It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
The Conspiracy Theory Is True: Agents Infiltrate Websites Intending To "Manipulate, Deceive, And De
page: 14
share:
The Conspiracy Theory Is True: Agents Infiltrate Websites Intending To "Manipulate, Deceive, And Destroy Reputations"
The Conspiracy Theory Is True: Agents Infiltrate Websites Intending To "Manipulate, Deceive, And Destroy Reputations"
Shills are real! They walk among us. SHILL GATES ARE REAL!
This article is a real eyefull. It confirms your worst, most paranoid fantasies. The depth and and scope of the operations being played out on the internet are mindboggling. You owe it to yourself to read this...to know what we are all up against.
Many times I have thought accusations of shilling were over-the-top and paranoid. No more! While calling somebody a "shill" is often just an easy, lazy way of shutting down an opposing viewpoint, after reading this I will never doubt that THEY WALK AMONG US.
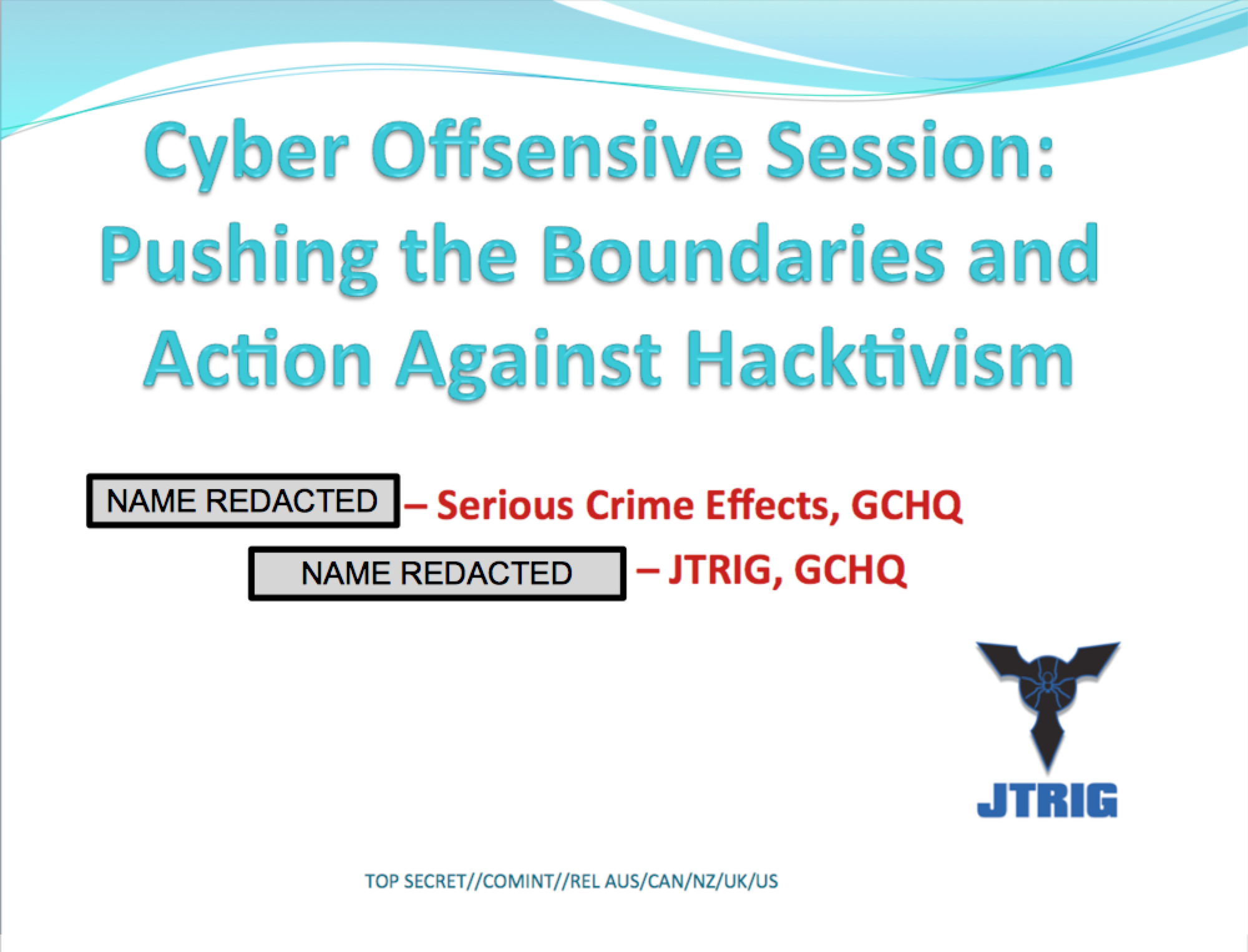
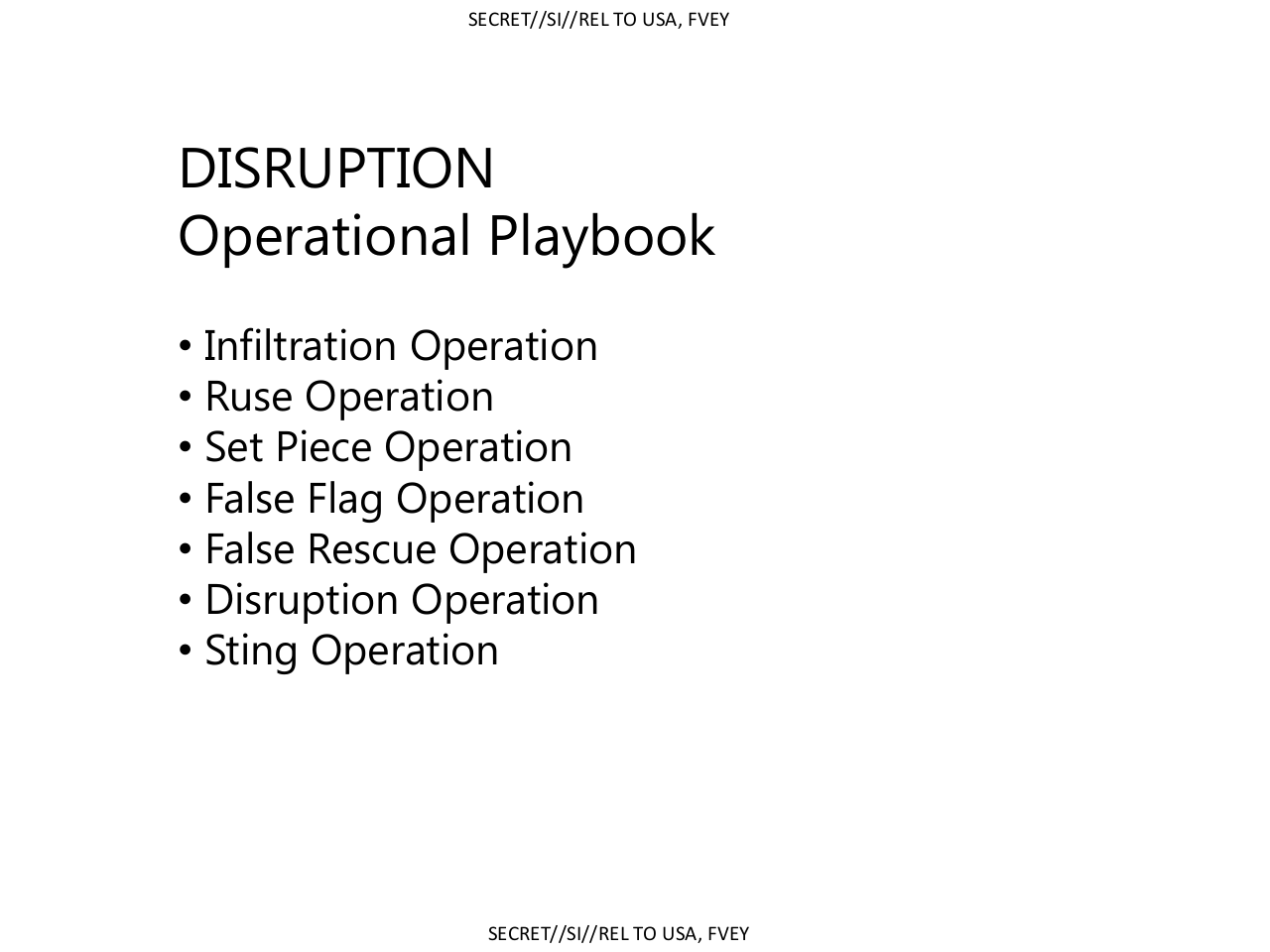
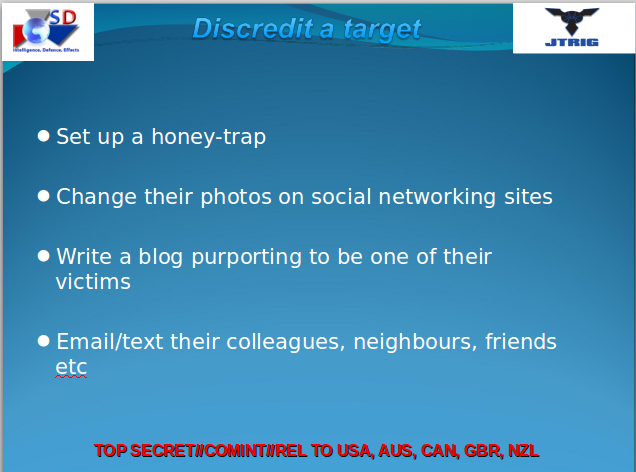
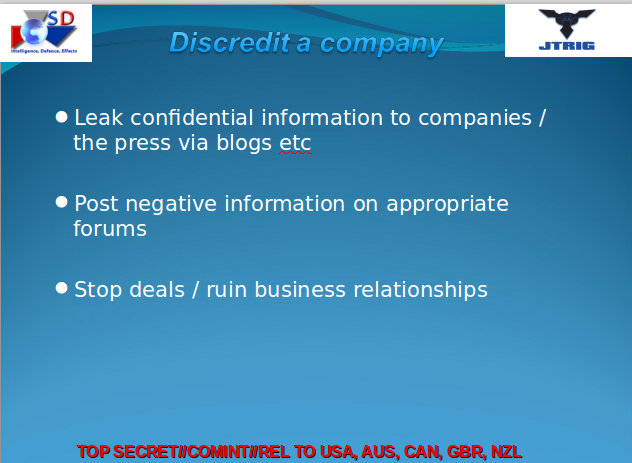
