reference that location with the FCC’s transmitter database.
If the tower was fake or not legit it would not show up in that data. If it’s a business operating it then it would be there and be identified.
If they did that however they would not have a marketing angle for their special super secret cryptophone.
A lot of implications that are not entirely supported by the facts.
This talks about fake “towers” and implies that the NSA is the operator of those towers.
Well that’s not the only possibility. Setting up a local cell is not that hard and not that costly.
There are companies that do it to improve connectivity in their campus for their employees.
They set up the tower and route the traffic over their corporate PBX. Their employees devices are authorized on the networks but all others are not.
So to your phone it looks like a fake tower.
There are other variations of this theme but it’s basically the same its cellular technology being used by legitimate businesses.
What they did not do is do some locating of one of these “towers” and then cross reference that location with the FCC’s transmitter database.
If the tower was fake or not legit it would not show up in that data. If it’s a business operating it then it would be there and be identified.
If they did that however they would not have a marketing angle for their special super secret cryptophone.
This doesn't surprise me at all. I saw a photo of a device the CIA has: its a yagi antenna hooked to a briefcase with a bunch of electronics in it.
the only thing you need to do to intercept a call is transmit the strongest signal in the area. the device automatically seeks the best connects and
will just connect to the eavesdropping device. its then relayed to an actual tower where your call is completed. i imagine things like these are
installed all over the place. you would never be able to tell unless you has an hardened device that can detect that unsecured signal.
Here's a practical application that's annoying. While waiting for my vehicle to be impounded for parking tickets I can't pay, I texted my girl
saying "screw them. It was worth less than the tix. Part of me is okay with it, part of me wants to rig it with explosives,"
Ten minutes later there's a cop parked next to it. Twenty mins later, after the cop sees me going in and out, there's three cops. In another ten mins there was a helo right over me.
Of course I gestured that he's number one
Coincidence? Doubtful. Welcome to police state USA.
EF You Kay the NSA!
Ten minutes later there's a cop parked next to it. Twenty mins later, after the cop sees me going in and out, there's three cops. In another ten mins there was a helo right over me.
Of course I gestured that he's number one
Coincidence? Doubtful. Welcome to police state USA.
EF You Kay the NSA!
a reply to: AgentSmith
That's a lot of dismissive text, but you overlooked a key point to this story in your haste to absolve the Federal government.
Many of the 'fake' cell towers are located on restricted US government property, like military bases. I find it hard to believe that the military would allow criminal hackers to set up shop in the PX parking lot. Pretty sure they monitor EM traffic in those areas closely.
www.computerworld.com...
That's a lot of dismissive text, but you overlooked a key point to this story in your haste to absolve the Federal government.
Many of the 'fake' cell towers are located on restricted US government property, like military bases. I find it hard to believe that the military would allow criminal hackers to set up shop in the PX parking lot. Pretty sure they monitor EM traffic in those areas closely.
www.computerworld.com...
originally posted by: eisegesis
They can easily triangulate your position once they lock onto your signal. With a strong enough antenna, they could probably eliminate mobile stingray operations or already have. Turning off your GPS doesn't help either.
I'm sorry...BUT; this is NOT how triangulation works. It is not about the "strength" of the signal, except in how that signal strength relates to direction...and One only needs two bearings on a signal to precisely locate it.
originally posted by: tanka418
originally posted by: eisegesis
They can easily triangulate your position once they lock onto your signal. With a strong enough antenna, they could probably eliminate mobile stingray operations or already have. Turning off your GPS doesn't help either.
I'm sorry...BUT; this is NOT how triangulation works. It is not about the "strength" of the signal, except in how that signal strength relates to direction...and One only needs two bearings on a signal to precisely locate it.
It most certainly is possible. If you have an Android phone you can see for yourself. Go to "Settings" and select "Location". Depending on your version, you will see something like this, "Use GPS, Wi-Fi, and mobile networks to determine location". The feds don't even have to bother as most give their location away for free.
