It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
share:
a reply to: aLLeKs
Air-gap PC [offline] are fair game and are not necessarily secure.
Not going to even mention other means that can monitor what you type and what you are doing remotely without physically hacking your PC offline or online. Ok maybe a few:
curiousmatic.com...
If they want to capture data on you they will capture data on you.
The only way to be secure from hacking is being offline.
Air-gap PC [offline] are fair game and are not necessarily secure.
mashable.com...
Traditionally, common belief held that one of the most effective measures against Internet surveillance was to "air-gap" a computer containing sensitive information — or, in plain English, unplug the laptop or computer's Internet connection, isolating it from the outside world. But thanks to these tiny bugs, this protection method isn't foolproof anymore.
Not going to even mention other means that can monitor what you type and what you are doing remotely without physically hacking your PC offline or online. Ok maybe a few:
curiousmatic.com...
If they want to capture data on you they will capture data on you.
edit on 54831America/ChicagoWed, 06 Aug 2014 16:54:40 -0500000000p3142 by interupt42 because: (no reason given)
a reply to: interupt42
unbelievable .. so the only actual way is to just not have a computer I guess or just be .. dead .. or is there some type of hack for that also ? lol .. I'm guessing some time in the future they'll be able to read minds so no one will be safe
unbelievable .. so the only actual way is to just not have a computer I guess or just be .. dead .. or is there some type of hack for that also ? lol .. I'm guessing some time in the future they'll be able to read minds so no one will be safe
a reply to: Stuyvesant
So if you know just how deep surveillance is - I do as well. How can you reasonably say 'we are the ones putting our personal data out there?'
That is simply not true anymore. They can pull absolutely anything and everything from your computer, they can access your webcam, your private files, they can even access protected encrypted information stored on your device.
Many people would like to use their computers for record keeping and they would never ever put said data online - they simply store stuff on their hard drives for accessibility and because let's face it typing # is way easier.
Yet the government still steals this stuff...yes steals....They have gone way beyond crossing the line at this point.
So if you know just how deep surveillance is - I do as well. How can you reasonably say 'we are the ones putting our personal data out there?'
That is simply not true anymore. They can pull absolutely anything and everything from your computer, they can access your webcam, your private files, they can even access protected encrypted information stored on your device.
Many people would like to use their computers for record keeping and they would never ever put said data online - they simply store stuff on their hard drives for accessibility and because let's face it typing # is way easier.
Yet the government still steals this stuff...yes steals....They have gone way beyond crossing the line at this point.
a reply to: kranskik
Ok here is how to beat this lol when ever you use tor you use it on a virtual machine running a different operating system. Virus is down loaded to a sand box os.
That can be recovered and will not have admin privlages on your actual os. Best of luck to the new tor users you can also get it on your andriod or apple phone its called orbot and orweb. all this does is catch people new to tor dont forget to use proxy chains on your scanner or apps as they will give up your actual ip address.
The reason a virtual machine will work is because the virus will stay on the virtual machine and only be able to access the vms files. Few viruses can infect two diffrent operating systems. You can get vmware or virtual box then get the iso for linux or apple or windows and mount it to the vmware or virtual box
Ok here is how to beat this lol when ever you use tor you use it on a virtual machine running a different operating system. Virus is down loaded to a sand box os.
That can be recovered and will not have admin privlages on your actual os. Best of luck to the new tor users you can also get it on your andriod or apple phone its called orbot and orweb. all this does is catch people new to tor dont forget to use proxy chains on your scanner or apps as they will give up your actual ip address.
The reason a virtual machine will work is because the virus will stay on the virtual machine and only be able to access the vms files. Few viruses can infect two diffrent operating systems. You can get vmware or virtual box then get the iso for linux or apple or windows and mount it to the vmware or virtual box
edit on 6-8-2014 by devious003 because: (no reason given)
originally posted by: dude77
a reply to: interupt42
I'm guessing some time in the future they'll be able to read minds so no one will be safe
They have been working on it for a while .
www.technologyreview.com...
Edward Chang, a neurosurgeon at the University of California, San Francisco, says he is working toward building a wireless brain-machine interface that could translate brain signals directly into audible speech using a voice synthesizer.
