It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
share:
Stellar Wind is not the only project that I will be discussing today. There are lots of different agencies that are currently doing surveillance all
over the world. This we know as fact. What I would like to bring about is who they are, where they are, how powerful they are, and how each and
everyone of us will be affected (even those that think that the "underground" internet will not be affected.)
One of the largest and I think the smartest ways that those that choose to provide, and administer this type of intrusion, give the "regular" man and women the notion that we are fully aware of the technology that is out there, this my friends is far from true.
There will be numbers, and names of programs, and storage information that will boggle the mind. NO this is not coming in in the future.... this is NOW!!
Welcome to Countries Biggest Spy Centers. The Utah data center.

www.wired.com...
www.bibliotecapleyades.net...
Now just wrap your mind up on the amount of information that can be stored here, why in the world would there be a reason for such a place? This isn't your typical machine, or station for information storing of the "usual suspects". This is at a much grander scale.
The usual "threat" has become a monster within itself, as we seek further "security" we are in fact every day become one of the "wanted", or the less spoken but always popular "undesirable". There is no way, shape, or form this is going to be used for those that our so loving and caring PTB are protecting us from.
As you can also see they seem to be now going after those that hold certain secrets on the "underground" level of the internet. Which many are not aware of. There are many "telecom" companies that have decided to jump the "we will hand what ever you want over" train in order to avoid prosecution or interruption of their services.