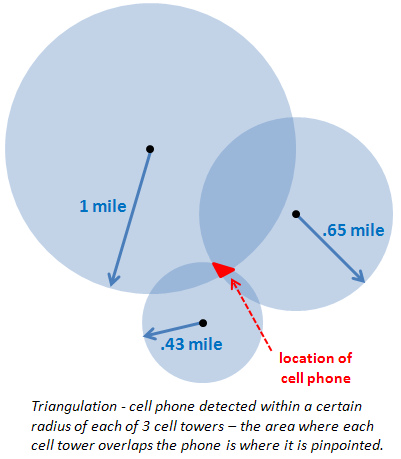
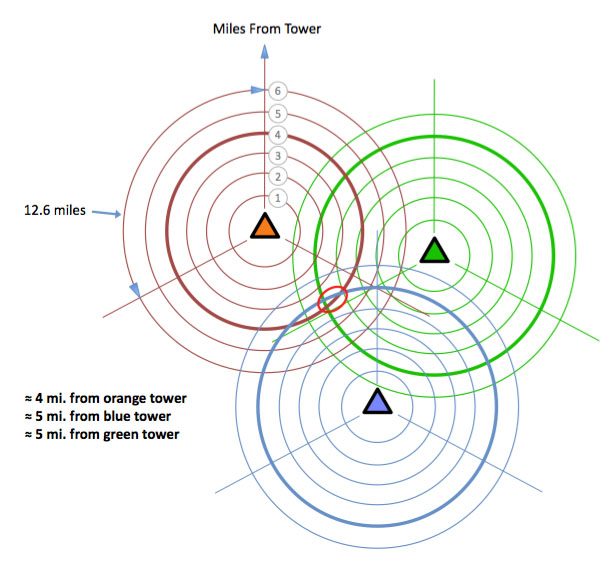
Sorry for the crude graphic...
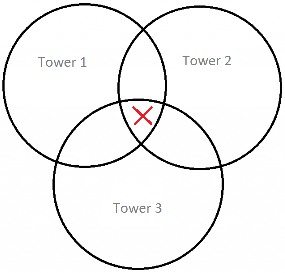
The size of the overlapping areas of signal are going to depend on the strength of the tower's broadcasting. The stronger the signal, the closer you are to that tower. If the signal to tower 1 is stronger than 2 and 3, you know that within that overlapping area, you are going to be closer to 1. If you are the same strength on 1 and 2, but weaker on 3, it's going to be top middle.
This is old news. And even though I have nothing to hide, I am EXTREMELY uncomfortable with strangers having a direct link to my phone or computer, capable of uploading "stuff" at will. How are we supposed to walk the straight path when it has become so easy to frame us as criminals?
Are you still doubting their capabilities?
edit on 3-9-2014 by eisegesis because: (no reason given)
a reply to: eisegesis
Sorry, I didn't say anything about "possible" or not. I said that is not how triangulation works.
Now, I am fully aware that what you are representing is "called" 'triangulation'...that isn't quite accurate though, and is a misuse of the word.
Real triangulation is done by "taking a bearing" on a radio source from two or more known locations and then using actual math (trig) the precise location of the radio source can be determined.
Using the crude example you have shown will give a location within several yards of the actual location, using "old school" triangulation is much more precise than that, and can be within only a few feet, almost as good as new GPS.
Old school triangulation has been around for decades and has been used by the FCC to locate rogue transmitters, by the Air Force to locate SAM sites, radio amateurs just for fun. And, of course in no case is signal strength an issue.
ETA: Distance of a transmitting antenna from a receiving antenna cannot be determined by signal strength, there are too many factors affecting the strength of a signal.
What can I say...for your PC get a firewall and configure it correctly...for your phone: never allow sensitive data on it. AND, always, ALWAYS pay attention to your data devices!
Sorry, I didn't say anything about "possible" or not. I said that is not how triangulation works.
Now, I am fully aware that what you are representing is "called" 'triangulation'...that isn't quite accurate though, and is a misuse of the word.
Real triangulation is done by "taking a bearing" on a radio source from two or more known locations and then using actual math (trig) the precise location of the radio source can be determined.
Using the crude example you have shown will give a location within several yards of the actual location, using "old school" triangulation is much more precise than that, and can be within only a few feet, almost as good as new GPS.
Old school triangulation has been around for decades and has been used by the FCC to locate rogue transmitters, by the Air Force to locate SAM sites, radio amateurs just for fun. And, of course in no case is signal strength an issue.
ETA: Distance of a transmitting antenna from a receiving antenna cannot be determined by signal strength, there are too many factors affecting the strength of a signal.
And even though I have nothing to hide, I am EXTREMELY uncomfortable with strangers having a direct link to my phone or computer, capable of uploading "stuff" at will. How are we supposed to walk the straight path when it has become so easy to frame us as criminals?
What can I say...for your PC get a firewall and configure it correctly...for your phone: never allow sensitive data on it. AND, always, ALWAYS pay attention to your data devices!
edit on 3-9-2014 by tanka418 because: (no reason given)
The only question that i would ask is - How are these systems supposed to work if there is not access? The shortest answer is they will not work.
Larson Camouflage Hmmm... These guys probably know what's up.
edit on 9/3/14 by VikingWarlord
because: (no reason given)
originally posted by: VikingWarlord
Larson Camouflage Hmmm..
That is crazy. Crucifixes, water towers, trees, cacti!
Some wouldn't pass in my neighbourhood but some would.
That's blown my mind.
If I knew whitch towers are fake.
I would um! take them out.
keep clear off the antener,
untill you take out the power.
thats if you wont to have babies.
you should do the same.
maybe a tin foil sack?
