It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
share:
Here we go again! Wikileaks releases "Hive"
Vault 7, Wikileaks releases "Hive"
https://__._/vault7/#Hive
https://__._/vault7/document/hive-UsersGuide/
(fill the blanks with "wikileaks" and "org"
Today, April 14th 2017, WikiLeaks publishes six documents from the CIA's HIVE project created by its "Embedded Development Branch" (EDB).
HIVE is a back-end infrastructure malware with a public-facing HTTPS interface which is used by CIA implants to transfer exfiltrated information from target machines to the CIA and to receive commands from its operators to execute specific tasks on the targets. HIVE is used across multiple malware implants and CIA operations. The public HTTPS interface utilizes unsuspicious-looking cover domains to hide its presence.
Anti-Virus companies and forensic experts have noticed that some possible state-actor malware used such kind of back-end infrastructure by analyzing the communication behaviour of these specific implants, but were unable to attribute the back-end (and therefore the implant itself) to operations run by the CIA. In a recent blog post by Symantec, that was able to attribute the "Longhorn" activities to the CIA based on the Vault 7, such back-end infrastructure is described:
"For C&C servers, Longhorn typically configures a specific domain and IP address combination per target. The domains appear to be registered by the attackers; however they use privacy services to hide their real identity. The IP addresses are typically owned by legitimate companies offering virtual private server (VPS) or webhosting services. The malware communicates with C&C servers over HTTPS using a custom underlying cryptographic protocol to protect communications from identification."
The documents from this publication might further enable anti-malware researchers and forensic experts to analyse this kind of communication between malware implants and back-end servers used in previous illegal activities.
-----------------------
Let me know what you think about it, if somebody has enough time to dig through the user guides and documents posted on Wikileaks' website, please share any details!
Cheers.
Hive, the latest batch of WikiLeaks documents exposing alleged CIA hacking techniques from ‘Vault 7’, details how the agency can monitor its targets through the use of malware and carry out specific tasks on targeted machines.
Described as a multi-platform malware suite, Hive provides “customisable implants” for Windows, Solaris, MikroTik (used in Internet routers), Linux platforms, and AVTech Network Video Recorders, used for CCTV recording. Such implants allow the CIA to communicate specific commands.
Vault 7, Wikileaks releases "Hive"
https://__._/vault7/#Hive
https://__._/vault7/document/hive-UsersGuide/
(fill the blanks with "wikileaks" and "org"
Today, April 14th 2017, WikiLeaks publishes six documents from the CIA's HIVE project created by its "Embedded Development Branch" (EDB).
HIVE is a back-end infrastructure malware with a public-facing HTTPS interface which is used by CIA implants to transfer exfiltrated information from target machines to the CIA and to receive commands from its operators to execute specific tasks on the targets. HIVE is used across multiple malware implants and CIA operations. The public HTTPS interface utilizes unsuspicious-looking cover domains to hide its presence.
Anti-Virus companies and forensic experts have noticed that some possible state-actor malware used such kind of back-end infrastructure by analyzing the communication behaviour of these specific implants, but were unable to attribute the back-end (and therefore the implant itself) to operations run by the CIA. In a recent blog post by Symantec, that was able to attribute the "Longhorn" activities to the CIA based on the Vault 7, such back-end infrastructure is described:
"For C&C servers, Longhorn typically configures a specific domain and IP address combination per target. The domains appear to be registered by the attackers; however they use privacy services to hide their real identity. The IP addresses are typically owned by legitimate companies offering virtual private server (VPS) or webhosting services. The malware communicates with C&C servers over HTTPS using a custom underlying cryptographic protocol to protect communications from identification."
The documents from this publication might further enable anti-malware researchers and forensic experts to analyse this kind of communication between malware implants and back-end servers used in previous illegal activities.
-----------------------
Let me know what you think about it, if somebody has enough time to dig through the user guides and documents posted on Wikileaks' website, please share any details!
Cheers.
edit on 14-4-2017 by Necrose because: (no reason given)
The user guide details the commands that are available, including uploading and deleting files and executing applications on the computer.
To hide the presence of such malware, WikiLeaks notes that the public HTTPS interface (a protocol for secure communication over a computer network within an encrypted connection) “utilizes unsuspicious-looking cover domains,” meaning those targeted would be unaware of the CIA’s interference.