Though we have found an outlet in our own little worlds on the World Wide Web, the seem to have noticed that we cannot be stopped on certain levels, the have now got their eyes set on the core of what we seem to treasure the most. Freedom of expression, and the wanting of knowledge, beyond their indoctrination.
Peace, NRE.
BTW, there is more to come.
One of the largest and I think the smartest ways that those that choose to provide, and administer this type of intrusion, give the "regular" man and women the notion that we are fully aware of the technology that is out there, this my friends is far from true.
There will be numbers, and names of programs, and storage information that will boggle the mind. NO this is not coming in in the future.... this is NOW!!
Welcome to Countries Biggest Spy Centers. The Utah data center.

Just off Beef Hollow Road, less than a mile from brethren headquarters, thousands of hard-hatted construction workers in sweat-soaked T-shirts are laying the groundwork for the newcomers’ own temple and archive, a massive complex so large that it necessitated expanding the town’s boundaries. Once built, it will be more than five times the size of the US Capitol.
Rather than Bibles, prophets, and worshippers, this temple will be filled with servers, computer intelligence experts, and armed guards. And instead of listening for words flowing down from heaven, these newcomers will be secretly capturing, storing, and analyzing vast quantities of words and images hurtling through the world’s telecommunications networks. In the little town of Bluffdale, Big Love and Big Brother have become uneasy neighbors.
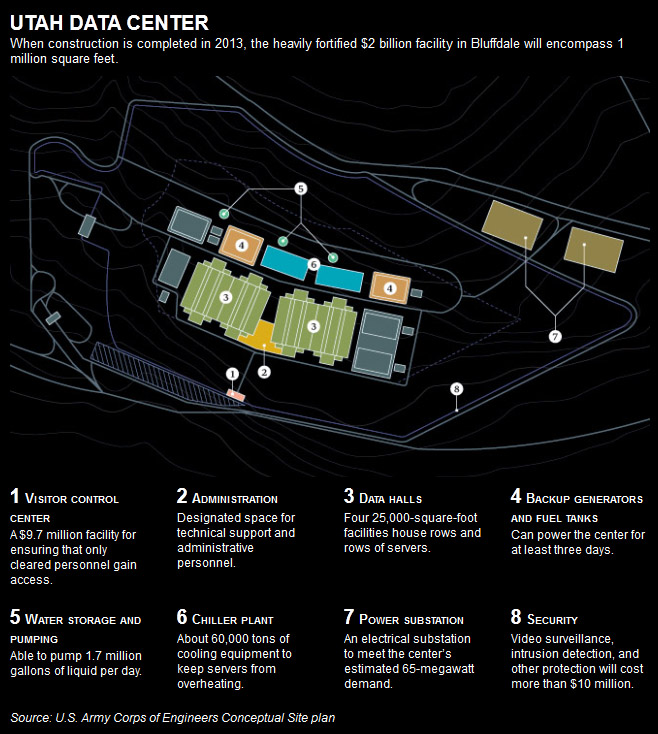
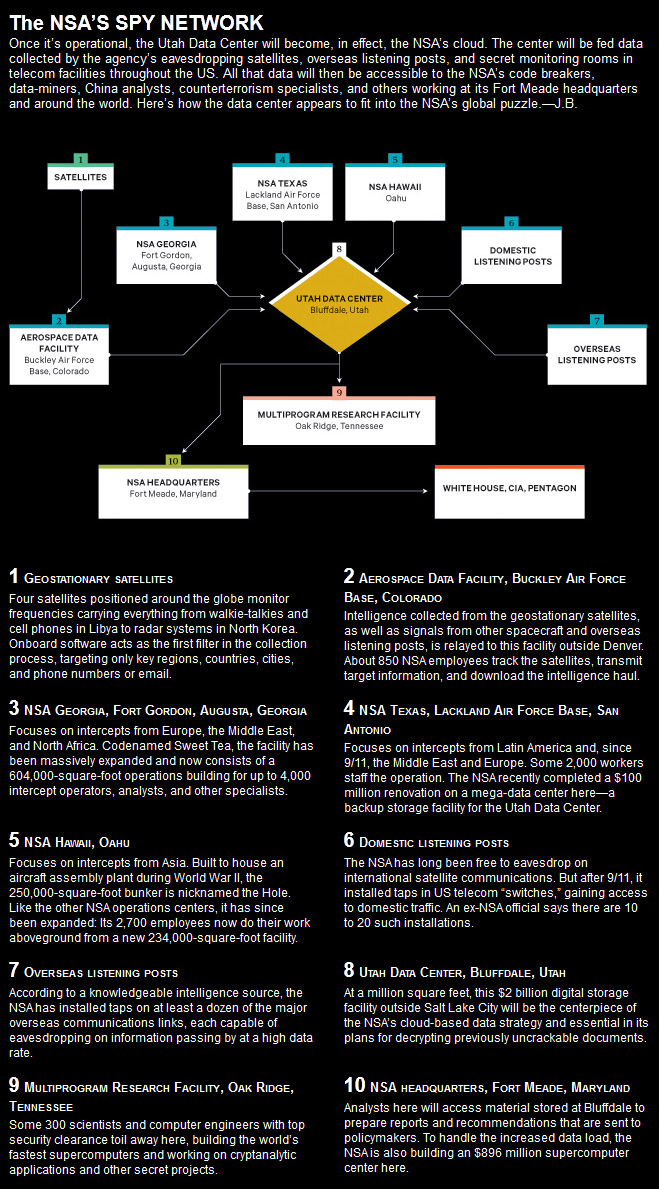
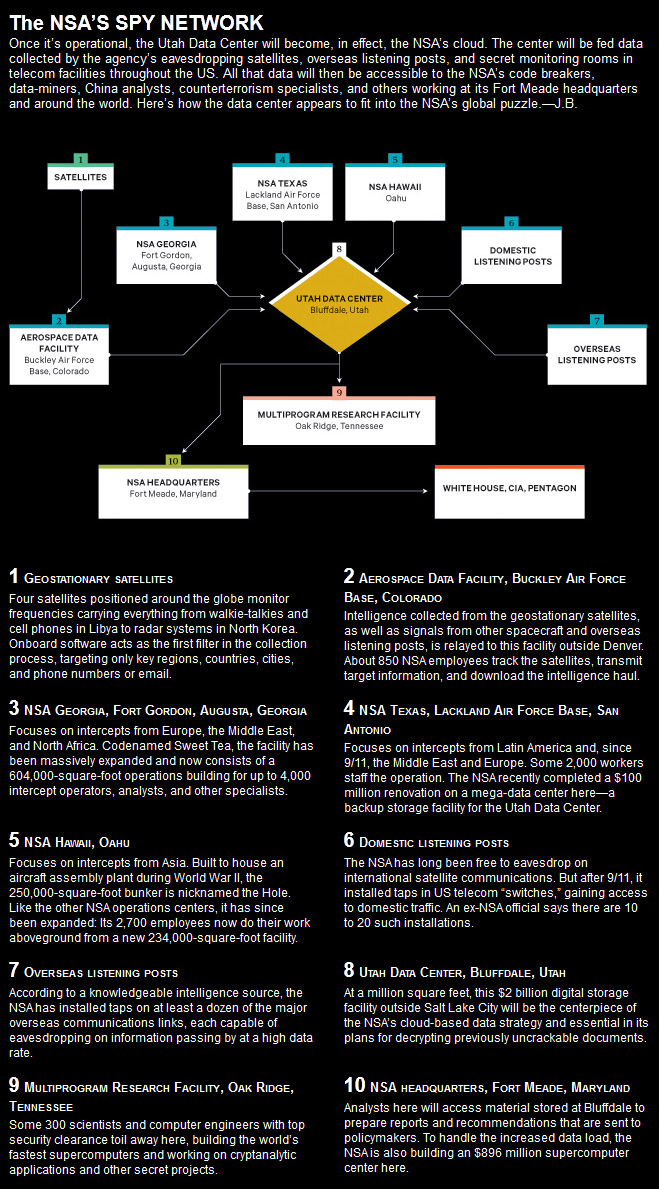
Under construction by contractors with top-secret clearances, the blandly named Utah Data Center is being built for the National Security Agency. A project of immense secrecy, it is the final piece in a complex puzzle assembled over the past decade. Its purpose: to intercept, decipher, analyze, and store vast swaths of the world’s communications as they zap down from satellites and zip through the underground