It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
share:
originally posted by: Char-Lee
originally posted by: cdesigns
Very interesting, less than 2 miles away from my home there is a tower behind a house and is camoflauge as a big pine tree, I will take a picture later today.
Ah came across one I wish all towers looked like this.
www.govtech.com...
Looks very similar to the one close by my house, the one close to my house has more camouflage (limbs an leafs) and its also painted brown. It's behind a house that only has about 2-3 more houses close by. The funny thing is that I have Sprint, ATT and Tmobile phones laying around and all get bad signal here. I'm missing verizon though.
I was going to take a picture but I found it on Google Earth
You can see it in the middle
Put this address on google maps and you will find it by looking around on street view
17558 Hartwood Marsh Rd, Clermont, FL

You can see it in the middle
Put this address on google maps and you will find it by looking around on street view
17558 Hartwood Marsh Rd, Clermont, FL

edit on 3-9-2014 by cdesigns because: (no reason given)
I'm not suggesting that some people aren't out for some evil or sinister use for this technolgy or information. But I did want to suggest something
in regards to the ones being on military installations.
Imagine a scenario where somehow, somway, someone takes truck full of explosives onto a miltary base and kills hundres of our troops. Imagine the outcry for better security and intelligence gathering. Now imagine if that base didn't have the ability to monitor cell phone track around the base. They had no early intelligence warnings that someone was planning something. That would be a terrible day for America.
Now imagine if they did, and the sole purpose was to listen for possible warnings or attacks. Some tracking algorythm picked up on a few key words, an alert goes out to SP's or MP's to either increase security protocol or shut down the base completely. They find and detain the bad guys or at the very least scare them off.
No dead soldiers, and you'd likely hear very little about it because it's not shocking enough to be carried on MSM. My point is, not everything and everyone is sinister in nature. Not everyone is out to get your nude photos stored on your phone or your password/credit card numbers/etc. Sometimes this technology is used to save lives.
But there certainly is no reason for it to be in a Casino or anything like that.
Imagine a scenario where somehow, somway, someone takes truck full of explosives onto a miltary base and kills hundres of our troops. Imagine the outcry for better security and intelligence gathering. Now imagine if that base didn't have the ability to monitor cell phone track around the base. They had no early intelligence warnings that someone was planning something. That would be a terrible day for America.
Now imagine if they did, and the sole purpose was to listen for possible warnings or attacks. Some tracking algorythm picked up on a few key words, an alert goes out to SP's or MP's to either increase security protocol or shut down the base completely. They find and detain the bad guys or at the very least scare them off.
No dead soldiers, and you'd likely hear very little about it because it's not shocking enough to be carried on MSM. My point is, not everything and everyone is sinister in nature. Not everyone is out to get your nude photos stored on your phone or your password/credit card numbers/etc. Sometimes this technology is used to save lives.
But there certainly is no reason for it to be in a Casino or anything like that.
originally posted by: eisegesis
originally posted by: tanka418
originally posted by: eisegesis
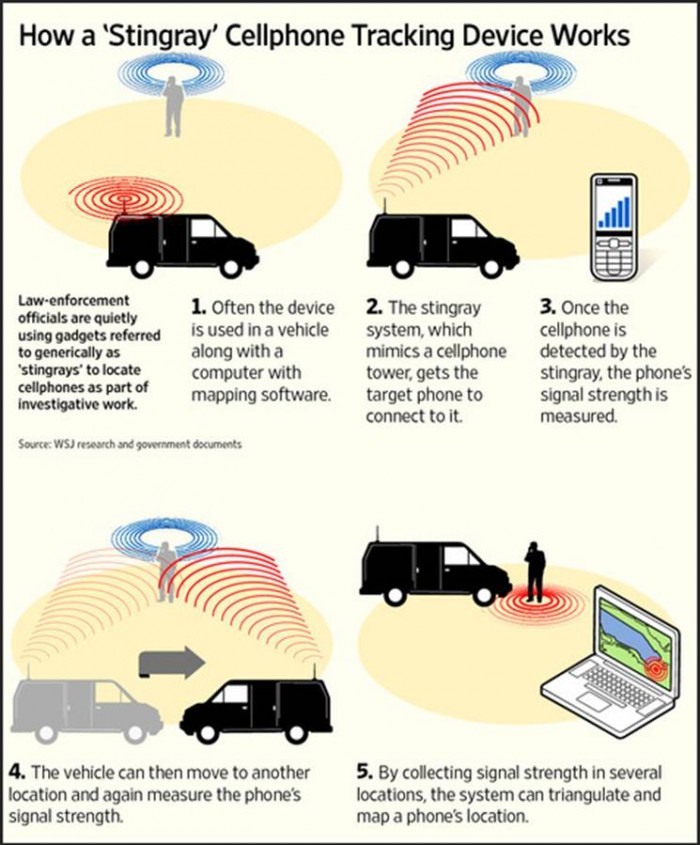
They can easily triangulate your position once they lock onto your signal. With a strong enough antenna, they could probably eliminate mobile stingray operations or already have. Turning off your GPS doesn't help either.