A ‘self-delete’ function is described in documentation accompanying Hive, revealing that the implant destroys itself if it’s not signalled for a predetermined amount of time. Binary information regarding Hive is deleted from the host, leaving a log and configuration file containing only a timestamp.
The self-delete was known to cause issues for the developers after running into complications caused by disparities in system clocks.
To hide the presence of such malware, WikiLeaks notes that the public HTTPS interface (a protocol for secure communication over a computer network within an encrypted connection) “utilizes unsuspicious-looking cover domains,” meaning those targeted would be unaware of the CIA’s interference.
A ‘self-delete’ function is described in documentation accompanying Hive, revealing that the implant destroys itself if it’s not signalled for a predetermined amount of time. Binary information regarding Hive is deleted from the host, leaving a log and configuration file containing only a timestamp.
The self-delete was known to cause issues for the developers after running into complications caused by disparities in system clocks.
So basically the CIA have established a hive mind network of information gathering/sharing tools that has interfaced itself with modern society and
technology at every facet.. Much, much, much beyond 1984. In fact, this is counterproductive to the CIA as they've been overloaded with information
and data. I suspect they either have an AI or are developing an AI to parse through the information .
I keep waiting on something from these to come out that you just can't ignore.....maybe this time.
Always so much to sift through. Looking for a needle in a hay stack.
Always so much to sift through. Looking for a needle in a hay stack.
a reply to: Necrose
This one is not from Wikileaks but was echoed by their twitter account :
Hackers release files indicating NSA monitored global bank transfers
This one is not from Wikileaks but was echoed by their twitter account :
Hackers release files indicating NSA monitored global bank transfers
Hackers released documents and files on Friday that cybersecurity experts said indicated the U.S. National Security Agency had accessed the SWIFT interbank messaging system, allowing it to monitor money flows among some Middle Eastern and Latin American banks.
The release included computer code that could be adapted by criminals to break into SWIFT servers and monitor messaging activity, said Shane Shook, a cyber security consultant who has helped banks investigate breaches of their SWIFT systems.
The documents and files were released by a group calling themselves The Shadow Brokers. Some of the records bear NSA seals, but Reuters could not confirm their authenticity.
The NSA could not immediately be reached for comment.
a reply to: Necrose
But WikiLeaks is definitely not hostile to the United States. It is purely objective. Just look at all the "leaks" damaging to the FSB, SVR, and good ol' GRU there are on there! It is clearly in no way an instrument of Russian intelligence/agitprop.
But WikiLeaks is definitely not hostile to the United States. It is purely objective. Just look at all the "leaks" damaging to the FSB, SVR, and good ol' GRU there are on there! It is clearly in no way an instrument of Russian intelligence/agitprop.
a reply to: DJW001
If there were hostile to US interests, they wouldn't have published the Syria files.
It is potentially damaging to a government the US regime is trying to overthrow :
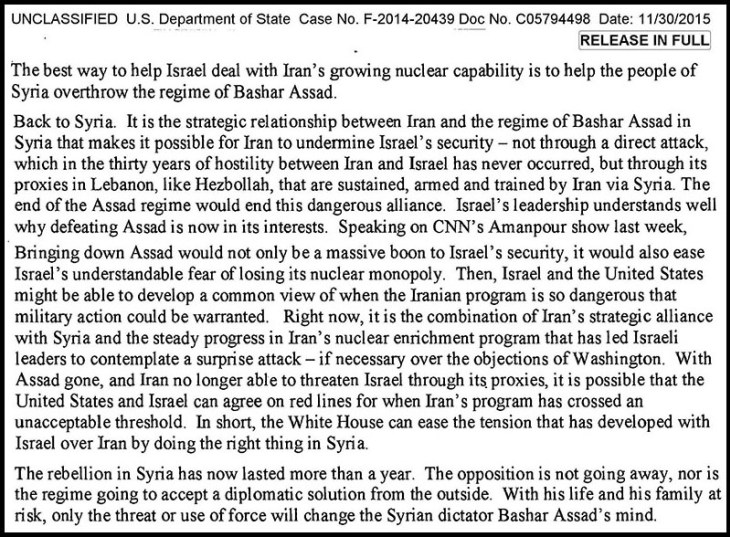
If there were hostile to US interests, they wouldn't have published the Syria files.