and undersea cables of international, foreign, and domestic networks. The heavily fortified $2 billion center should be up and running in September 2013. Flowing through its servers and routers and stored in near-bottomless databases will be all forms of communication, including the complete contents of private emails, cell phone calls, and Google searches, as well as all sorts of personal data trails—parking receipts, travel itineraries, bookstore purchases, and other digital “pocket litter.” It is, in some measure, the realization of the “total information awareness” program created during the first term of the Bush administration—an effort that was killed by Congress in 2003 after it caused an outcry over its potential for invading Americans’ privacy.
But “this is more than just a data center,” says one senior intelligence official who until recently was involved with the program. The mammoth Bluffdale center will have another important and far more secret role that until now has gone unrevealed. It is also critical, he says, for breaking codes. And code-breaking is crucial, because much of the data that the center will handle—financial information, stock transactions, business deals, foreign military and diplomatic secrets, legal documents, confidential personal communications—will be heavily encrypted. According to another top official also involved with the program, the NSA made an enormous breakthrough several years ago in its ability to cryptanalyze, or break, unfathomably complex encryption systems employed by not only governments around the world but also many average computer users in the US. The upshot, according to this official: “Everybody’s a target; everybody with communication is a target.”
www.wired.com...
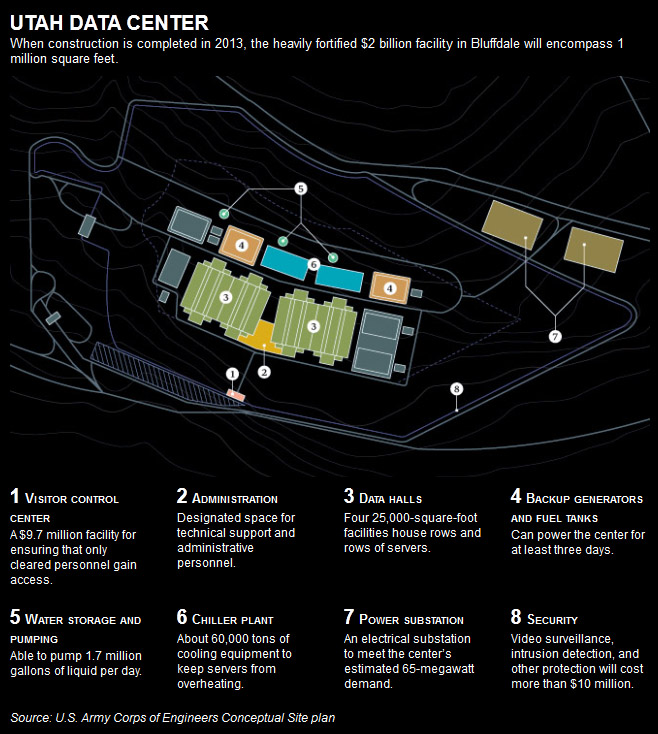
Electricity will come from the center’s own substation built by Rocky Mountain Power to satisfy the 65-megawatt power demand. Such a mammoth amount of energy comes with a mammoth price tag - about $40 million a year, according to one estimate.