I'm sorry...BUT; this is NOT how triangulation works. It is not about the "strength" of the signal, except in how that signal strength relates to direction...and One only needs two bearings on a signal to precisely locate it.
It most certainly is possible. If you have an Android phone you can see for yourself. Go to "Settings" and select "Location". Depending on your version, you will see something like this, "Use GPS, Wi-Fi, and mobile networks to determine location". The feds don't even have to bother as most give their location away for free.
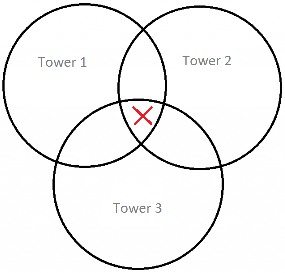
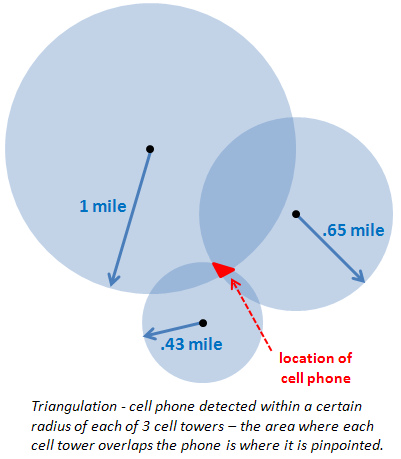
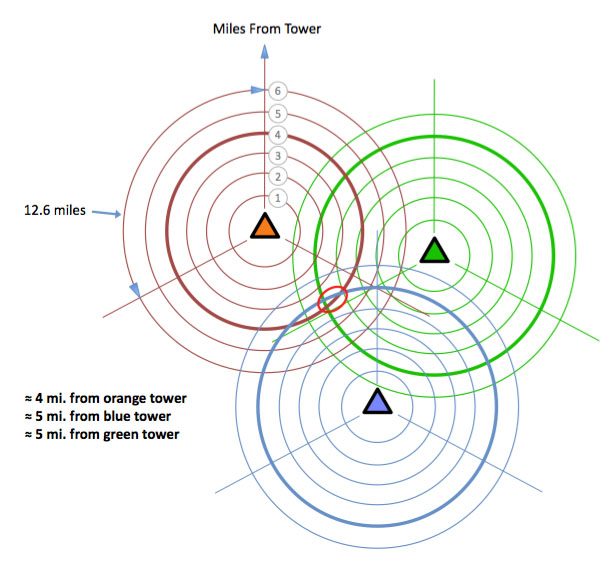
Sorry for the crude graphic...
The size of the overlapping areas of signal are going to depend on the strength of the tower's broadcasting. The stronger the signal, the closer you are to that tower. If the signal to tower 1 is stronger than 2 and 3, you know that within that overlapping area, you are going to be closer to 1. If you are the same strength on 1 and 2, but weaker on 3, it's going to be top middle.
This is old news. And even though I have nothing to hide, I am EXTREMELY uncomfortable with strangers having a direct link to my phone or computer, capable of uploading "stuff" at will. How are we supposed to walk the straight path when it has become so easy to frame us as criminals?
Are you still doubting their capabilities?
I went to location under my settings and it didn't give me an option for WiFi only. I changed my selection from GPS/WiFi/Mobiel network to GPS only to see what that did and I didn't notice anything however I'm sure I'd notice in a dead area that had no signal or WiFi.
Then when I re-selected the original setting, a pop up box popped up telling me to confirm that Google could gather data without my knowing etc. I took screen shots but I'm on my phone now and don't know how to upload the pictures to my post here.
