It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
The Conspiracy Theory Is True: Agents Infiltrate Websites Intending To "Manipulate, Deceive, And De
page: 1share:
The Conspiracy Theory Is True: Agents Infiltrate Websites Intending To "Manipulate, Deceive, And Destroy Reputations"
The Conspiracy Theory Is True: Agents Infiltrate Websites Intending To "Manipulate, Deceive, And Destroy Reputations"
Most know, it's no surprise that this is happening, as discussed multiple times on this site. More so now that to show those in doubt or unknowing to the subject.
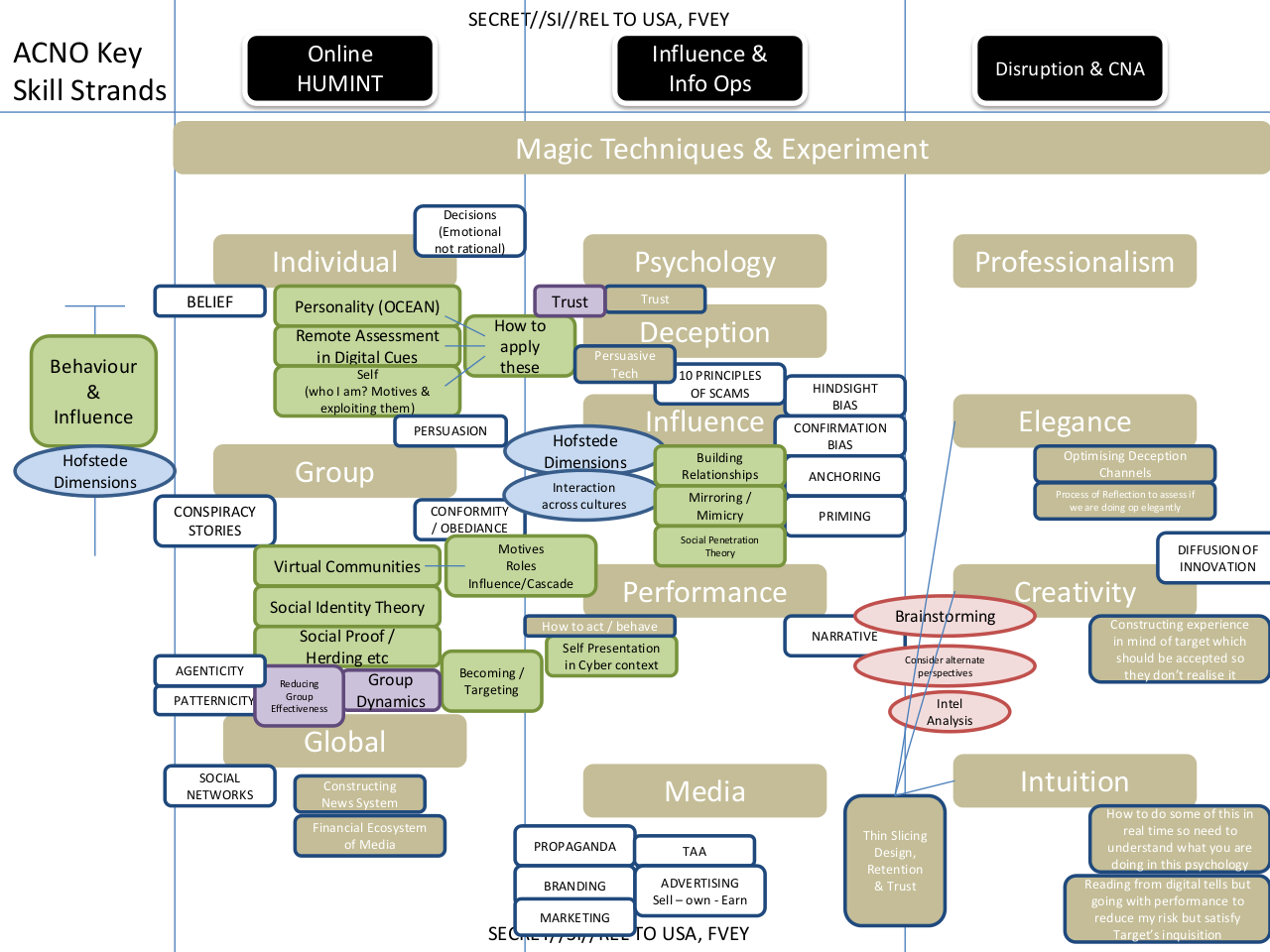
The article's messenger in this case is Glenn Greenwald. Greenwald's new site(see here, "How Covert Agents Infiltrate the Internet to Manipulate, Deceive, and Destroy Reputations") has data, which I will share some of in the following reply posts. This coupled in with the results in action of Comcast's corruption, not just a start, but it's rearing it's ugly head.