Given the facility’s scale and the fact that a terabyte of data can now be stored on a flash drive the size of a man’s pinky, the potential amount of information that could be housed in Bluffdale is truly staggering. But so is the exponential growth in the amount of intelligence data being produced every day by the eavesdropping sensors of the NSA and other intelligence agencies.
As a result of this “expanding array of theater airborne and other sensor networks,” as a 2007 Department of Defense report puts it, the Pentagon is attempting to expand its worldwide communications network, known as the Global Information Grid, to handle yottabytes (1024 bytes) of data. (A yottabyte is a septillion bytes - so large that no one has yet coined a term for the next higher magnitude.)
It needs that capacity because, according to a recent report by Cisco, global Internet traffic will quadruple from 2010 to 2015, reaching 966 exabytes per year. (A million exabytes equal a yottabyte.)
In terms of scale, Eric Schmidt, Google’s former CEO, once estimated that the total of all human knowledge created from the dawn of man to 2003 totaled 5 exabytes.
And the data flow shows no sign of slowing.
In 2011 more than 2 billion of the world’s 6.9 billion people were connected to the Internet. By 2015, market research firm IDC estimates, there will be 2.7 billion users. Thus, the NSA’s need for a 1-million-square-foot data storehouse. Should the agency ever fill the Utah center with a yottabyte of information, it would be equal to about 500 quintillion (500,000,000,000,000,000,000) pages of text.
The data stored in Bluffdale will naturally go far beyond the world’s billions of public web pages. The NSA is more interested in the so-called invisible web, also known as the deep web or deepnet - data beyond the reach of the public.
www.bibliotecapleyades.net...
Now just wrap your mind up on the amount of information that can be stored here, why in the world would there be a reason for such a place? This isn't your typical machine, or station for information storing of the "usual suspects". This is at a much grander scale.
The usual "threat" has become a monster within itself, as we seek further "security" we are in fact every day become one of the "wanted", or the less spoken but always popular "undesirable". There is no way, shape, or form this is going to be used for those that our so loving and caring PTB are protecting us from.
As you can also see they seem to be now going after those that hold certain secrets on the "underground" level of the internet. Which many are not aware of. There are many "telecom" companies that have decided to jump the "we will hand what ever you want over" train in order to avoid prosecution or interruption of their services.
Though we have found an outlet in our own little worlds on the World Wide Web, the seem to have noticed that we cannot be stopped on certain levels, the have now got their eyes set on the core of what we seem to treasure the most. Freedom of expression, and the wanting of knowledge, beyond their indoctrination.
Peace, NRE.
BTW, there is more to come.
edit on 27-5-2012 by NoRegretsEver because: fixing
Wahhh more job for us.
Now we have to make rick roll vids and spread it to the underground internet.
(Thinking of making Rick Roll movie, then renaming it every day) Need to fill up that wintillion space fast.
Also its nice to see the machine cracking my movie list - encrypted of course.
I love this, free computing power! Here, crack this for starter
ouYr mmo sscuk.
Now we have to make rick roll vids and spread it to the underground internet.
(Thinking of making Rick Roll movie, then renaming it every day) Need to fill up that wintillion space fast.
Also its nice to see the machine cracking my movie list - encrypted of course.
I love this, free computing power! Here, crack this for starter
ouYr mmo sscuk.
Here are a few lets call them "computers" that are currently being used in these types of facilities.
Here is the now outdated Jaguar.