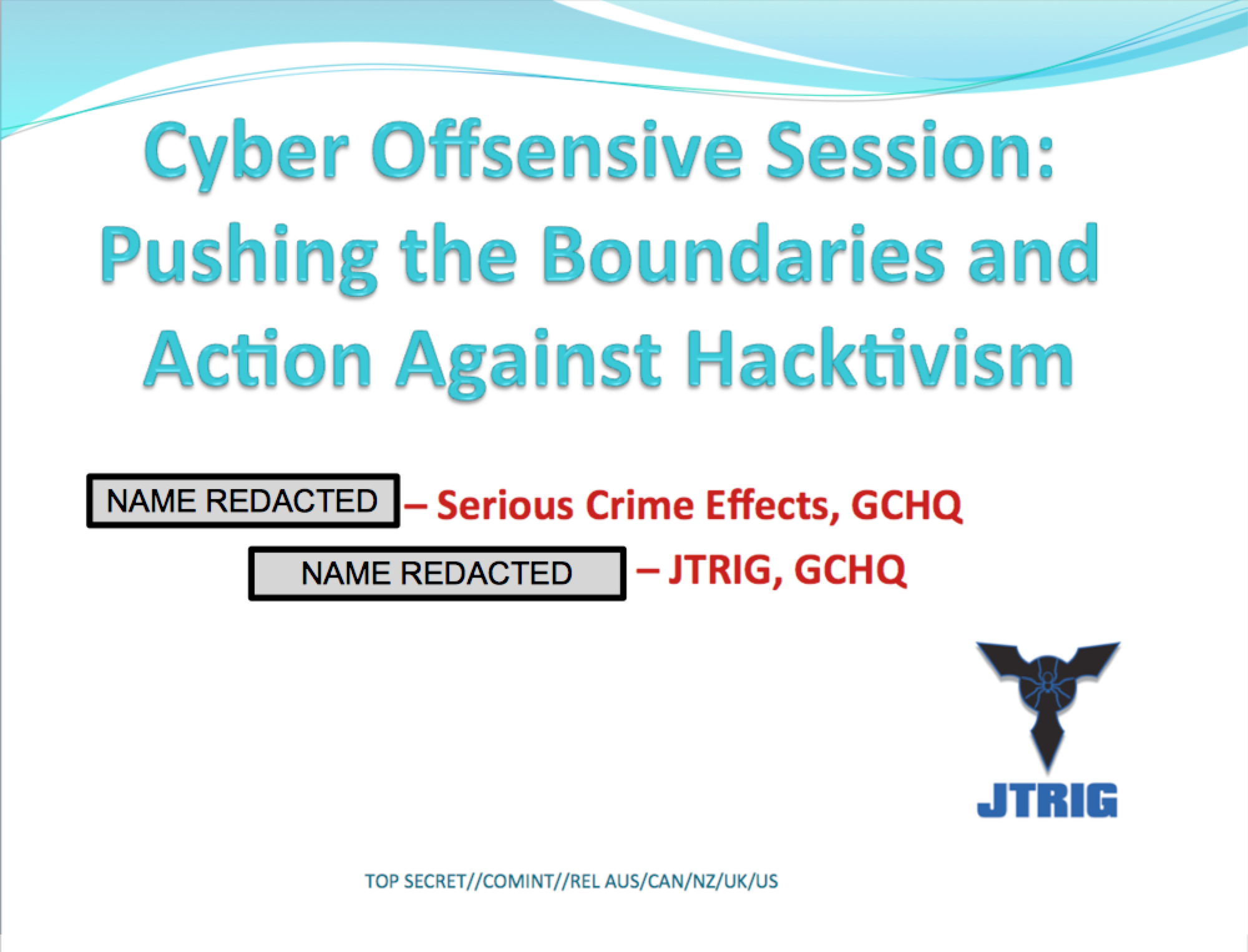
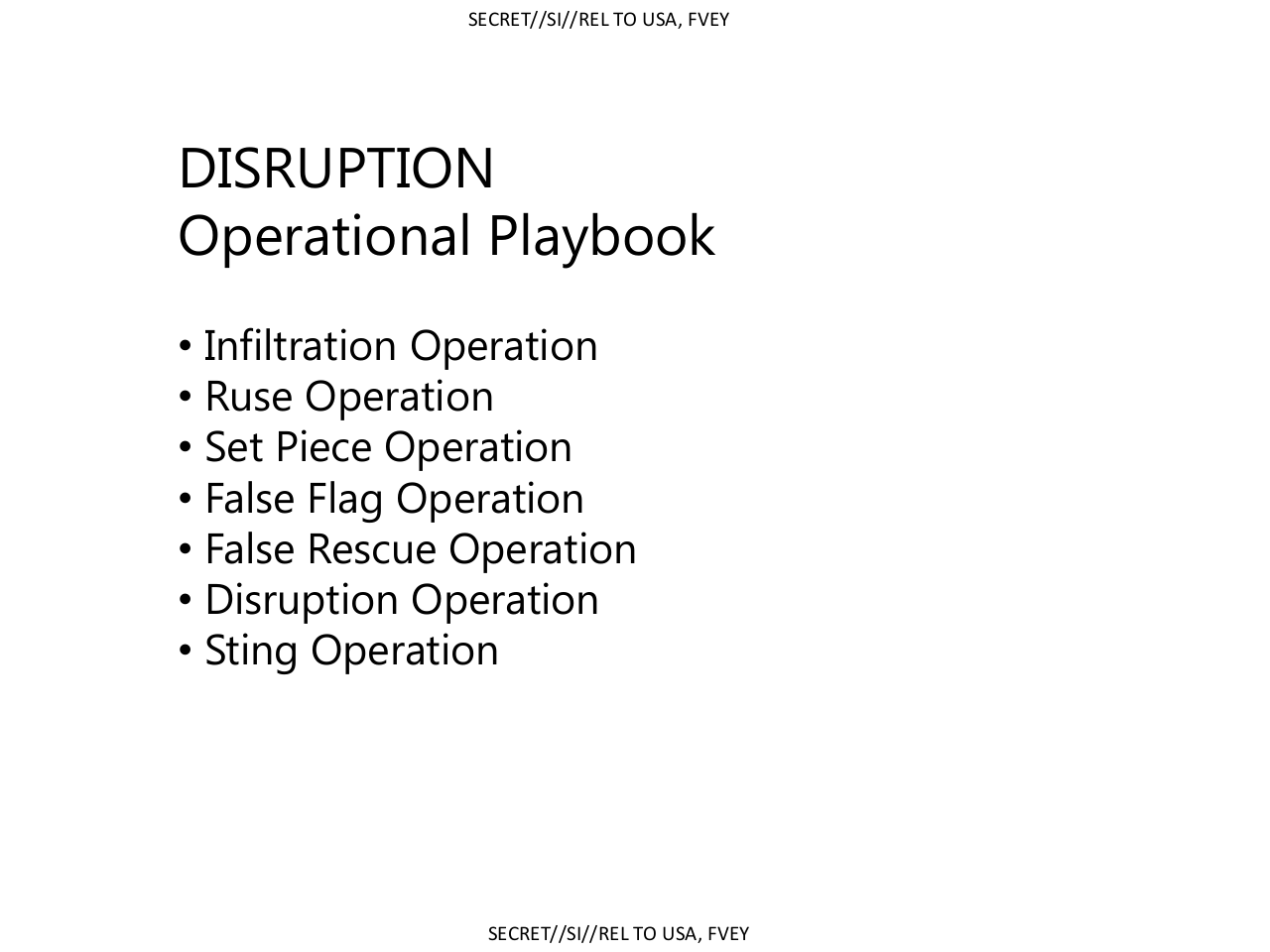
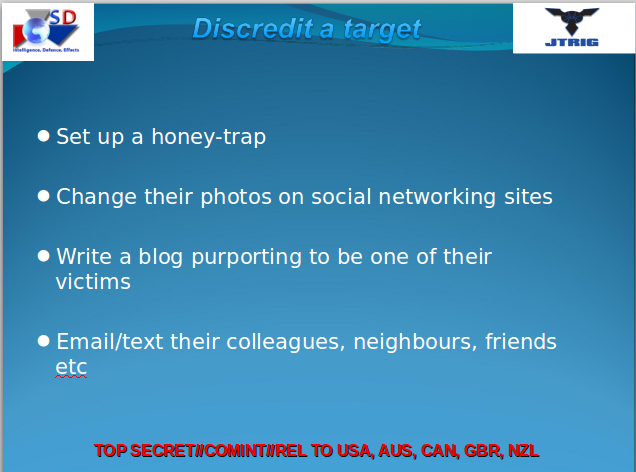
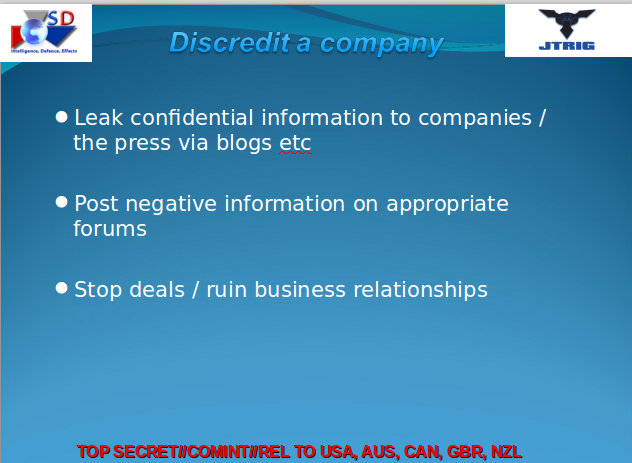
Below are some screenshots from the government-made materials discussed in the article; they give an idea of the operations but are by no means exhaustive.
And I quote...
"..Among the core self-identified purposes of JTRIG are two tactics: (1) to inject all sorts of false material onto the internet in order to destroy the reputation of its targets; and (2) to use social sciences and other techniques to manipulate online discourse and activism to generate outcomes it considers desirable. To see how extremist these programs are, just consider the tactics they boast of using to achieve those ends: “false flag operations” (posting material to the internet and falsely attributing it to someone else), fake victim blog posts (pretending to be a victim of the individual whose reputation they want to destroy), and posting “negative information” on various forums..."
In the annals of internet conspiracy theories, none is more pervasive than the one speculating paid government plants infiltrate websites, social network sites, and comment sections with an intent to sow discord, troll, and generally manipulate, deceive and destroy reputations. Guess what: it was all true.
And this time we have a pretty slideshow of formerly confidential data prepared by the UK NSA equivalent, the GCHQ, to confirm it, and Edward Snowden to thank for disclosing it. The messenger in this case is Glenn Greenwald, [who says]: "... these agencies are attempting to control, infiltrate, manipulate, and warp online discourse, and in doing so, are compromising the integrity of the internet itself."