I would um! take them out.
keep clear off the antener,
untill you take out the power.
thats if you wont to have babies.
you should do the same.
maybe a tin foil sack?
If these baseband interceptors are crushing everything they can get on to their network to 2G, it makes me womder about two things:
1: Are they looking for a certain kind of phone? Or a phone configured in a certain way?
2: If the majority of these things are on military bases doesn't that mean they are doing the same thing to everyone on the base that doesn't have a Crypto500?
ETA: Yeah, the more I think about this the more I think that it has to do with risk mitigation on the part of those that have installed them (the baseband interceptors). The military is probably using them like a "purse-check" in terms of phones coming and going. The one in Vegas is doing the same, and I bet someone got charged a pretty penny for it.
I bet they aren't even terribly accurate when it comes to finding whatever it is they are trying to find, but not doing it is probably more expensive in the end than doing it.
1: Are they looking for a certain kind of phone? Or a phone configured in a certain way?
2: If the majority of these things are on military bases doesn't that mean they are doing the same thing to everyone on the base that doesn't have a Crypto500?
ETA: Yeah, the more I think about this the more I think that it has to do with risk mitigation on the part of those that have installed them (the baseband interceptors). The military is probably using them like a "purse-check" in terms of phones coming and going. The one in Vegas is doing the same, and I bet someone got charged a pretty penny for it.
I bet they aren't even terribly accurate when it comes to finding whatever it is they are trying to find, but not doing it is probably more expensive in the end than doing it.
edit on 3-9-2014 by Bybyots because: . : .
It seems like very few read the article, these towers are forcing cellphones onto a lesser encrypted method of calling and data so they can listen.
Why really doesn't matter, did anyone ask you if they could listen to your phone calls and read your email? The FBI is all over the news about the seriousness of this cell phone hacker posting the same pics that they themselves are viewing without probable cause.
It may very well be the NSA just fishing, or the police spending money they have been given or the military doing it simply because they can.
None of which is right.
Why really doesn't matter, did anyone ask you if they could listen to your phone calls and read your email? The FBI is all over the news about the seriousness of this cell phone hacker posting the same pics that they themselves are viewing without probable cause.
It may very well be the NSA just fishing, or the police spending money they have been given or the military doing it simply because they can.
None of which is right.
edit on 3-9-2014 by circuitsports because: (no reason given)
new topics
-
Putin, Russia and the Great Architects of the Universe
ATS Skunk Works: 16 minutes ago -
A Warning to America: 25 Ways the US is Being Destroyed
New World Order: 4 hours ago -
President BIDEN's FBI Raided Donald Trump's Florida Home for OBAMA-NORTH KOREA Documents.
Political Conspiracies: 10 hours ago
top topics
-
President BIDEN's FBI Raided Donald Trump's Florida Home for OBAMA-NORTH KOREA Documents.
Political Conspiracies: 10 hours ago, 28 flags -
A Warning to America: 25 Ways the US is Being Destroyed
New World Order: 4 hours ago, 10 flags -
Gaza Terrorists Attack US Humanitarian Pier During Construction
Middle East Issues: 16 hours ago, 8 flags -
Las Vegas UFO Spotting Teen Traumatized by Demon Creature in Backyard
Aliens and UFOs: 15 hours ago, 6 flags -
2024 Pigeon Forge Rod Run - On the Strip (Video made for you)
Automotive Discussion: 16 hours ago, 4 flags -
Is AI Better Than the Hollywood Elite?
Movies: 12 hours ago, 3 flags -
The functionality of boldening and italics is clunky and no post char limit warning?
ATS Freshman's Forum: 17 hours ago, 1 flags -
Maestro Benedetto
Literature: 12 hours ago, 1 flags -
Putin, Russia and the Great Architects of the Universe
ATS Skunk Works: 16 minutes ago, 0 flags
active topics
-
SETI chief says US has no evidence for alien technology. 'And we never have'
Aliens and UFOs • 75 • : Hecate666 -
Las Vegas UFO Spotting Teen Traumatized by Demon Creature in Backyard
Aliens and UFOs • 13 • : FlyersFan -
Putin, Russia and the Great Architects of the Universe
ATS Skunk Works • 4 • : CosmicFocus -
Mood Music Part VI
Music • 3105 • : BrucellaOrchitis -
The Acronym Game .. Pt.3
General Chit Chat • 7752 • : bally001 -
Is AI Better Than the Hollywood Elite?
Movies • 18 • : Hecate666 -
A Warning to America: 25 Ways the US is Being Destroyed
New World Order • 7 • : BrucellaOrchitis -
Hate makes for strange bedfellows
US Political Madness • 49 • : network dude -
Truth Social goes public, be careful not to lose your money
Mainstream News • 131 • : burritocat -
Cars and Coffee - Knoxville, TN 2023
Automotive Discussion • 12 • : adamfrank