And here is the next that followed. Cray XT5

en.wikipedia.org...
I may have put that in order backwards, but what does it matter? This is the newest. Codename: Titan.
en.wikipedia.org...
BTW, there is a list of the top 500 Supercomputers, so go figure
Here is the latest #1 pick straight from Japan. “K Computer”

www.top500.org...
Peace, NRE.
Here is the now outdated Jaguar.

en.wikipedia.org...
Jaguar is a petascale supercomputer built by Cray at Oak Ridge National Laboratory (ORNL) in Oak Ridge, Tennessee. The massively parallel Jaguar has a peak performance of just over 1,750 teraflops (1.75 petaflops). It has 224,256 x86-based AMD Opteron processor cores,[2] and operates with a version of Linux called the Cray Linux Environment.[3] Jaguar is a Cray XT5 system, a development from the Cray XT4 supercomputer.
In November 2009 and June 2010, TOP500, the semiannual list of the world's top 500 supercomputers, named Jaguar as the world's fastest computer. In late October 2010, the BBC reported that the Chinese supercomputer Tianhe-1A had taken over the top spot, achieving over 2.5 quadrillion calculations per second, thereby bumping Jaguar to second place. The November 2010 TOP500 list confirmed the new rankings.[4][5]
In 2012 the Jaguar was transformed into Titan by replacing CPUs with GPUs.[6][7][8]
And here is the next that followed. Cray XT5

The Cray XT5 is an updated version of the Cray XT4 supercomputer, launched on November 6, 2007. It includes a faster version of the XT4's SeaStar2 interconnect router called SeaStar2+, and can be configured either with XT4 compute blades, which have four dual-core AMD Opteron processor sockets, or XT5 blades, with eight sockets supporting dual or quad-core Opterons. The XT5 uses a 3-dimensional torus network topology.
The XT5 family run the Cray Linux Environment, formerly known as UNICOS/lc.[1] This incorporates SUSE Linux Enterprise Server and Cray's Compute Node Linux.
The XT5h (hybrid) variant also includes support for Cray X2 vector processor blades, and Cray XR1 blades which combine Opterons with FPGA-based Reconfigurable Processor Units (RPUs) provided by DRC Computer Corporation.
The XT5m variant is a mid-ranged supercomputer with most of the features of the XT5, but having a 2-dimensional torus network topology and scalable to 6 cabinets.
en.wikipedia.org...
I may have put that in order backwards, but what does it matter? This is the newest. Codename: Titan.
The Cray XK6 is an enhanced version of the Cray XE6 supercomputer, announced in May 2011.[1] The XK6 uses the same "blade" architecture of the XE6, with each XK6 blade comprising four compute "nodes". Each node consists of a 16-core AMD Opteron 6200 processor with 16 or 32 GB of DDR3 RAM and an Nvidia Tesla X2090 GPGPU with 6 GB of GDDR5 RAM, the two connected via PCI Express 2.0.[2] Two Gemini router ASICs are shared between the nodes on a blade, providing a 3-dimensional torus network topology between nodes.
An XK6 cabinet accommodates 24 blades (96 nodes). Each of the Tesla processors is rated at 665 double-precision gigaflops giving 63.8 teraflops per cabinet. The XK6 is capable of scaling to 500,000 Opteron cores, giving up to 50 petaflops total hybrid peak performance.[2]
The XK6 runs the Cray Linux Environment. This incorporates SUSE Linux Enterprise Server and Cray's Compute Node Linux.
The first order for an XK6 system was an upgrade of an existing XE6m at the Swiss National Supercomputing Centre (CSCS).
en.wikipedia.org...
BTW, there is a list of the top 500 Supercomputers, so go figure
Here is the latest #1 pick straight from Japan. “K Computer”

Japan’s “K Computer” maintained its position atop the newest edition of the TOP500 List of the world’s most powerful supercomputers, thanks to a full build-out that makes it four times as powerful as its nearest competitor. Installed at the RIKEN Advanced Institute for Computational Science (AICS) in Kobe, Japan, the K Computer it achieved an impressive 10.51 Petaflop/s on the Linpack benchmark using 705,024 SPARC64 processing cores.
www.top500.org...