Then when I switched it back
edit on Jam9uamThu, 04 Sep 2014 00:28:33 -050014 13 by Mjab6910 because: typo
a reply to: Maxmars
Had a quick look at the link doesn't really say what's claimed in the title.
So we have a guy PUSHING his OWN product claiming dozens of towers with NO real proof of the fake claim and in the link a road trip of possibly up to 650 miles they find 8 of these claimed fake towers.
Now since his phone is $3500 dollars what better way to push sales than make claims WE can't really check!!!
Had a quick look at the link doesn't really say what's claimed in the title.
So we have a guy PUSHING his OWN product claiming dozens of towers with NO real proof of the fake claim and in the link a road trip of possibly up to 650 miles they find 8 of these claimed fake towers.
Now since his phone is $3500 dollars what better way to push sales than make claims WE can't really check!!!
a reply to: douglas5
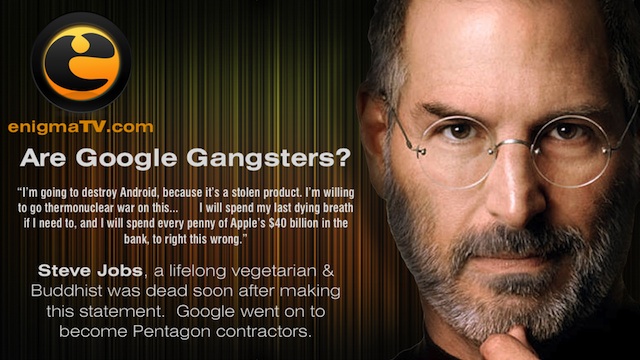
Seems that Jobs forgot his roots: he and Apple co-founder Wozniak were hackers themselves in the 1970s. They made "blue boxes" which could be used to cheat phone companies out of their money by allowing the users of these blue boxes to make long distance phone calls without charge. It was Jobs who saw the commercial value of these boxes and sold them for $170 each. However, the boxes he built were based on ideas and teachings of the famous (though smelly) Capt'n Crunch (John Draper).
Google and Apple both earn money from the hard work of the hacker community. But at least Google returns something to the community for free, which Apple never did.
Seems that Jobs forgot his roots: he and Apple co-founder Wozniak were hackers themselves in the 1970s. They made "blue boxes" which could be used to cheat phone companies out of their money by allowing the users of these blue boxes to make long distance phone calls without charge. It was Jobs who saw the commercial value of these boxes and sold them for $170 each. However, the boxes he built were based on ideas and teachings of the famous (though smelly) Capt'n Crunch (John Draper).
Google and Apple both earn money from the hard work of the hacker community. But at least Google returns something to the community for free, which Apple never did.
a reply to: Maxmars
I was just going to post the same sort of story. First time I saw something like it on Yahoo News!
finance.yahoo.com...
I was just going to post the same sort of story. First time I saw something like it on Yahoo News!
finance.yahoo.com...
I wonder what would happen and how fast the response would be if you cut the power wire to these fine units?
a reply to: douglas5
He is not thinking about anything
he is dead, and dead don't think...
unless you believe he faked his death
& now lives in RIO
but I guess if you are a fruit fan-boy
it makes for a great conspiracy
its not a fruit vs bot thing
every1's signal is intercepted
for whatever reason....
not good @ all
He is not thinking about anything
he is dead, and dead don't think...
unless you believe he faked his death
& now lives in RIO
but I guess if you are a fruit fan-boy
it makes for a great conspiracy
its not a fruit vs bot thing
every1's signal is intercepted
for whatever reason....
not good @ all
a reply to: Maxmars
This is a really important story, and I'm glad to see it published here. But the headline about Android devices is misleading, this effects all of them.
I'm seeing this backlash against Google (maker of Android), when the pics leaked off of Apple devices. Here's the example I just saw:
entertainthis.usatoday.com...
So the Apple leaks are being included in an exhibit called "fear Google". Its true Google probably has many of the same vlunerabilities here, they are not exempt. But at the same time, Google had nothing to do with this. Wired documents what happened clearly here:
www.wired.com...
So you have a police surveillance tool, being used by criminals to get the pics. You have both the means, and the motivation. The problems are right in front of every one, and its bigger than just any one of these too. This is a dumb time for Apple vs Google wars.
This is a really important story, and I'm glad to see it published here. But the headline about Android devices is misleading, this effects all of them.