It is potentially damaging to a government the US regime is trying to overthrow :
a reply to: theultimatebelgianjoke
Let me know when they publish something "leaked" by Assad's security forces, comrade.
Let me know when they publish something "leaked" by Assad's security forces, comrade.
originally posted by: theultimatebelgianjoke
a reply to: DJW001
It's the US alphabet agencies that are spying on the world, not the Syrian intelligence service.
Assad doesn't have spies? No wonder he needs to kill everybody indiscriminately.
a reply to: theultimatebelgianjoke
The purpose of spies is to inform the decision makers who is a friend and who is an enemy. Fortunately, some people are not afraid to wear their enmity on their sleeve.
I didn't know the purpose of spies was to kill people.
The purpose of spies is to inform the decision makers who is a friend and who is an enemy. Fortunately, some people are not afraid to wear their enmity on their sleeve.
originally posted by: theultimatebelgianjoke
a reply to: DJW001
Figuring out who is an enemy or a friend ?
Assange/Wikileaks is now regarded by Pompeo as an enemy, do you agree with him ?
I have been saying that WikiLeaks is a Russian asset even before Pompeo said it. It was one of the many ways the Russians tried to influence the elections. You know I was saying that at the time.
Antivirus software vendors are now beginning to publish their first papers about the viruses released in the wild by the CIA :
Longhorn: Tools used by cyberespionage group linked to Vault 7 (Symantec)
Longhorn: Tools used by cyberespionage group linked to Vault 7 (Symantec)
Spying tools and operational protocols detailed in the recent Vault 7 leak have been used in cyberattacks against at least 40 targets in 16 different countries by a group Symantec calls Longhorn. Symantec has been protecting its customers from Longhorn’s tools for the past three years and has continued to track the group in order to learn more about its tools, tactics, and procedures.
The tools used by Longhorn closely follow development timelines and technical specifications laid out in documents disclosed by WikiLeaks. The Longhorn group shares some of the same cryptographic protocols specified in the Vault 7 documents, in addition to following leaked guidelines on tactics to avoid detection. Given the close similarities between the tools and techniques, there can be little doubt that Longhorn's activities and the Vault 7 documents are the work of the same group.
Who is Longhorn?
Longhorn has been active since at least 2011. It has used a range of back door Trojans in addition to zero-day vulnerabilities to compromise its targets. Longhorn has infiltrated governments and internationally operating organizations, in addition to targets in the financial, telecoms, energy, aerospace, information technology, education, and natural resources sectors. All of the organizations targeted would be of interest to a nation-state attacker.
Longhorn has infected 40 targets in at least 16 countries across the Middle East, Europe, Asia, and Africa. On one occasion a computer in the United States was compromised but, following infection, an uninstaller was launched within hours, which may indicate this victim was infected unintentionally.
a reply to: theultimatebelgianjoke
Why? Did I say that WikiLeaks should be banned or suppressed? They are free to publish anything they want. The fact that they only seem to publish information damaging to the United States is what makes them so useful to Russia. You, on the other hand, seem to admire all things totalitarian... except Israel, of course.
You are now officially aligned behind the GOP against the first amendment.
Why? Did I say that WikiLeaks should be banned or suppressed? They are free to publish anything they want. The fact that they only seem to publish information damaging to the United States is what makes them so useful to Russia. You, on the other hand, seem to admire all things totalitarian... except Israel, of course.
a reply to: DJW001
Any ambition to bring your deep-state damage-control operation back on topic ?
They didn't really publish anything embarassing from Israel or North Korea either.
Maybe it's just because the Russians and the Israelis are better at securing their IT systems.
The NKoreans are probably, due to their state of isolation, more likely to make use of in-house proprietary systems more difficult to breach.
But still, it is not as if someone 'broke into the CIA', it was more likely an insider leak.
Any ambition to bring your deep-state damage-control operation back on topic ?
They didn't really publish anything embarassing from Israel or North Korea either.
Maybe it's just because the Russians and the Israelis are better at securing their IT systems.