And because the Military cares about your mental health .
the Defense Advanced Research Projects Agency, or DARPA, awarded two large contracts to Massachusetts General Hospital and the University of California, San Francisco, to create electrical brain implants capable of treating seven psychiatric conditions, including addiction, depression, and borderline personality disorder.
the development of microlectronic systems that can fit in the body; and substantial evidence that thoughts and actions can be altered with well-placed electrical impulses to the brain.
www.technologyreview.com...
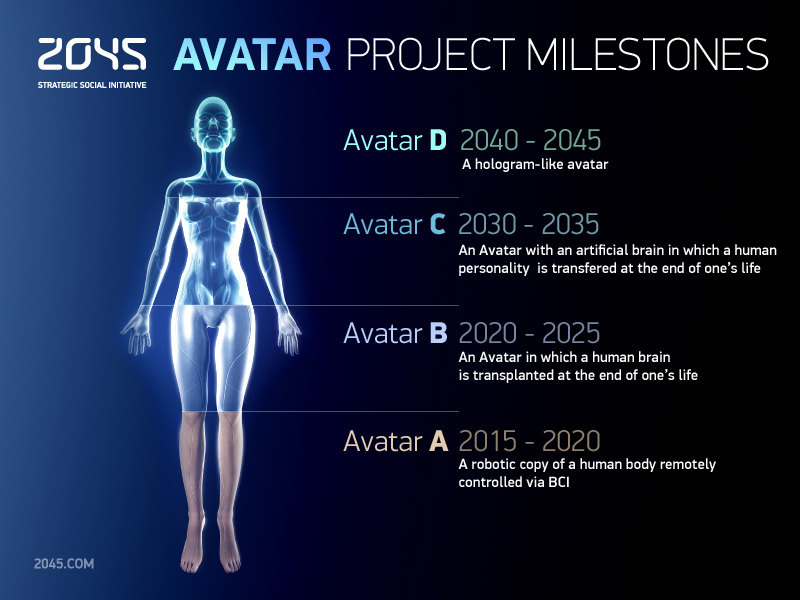
Death for the time being is the sure method or at least till 2030 if a Russian Billionaire gets his way. He hopes to achieve mortality by uploading his brain just before death to a virtual brain or network.
2045.com...
edit on 27831America/ChicagoThu, 07 Aug 2014 08:27:10 -0500000000p3142 by interupt42 because: (no reason given)
a reply to: Stuyvesant
I believe you hit the nail right on the head, good post! Look how easily these hackers get into even highly secure sites, and then think of the average person like you or me on a PC/cell phone/tablet. It's like taking candy from a baby.
Anyone who thinks they are secure online is just kidding themselves. No such thing as security.
I believe you hit the nail right on the head, good post! Look how easily these hackers get into even highly secure sites, and then think of the average person like you or me on a PC/cell phone/tablet. It's like taking candy from a baby.
Anyone who thinks they are secure online is just kidding themselves. No such thing as security.
originally posted by: lightedhype
a reply to: Stuyvesant
So if you know just how deep surveillance is - I do as well. How can you reasonably say 'we are the ones putting our personal data out there?'
That is simply not true anymore. They can pull absolutely anything and everything from your computer, they can access your webcam, your private files, they can even access protected encrypted information stored on your device.
Many people would like to use their computers for record keeping and they would never ever put said data online - they simply store stuff on their hard drives for accessibility and because let's face it typing # is way easier.
Yet the government still steals this stuff...yes steals....They have gone way beyond crossing the line at this point.
I don't disagree with anything you said.
When I said "we are the ones putting our personal data out there" I didn't mean just online, I meant on computers & electronic devices. Even a simple storage device, not hooked up to anything, can be accessed. (At least, I have to make that assumption, based on the tech I have seen.)
Plus, I think we are being conditioned to conduct all business transactions and correspondence through this medium. I believe personal privacy really is a chimera for most people in high-tech environments. Heck, it's probably nearly-nonexistent for people living in rural areas too.
Destroy the computer and go old-school. That's the safe(r) alternative and best option for privacy in these weird times, and every day I think about destroying my computer and actually doing it - but like a lot of people, I have grown used to the ease of it.
originally posted by: devious003
a reply to: kranskik
Ok here is how to beat this lol when ever you use tor you use it on a virtual machine running a different operating system. Virus is down loaded to a sand box os.
That can be recovered and will not have admin privlages on your actual os. Best of luck to the new tor users you can also get it on your andriod or apple phone its called orbot and orweb. all this does is catch people new to tor dont forget to use proxy chains on your scanner or apps as they will give up your actual ip address.