I'm seeing this backlash against Google (maker of Android), when the pics leaked off of Apple devices. Here's the example I just saw:
entertainthis.usatoday.com...
So the Apple leaks are being included in an exhibit called "fear Google". Its true Google probably has many of the same vlunerabilities here, they are not exempt. But at the same time, Google had nothing to do with this. Wired documents what happened clearly here:
www.wired.com...
So you have a police surveillance tool, being used by criminals to get the pics. You have both the means, and the motivation. The problems are right in front of every one, and its bigger than just any one of these too. This is a dumb time for Apple vs Google wars.
originally posted by: bitsforbytes
...
The more time moves forward, the more we become dependent on technology, the more they can control us. Being dependent is okay, it depends on what and who.
In my mind, I think there is the outstanding illusion that any attempt at security by the 'experts' has always been a con job. Ultimately the protocol and infrastructure in our technology was not engineered to deny access, but to allow it.
Yet all these technology manufacturers perpetuate the illusion of security; never acknowledging that the only thing secure about any device is its user, lacking that, the rest is largely pointless. Knowing that, how could they ask for so much money to provide something that's impossible to provide?
originally posted by: WeRpeons
a reply to: Maxmars
...And the representatives we vote into office...
Not to belabor a fine point, but the real question of representation is the nail on the head - IF you expect anyone to protect you from institutionalized exploitation; be it commercial, or intellectual. I suspect that kind of protection is a moot point... our representatives do as the party commands... or they turn in their jersey and hop to the other side.
In the end, we can only elect those a certain body of individuals who are made available for us to vote for. Then the media generates billions in revenue. The five owners are in hog heaven... what's not to like?... it's not like we can change that.
Watch me try. It'll be entertaining.
new topics
-
University of Texas Instantly Shuts Down Anti Israel Protests
Education and Media: 1 hours ago -
Any one suspicious of fever promotions events, major investor Goldman Sachs card only.
The Gray Area: 3 hours ago -
God's Righteousness is Greater than Our Wrath
Religion, Faith, And Theology: 7 hours ago -
Electrical tricks for saving money
Education and Media: 10 hours ago
top topics
-
VP's Secret Service agent brawls with other agents at Andrews
Mainstream News: 12 hours ago, 10 flags -
Cats Used as Live Bait to Train Ferocious Pitbulls in Illegal NYC Dogfighting
Social Issues and Civil Unrest: 16 hours ago, 8 flags -
Nearly 70% Of Americans Want Talks To End War In Ukraine
Political Issues: 12 hours ago, 4 flags -
Electrical tricks for saving money
Education and Media: 10 hours ago, 4 flags -
Sunak spinning the sickness figures
Other Current Events: 12 hours ago, 3 flags -
Late Night with the Devil - a really good unusual modern horror film.
Movies: 14 hours ago, 2 flags -
Any one suspicious of fever promotions events, major investor Goldman Sachs card only.
The Gray Area: 3 hours ago, 2 flags -
The Good News According to Jesus - Episode 1
Religion, Faith, And Theology: 17 hours ago, 1 flags -
God's Righteousness is Greater than Our Wrath
Religion, Faith, And Theology: 7 hours ago, 0 flags -
University of Texas Instantly Shuts Down Anti Israel Protests
Education and Media: 1 hours ago, 0 flags
active topics
-
Nearly 70% Of Americans Want Talks To End War In Ukraine
Political Issues • 33 • : andy06shake -
Sunak spinning the sickness figures
Other Current Events • 11 • : McUrnsalso -
Any one suspicious of fever promotions events, major investor Goldman Sachs card only.
The Gray Area • 6 • : ImagoDei -
University of Texas Instantly Shuts Down Anti Israel Protests
Education and Media • 1 • : PorkChop96 -
Reason of the Existence
The Gray Area • 20 • : belkide -
Black mirror, what happened.
Television • 20 • : seekshelter -
God's Righteousness is Greater than Our Wrath
Religion, Faith, And Theology • 25 • : andy06shake -
Russia Ukraine Update Thread - part 3
World War Three • 5730 • : Arbitrageur -
VP's Secret Service agent brawls with other agents at Andrews
Mainstream News • 43 • : Hakaiju -
Everest-sized ‘Devil comet’ Pons-Brooks Visible Now
Space Exploration • 17 • : Compendium