The NKoreans are probably, due to their state of isolation, more likely to make use of in-house proprietary systems more difficult to breach.
But still, it is not as if someone 'broke into the CIA', it was more likely an insider leak.
edit on 17-4-2017 by theultimatebelgianjoke because: -
a reply to: theultimatebelgianjoke
Thanks for that link. Wow, without making direct accusations they have proven it beyond a reasonable doubt. Knowing where and when they worked based on the leaked documents. I'm glad connections are being made and idly wait to see what happens next.
Thanks for that link. Wow, without making direct accusations they have proven it beyond a reasonable doubt. Knowing where and when they worked based on the leaked documents. I'm glad connections are being made and idly wait to see what happens next.
new topics
-
Where should Trump hold his next rally
2024 Elections: 1 hours ago -
Shocking Number of Voters are Open to Committing Election Fraud
US Political Madness: 1 hours ago -
Gov Kristi Noem Shot and Killed "Less Than Worthless Dog" and a 'Smelly Goat
2024 Elections: 2 hours ago -
Falkville Robot-Man
Aliens and UFOs: 2 hours ago -
James O’Keefe: I have evidence that exposes the CIA, and it’s on camera.
Whistle Blowers and Leaked Documents: 3 hours ago -
Australian PM says the quiet part out loud - "free speech is a threat to democratic dicourse"...?!
New World Order: 4 hours ago -
Ireland VS Globalists
Social Issues and Civil Unrest: 4 hours ago -
Biden "Happy To Debate Trump"
2024 Elections: 5 hours ago -
RAAF airbase in Roswell, New Mexico is on fire
Aliens and UFOs: 5 hours ago -
What is the white pill?
Philosophy and Metaphysics: 6 hours ago
top topics
-
A Warning to America: 25 Ways the US is Being Destroyed
New World Order: 15 hours ago, 21 flags -
Blast from the past: ATS Review Podcast, 2006: With All Three Amigos
Member PODcasts: 7 hours ago, 11 flags -
Mike Pinder The Moody Blues R.I.P.
Music: 7 hours ago, 8 flags -
Biden "Happy To Debate Trump"
2024 Elections: 5 hours ago, 8 flags -
James O’Keefe: I have evidence that exposes the CIA, and it’s on camera.
Whistle Blowers and Leaked Documents: 3 hours ago, 7 flags -
Australian PM says the quiet part out loud - "free speech is a threat to democratic dicourse"...?!
New World Order: 4 hours ago, 7 flags -
What is the white pill?
Philosophy and Metaphysics: 6 hours ago, 5 flags -
Ireland VS Globalists
Social Issues and Civil Unrest: 4 hours ago, 4 flags -
RAAF airbase in Roswell, New Mexico is on fire
Aliens and UFOs: 5 hours ago, 4 flags -
Putin, Russia and the Great Architects of the Universe
ATS Skunk Works: 10 hours ago, 3 flags
active topics
-
Candidate TRUMP Now Has Crazy Judge JUAN MERCHAN After Him - The Stormy Daniels Hush-Money Case.
Political Conspiracies • 811 • : Oldcarpy2 -
Shocking Number of Voters are Open to Committing Election Fraud
US Political Madness • 3 • : Disgusted123 -
Meadows, Giuliani Among 11 Indicted in Arizona in Latest 2020 Election Subversion Case
Mainstream News • 28 • : yuppa -
SETI chief says US has no evidence for alien technology. 'And we never have'
Aliens and UFOs • 77 • : yuppa -
Biden "Happy To Debate Trump"
2024 Elections • 39 • : underpass61 -
Where should Trump hold his next rally
2024 Elections • 6 • : WeMustCare -
University of Texas Instantly Shuts Down Anti Israel Protests
Education and Media • 306 • : Xtrozero -
Russia Ukraine Update Thread - part 3
World War Three • 5737 • : Arbitrageur -
Gov Kristi Noem Shot and Killed "Less Than Worthless Dog" and a 'Smelly Goat
2024 Elections • 26 • : CarlLaFong -
James O’Keefe: I have evidence that exposes the CIA, and it’s on camera.
Whistle Blowers and Leaked Documents • 8 • : Athetos