Peace, NRE.
AMD Opteron processor cores,,,,,
SPARC64 processing cores.
cool way too go SUN,,standford uni,,,,,still?
cool
SPARC64 processing cores.
cool way too go SUN,,standford uni,,,,,still?
cool
edit on 27-5-2012 by BobAthome because: (no reason given)
All will be, are, but infinitesimal powered child's playgrounds against the Master of space-time that comes quickly.
Honestly non of this surprises me in the least. However I had no clue about this facility. S&F thanks for bringing it to our attention. Very
interesting .
Anything that large will be completely unable to act on any given information until it's too late. But meanwhile, they'll suck up tax money we/they
don't have.
Watch what happens when a couple billion teenage hackers decide to confound and confuse them.
Watch what happens when a couple billion teenage hackers decide to confound and confuse them.
Booking my seat, this is some valuable information to bring to the attention of those too gullable to know the truth.
Thank you for posting OP, I would S&F if I could.
Posted Via ATS Mobile: m.abovetopsecret.com
Thank you for posting OP, I would S&F if I could.
OP. thank you. I am both impressed and grateful that you took the trouble to share all that detail. I do however, have one question. These beasts can
only beat me if I play in their domain.
Should I be scared? Can they sing? Can they dance? Can they write a poem?
Still, thank you; it was a good post.
Should I be scared? Can they sing? Can they dance? Can they write a poem?
Still, thank you; it was a good post.
A good investment, will no doubt be for other undisclosed purposes to,
Are evil people...that scared? These people can't find anything BETTER to do with their time and money? Instead of building super-computers....how
about finding a cure for cancer? Now THAT would be money well spent!
About time someone posted this
I read it in a magazine last month and forgot to put it up. I'm glad you did though.
In fact, that is the magazine
I read it in a magazine last month and forgot to put it up. I'm glad you did though.
In fact, that is the magazine
edit on 28-5-2012 by daaskapital because: (no reason given)
What a huge waster of taxpayers resources. All in the name of NS? I think there would be other reasons to have such vast computational power.
I would love to find a backdoor into that network. Prolly wind up in jail though.
I would love to find a backdoor into that network. Prolly wind up in jail though.
S & F. Thanks for posting this valuable info. We need to know this stuff.
Two things:
1. It is massive futuristic projects (possibly for the doom of eventual complete control of mankind?) that just makes all the coming doom threads fall to the ground. The underground bunkers and seed banks, built for "their protection and survival" if whatever they want us to believe that is going to happen happens, just does not make sense in the face of this billion dollar project.
Just trying to make sense of the madness of the paradox/controversy of these two developments. One under ground and the other above ground, but in my opinion, not above board.
2. Am I alone in thinking that this thing has way greater capacity than what is known even in this Opening Thread? Why do I have a feeling of horror at the possibility that the RFID chips, now starting to take off in US schools, and this massive project may possibly go hand in hand? Is this the coming of the beast, the absolute control over mankind, that makes me feel sick to my stomack, or am I seeing things that are not there?
Somehow, I think my gut feeling may not be far off.
Two things:
1. It is massive futuristic projects (possibly for the doom of eventual complete control of mankind?) that just makes all the coming doom threads fall to the ground. The underground bunkers and seed banks, built for "their protection and survival" if whatever they want us to believe that is going to happen happens, just does not make sense in the face of this billion dollar project.
Just trying to make sense of the madness of the paradox/controversy of these two developments. One under ground and the other above ground, but in my opinion, not above board.
2. Am I alone in thinking that this thing has way greater capacity than what is known even in this Opening Thread? Why do I have a feeling of horror at the possibility that the RFID chips, now starting to take off in US schools, and this massive project may possibly go hand in hand? Is this the coming of the beast, the absolute control over mankind, that makes me feel sick to my stomack, or am I seeing things that are not there?
Somehow, I think my gut feeling may not be far off.
I always wonder at the research skills of our ATS members that they are able to get all this super secret information and post it here in the internet
for the whole world to see. Good job.
Or not
how if this is so super secret are we even talking about it ????