The reason a virtual machine will work is because the virus will stay on the virtual machine and only be able to access the vms files. Few viruses can infect two diffrent operating systems. You can get vmware or virtual box then get the iso for linux or apple or windows and mount it to the vmware or virtual box
If you think you are maintaining any kind of anonymity by using Tor, (even by taking the above-mentioned precautions) I think you are horribly mistaken. The authorities have focused attention on Tor and Tor users, so use extreme caution when you think you want to 'try' being anonymous on the web. It raises red flags. Just $0.02 from a paranoid conspiracy theorist who doesn't know anything about computers and surveillance.
a reply to: Stuyvesant
I have a degree in information security. I know alot about the subject matter it took me 4 years and countless hours researching the subject. Hiding an ip address is only part of it.
I have a degree in information security. I know alot about the subject matter it took me 4 years and countless hours researching the subject. Hiding an ip address is only part of it.
new topics
-
BIDEN Admin Begins Planning For January 2025 Transition to a New President - Today is 4.26.2024.
2024 Elections: 3 hours ago -
Big Storms
Fragile Earth: 5 hours ago -
Where should Trump hold his next rally
2024 Elections: 7 hours ago -
Shocking Number of Voters are Open to Committing Election Fraud
US Political Madness: 8 hours ago -
Gov Kristi Noem Shot and Killed "Less Than Worthless Dog" and a 'Smelly Goat
2024 Elections: 9 hours ago -
Falkville Robot-Man
Aliens and UFOs: 9 hours ago -
James O’Keefe: I have evidence that exposes the CIA, and it’s on camera.
Whistle Blowers and Leaked Documents: 10 hours ago -
Australian PM says the quiet part out loud - "free speech is a threat to democratic dicourse"...?!
New World Order: 10 hours ago -
Ireland VS Globalists
Social Issues and Civil Unrest: 11 hours ago -
Biden "Happy To Debate Trump"
2024 Elections: 11 hours ago
top topics
-
James O’Keefe: I have evidence that exposes the CIA, and it’s on camera.
Whistle Blowers and Leaked Documents: 10 hours ago, 17 flags -
Australian PM says the quiet part out loud - "free speech is a threat to democratic dicourse"...?!
New World Order: 10 hours ago, 15 flags -
Blast from the past: ATS Review Podcast, 2006: With All Three Amigos
Member PODcasts: 14 hours ago, 13 flags -
Biden "Happy To Debate Trump"
2024 Elections: 11 hours ago, 13 flags -
Ireland VS Globalists
Social Issues and Civil Unrest: 11 hours ago, 9 flags -
Mike Pinder The Moody Blues R.I.P.
Music: 14 hours ago, 8 flags -
BIDEN Admin Begins Planning For January 2025 Transition to a New President - Today is 4.26.2024.
2024 Elections: 3 hours ago, 7 flags -
What is the white pill?
Philosophy and Metaphysics: 13 hours ago, 6 flags -
Shocking Number of Voters are Open to Committing Election Fraud
US Political Madness: 8 hours ago, 6 flags -
Big Storms
Fragile Earth: 5 hours ago, 6 flags
active topics
-
BIDEN Admin Begins Planning For January 2025 Transition to a New President - Today is 4.26.2024.
2024 Elections • 20 • : BustedBoomer -
Gov Kristi Noem Shot and Killed "Less Than Worthless Dog" and a 'Smelly Goat
2024 Elections • 62 • : BustedBoomer -
One Flame Throwing Robot Dog for Christmas Please!
Weaponry • 12 • : worldstarcountry -
RAAF airbase in Roswell, New Mexico is on fire
Aliens and UFOs • 13 • : Ophiuchus1 -
President BIDEN's FBI Raided Donald Trump's Florida Home for OBAMA-NORTH KOREA Documents.
Political Conspiracies • 40 • : BingoMcGoof -
Australian PM says the quiet part out loud - "free speech is a threat to democratic dicourse"...?!
New World Order • 7 • : 19Bones79 -
It takes One to Be; Two to Tango; Three to Create.
Philosophy and Metaphysics • 8 • : Compendium -
Big Storms
Fragile Earth • 16 • : rickymouse -
James O’Keefe: I have evidence that exposes the CIA, and it’s on camera.
Whistle Blowers and Leaked Documents • 14 • : 19Bones79 -
A Warning to America: 25 Ways the US is Being Destroyed
New World Order • 29 • : 19Bones79