The Conspiracy Theory Is True: Agents Infiltrate Websites Intending To "Manipulate, Deceive, And Destroy Reputations"
Shills are real! They walk among us. SHILL GATES ARE REAL!
This article is a real eyefull. It confirms your worst, most paranoid fantasies. The depth and and scope of the operations being played out on the internet are mindboggling. You owe it to yourself to read this...to know what we are all up against.
Many times I have thought accusations of shilling were over-the-top and paranoid. No more! While calling somebody a "shill" is often just an easy, lazy way of shutting down an opposing viewpoint, after reading this I will never doubt that THEY WALK AMONG US.
Below are some screenshots from the government-made materials discussed in the article; they give an idea of the operations but are by no means exhaustive.
And I quote...
"..Among the core self-identified purposes of JTRIG are two tactics: (1) to inject all sorts of false material onto the internet in order to destroy the reputation of its targets; and (2) to use social sciences and other techniques to manipulate online discourse and activism to generate outcomes it considers desirable. To see how extremist these programs are, just consider the tactics they boast of using to achieve those ends: “false flag operations” (posting material to the internet and falsely attributing it to someone else), fake victim blog posts (pretending to be a victim of the individual whose reputation they want to destroy), and posting “negative information” on various forums..."
edit on 24-2-2014 by Never Despise because: (no reason given)
reply to post by Never Despise
Sorry minutes too late
Exact thread here...............
www.abovetopsecret.com...
Sorry minutes too late
Exact thread here...............
www.abovetopsecret.com...
edit on 24-2-2014 by maythetruthbeknown because: (no reason given)
maythetruthbeknown
reply to post by Never Despise
Sorry minutes too late
Exact thread here...............
www.abovetopsecret.com...edit on 24-2-2014 by maythetruthbeknown because: (no reason given)
ARRRGH! And I uploaded all those pretty pics, too.
Oh well. great minds think alike and all that. Go ahead and kill this thread.
to bad, nice thread
the subject deserves all the attention it can get
the subject deserves all the attention it can get
Posted earlier here
www.abovetopsecret.com...
Please add further comments to the ongoing discussion in the above linked thread.
Thanks
**Thread Closed**
for future reference:
We Have A New Search Engine--Please Use It!
www.abovetopsecret.com...
Please add further comments to the ongoing discussion in the above linked thread.
Thanks
**Thread Closed**
for future reference:
We Have A New Search Engine--Please Use It!
new topics
-
Are you ready for the return of Jesus Christ? Have you been cleansed by His blood?
Religion, Faith, And Theology: 1 hours ago -
Chronological time line of open source information
History: 2 hours ago -
A man of the people
Diseases and Pandemics: 3 hours ago -
Ramblings on DNA, blood, and Spirit.
Philosophy and Metaphysics: 3 hours ago -
4 plans of US elites to defeat Russia
New World Order: 5 hours ago -
Thousands Of Young Ukrainian Men Trying To Flee The Country To Avoid Conscription And The War
Other Current Events: 8 hours ago -
12 jurors selected in Trump criminal trial
US Political Madness: 11 hours ago -
Iran launches Retalliation Strike 4.18.24
World War Three: 11 hours ago
top topics
-
George Knapp AMA on DI
Area 51 and other Facilities: 17 hours ago, 26 flags -
Israeli Missile Strikes in Iran, Explosions in Syria + Iraq
World War Three: 12 hours ago, 17 flags -
Iran launches Retalliation Strike 4.18.24
World War Three: 11 hours ago, 6 flags -
Thousands Of Young Ukrainian Men Trying To Flee The Country To Avoid Conscription And The War
Other Current Events: 8 hours ago, 6 flags -
12 jurors selected in Trump criminal trial
US Political Madness: 11 hours ago, 4 flags -
Chronological time line of open source information
History: 2 hours ago, 2 flags -
A man of the people
Diseases and Pandemics: 3 hours ago, 2 flags -
4 plans of US elites to defeat Russia
New World Order: 5 hours ago, 2 flags -
Ramblings on DNA, blood, and Spirit.
Philosophy and Metaphysics: 3 hours ago, 1 flags -
Are you ready for the return of Jesus Christ? Have you been cleansed by His blood?
Religion, Faith, And Theology: 1 hours ago, 0 flags
4