Or not
how if this is so super secret are we even talking about it ????
reply to post by UnlimitedSky
Who takes care of them and all the grunt work if all the common men are gone? The elites become the grunts in any scenario where mankind is eradicated. To what group of people does this make sense ? Not me but I am often alone in my viewpoints.
Who takes care of them and all the grunt work if all the common men are gone? The elites become the grunts in any scenario where mankind is eradicated. To what group of people does this make sense ? Not me but I am often alone in my viewpoints.
Originally posted by TritonTaranis
A good investment, will no doubt be for other undisclosed purposes to,
There's a reason they call private industry private.
reply to post by karen61057
Theres no way they could hide something of that size/cost and the real magic is what goes on inside
Theres no way they could hide something of that size/cost and the real magic is what goes on inside
new topics
-
America's Greatest Ally
General Chit Chat: 29 minutes ago -
President BIDEN's FBI Raided Donald Trump's Florida Home for OBAMA-NORTH KOREA Documents.
Political Conspiracies: 5 hours ago -
Maestro Benedetto
Literature: 7 hours ago -
Is AI Better Than the Hollywood Elite?
Movies: 7 hours ago -
Las Vegas UFO Spotting Teen Traumatized by Demon Creature in Backyard
Aliens and UFOs: 10 hours ago -
2024 Pigeon Forge Rod Run - On the Strip (Video made for you)
Automotive Discussion: 11 hours ago -
Gaza Terrorists Attack US Humanitarian Pier During Construction
Middle East Issues: 11 hours ago
top topics
-
President BIDEN's FBI Raided Donald Trump's Florida Home for OBAMA-NORTH KOREA Documents.
Political Conspiracies: 5 hours ago, 26 flags -
Krystalnacht on today's most elite Universities?
Social Issues and Civil Unrest: 16 hours ago, 9 flags -
Gaza Terrorists Attack US Humanitarian Pier During Construction
Middle East Issues: 11 hours ago, 8 flags -
Supreme Court Oral Arguments 4.25.2024 - Are PRESIDENTS IMMUNE From Later Being Prosecuted.
Above Politics: 16 hours ago, 8 flags -
Weinstein's conviction overturned
Mainstream News: 15 hours ago, 8 flags -
Massachusetts Drag Queen Leads Young Kids in Free Palestine Chant
Social Issues and Civil Unrest: 13 hours ago, 7 flags -
Las Vegas UFO Spotting Teen Traumatized by Demon Creature in Backyard
Aliens and UFOs: 10 hours ago, 6 flags -
Meadows, Giuliani Among 11 Indicted in Arizona in Latest 2020 Election Subversion Case
Mainstream News: 13 hours ago, 5 flags -
2024 Pigeon Forge Rod Run - On the Strip (Video made for you)
Automotive Discussion: 11 hours ago, 4 flags -
Is AI Better Than the Hollywood Elite?
Movies: 7 hours ago, 3 flags
active topics
-
Gaza Terrorists Attack US Humanitarian Pier During Construction
Middle East Issues • 30 • : Asher47 -
Electrical tricks for saving money
Education and Media • 8 • : anned1 -
Is AI Better Than the Hollywood Elite?
Movies • 16 • : 5thHead -
Hate makes for strange bedfellows
US Political Madness • 48 • : Terpene -
America's Greatest Ally
General Chit Chat • 0 • : 19Bones79 -
President BIDEN's FBI Raided Donald Trump's Florida Home for OBAMA-NORTH KOREA Documents.
Political Conspiracies • 17 • : BingoMcGoof -
Supreme Court Oral Arguments 4.25.2024 - Are PRESIDENTS IMMUNE From Later Being Prosecuted.
Above Politics • 90 • : Lumenari -
Las Vegas UFO Spotting Teen Traumatized by Demon Creature in Backyard
Aliens and UFOs • 12 • : KrustyKrab -
SHORT STORY WRITERS CONTEST -- April 2024 -- TIME -- TIME2024
Short Stories • 23 • : DontTreadOnMe -
Truth Social goes public, be careful not to lose your money
Mainstream News • 130 • : Astyanax