There's a war on for our internet, what do you say ATS?
In the annals of internet conspiracy theories, none is more pervasive than the one speculating paid government plants infiltrate websites, social network sites, and comment sections with an intent to sow discord, troll, and generally manipulate, deceive and destroy reputations. Guess what: it was all true.
Continued...
namely, that these agencies are attempting to control, infiltrate, manipulate, and warp online discourse, and in doing so, are compromising the integrity of the internet itself." Call it Stasi for "Generation Internet."
The Conspiracy Theory Is True: Agents Infiltrate Websites Intending To "Manipulate, Deceive, And Destroy Reputations"
Most know, it's no surprise that this is happening, as discussed multiple times on this site. More so now that to show those in doubt or unknowing to the subject.
The article's messenger in this case is Glenn Greenwald. Greenwald's new site(see here, "How Covert Agents Infiltrate the Internet to Manipulate, Deceive, and Destroy Reputations") has data, which I will share some of in the following reply posts. This coupled in with the results in action of Comcast's corruption, not just a start, but it's rearing it's ugly head.
- www.abovetopsecret.com...
The full PDF document can be obtained from scribd for those who want a copy: www.scribd.com...
There's a war on for our internet, what do you say ATS?
edit on 24-2-2014 by dreamingawake because: Full title since it did not
show.
edit on 24-2-2014 by dreamingawake because: more...
edit on 24-2-2014 by dreamingawake because: (no reason
given)
edit on 24-2-2014 by dreamingawake because: Added image.
edit on 24-2-2014 by dreamingawake because: Added PDF
download.
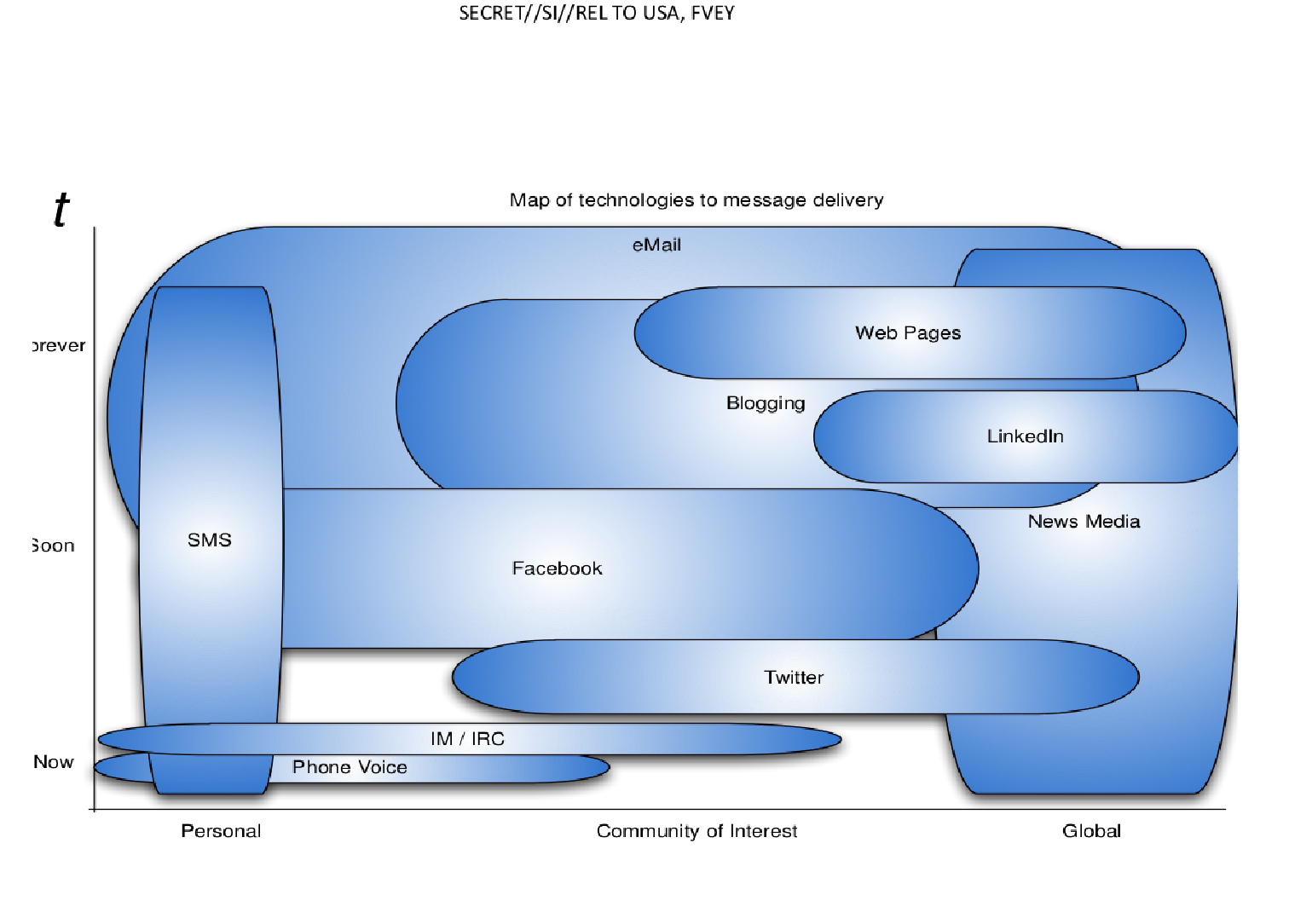
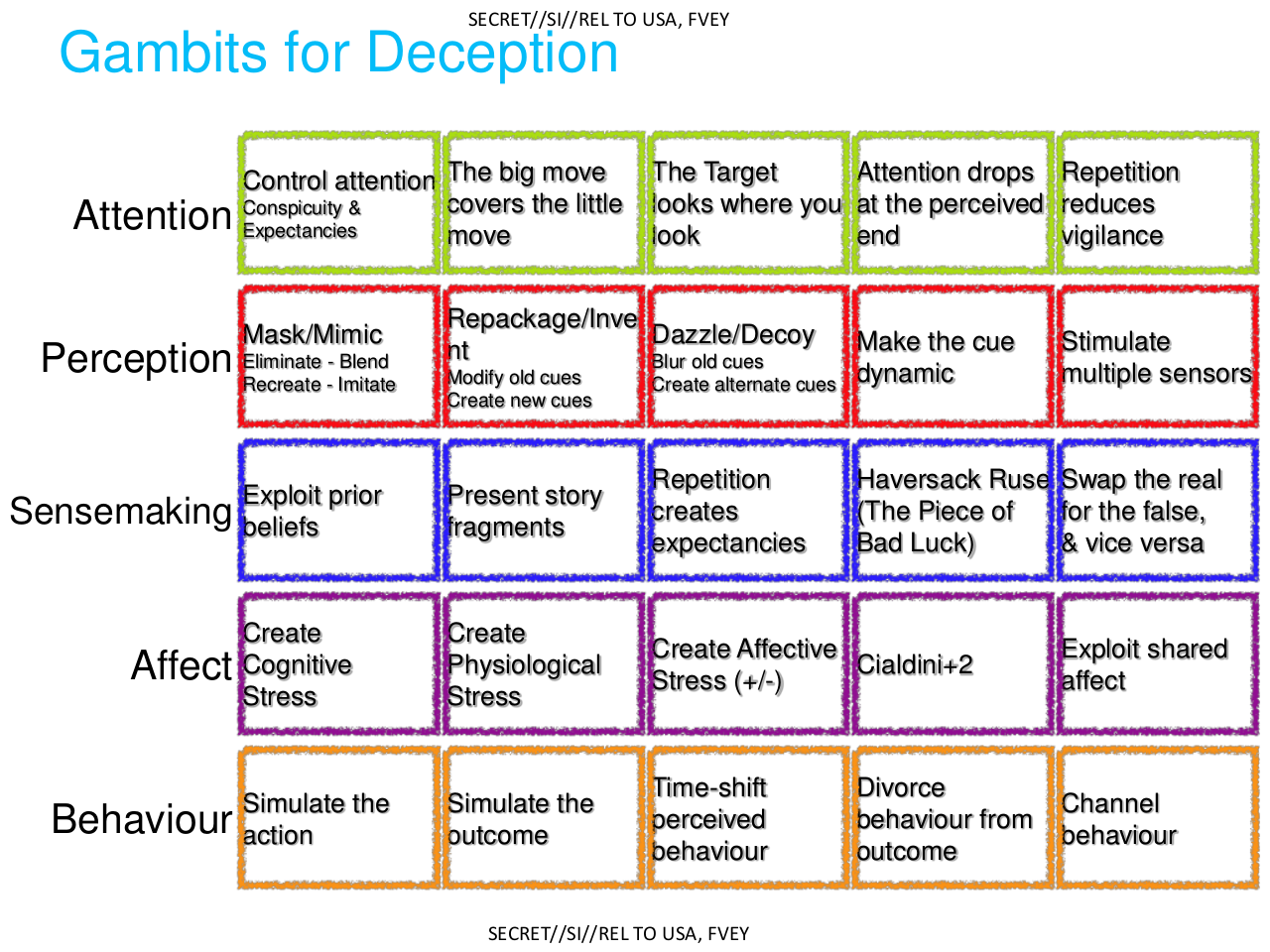
Other tactics aimed at individuals are listed here, under the revealing title “discredit a target”:

Continued...there are many slides, so I'll forward a bit in sharing.
edit on 24-2-2014 by dreamingawake because: more...
More at OP source, please see article descriptions as well.
reply to post by dreamingawake
How'd you get access to those files? You can message me if you're scared to speak on it so openly.
How'd you get access to those files? You can message me if you're scared to speak on it so openly.
reply to post by dreamingawake
I wish I could give you a star and flag but for some reason I am not able to do that. Great thread dreamingawake! I look forward to the rest!
I wish I could give you a star and flag but for some reason I am not able to do that. Great thread dreamingawake! I look forward to the rest!
brazenalderpadrescorpio
reply to post by dreamingawake
How'd you get access to those files? You can message me if you're scared to speak on it so openly.
They are posted to both on Glenn' site and Zero Hedge shared in the OP opening.
Seen your update, no prob.
edit on 24-2-2014 by dreamingawake because: (no reason given)
reply to post by dreamingawake
Nice thread. Guess we all pretty much knew this was true but it's nice to have some evidence on the matter. Now I wonder if you'll get any naysayers pop in here to deny it and call Greenwald a terrorist collaborator or something.
Thanks for the link as well, bookmarking The Intercept.
Nice thread. Guess we all pretty much knew this was true but it's nice to have some evidence on the matter. Now I wonder if you'll get any naysayers pop in here to deny it and call Greenwald a terrorist collaborator or something.
Thanks for the link as well, bookmarking The Intercept.
Bassago
reply to post by dreamingawake
Nice thread. Guess we all pretty much knew this was true but it's nice to have some evidence on the matter. Now I wonder if you'll get any naysayers pop in here to deny it and call Greenwald a terrorist collaborator or something.
Thanks for the link as well, bookmarking The Intercept.
haha YES!
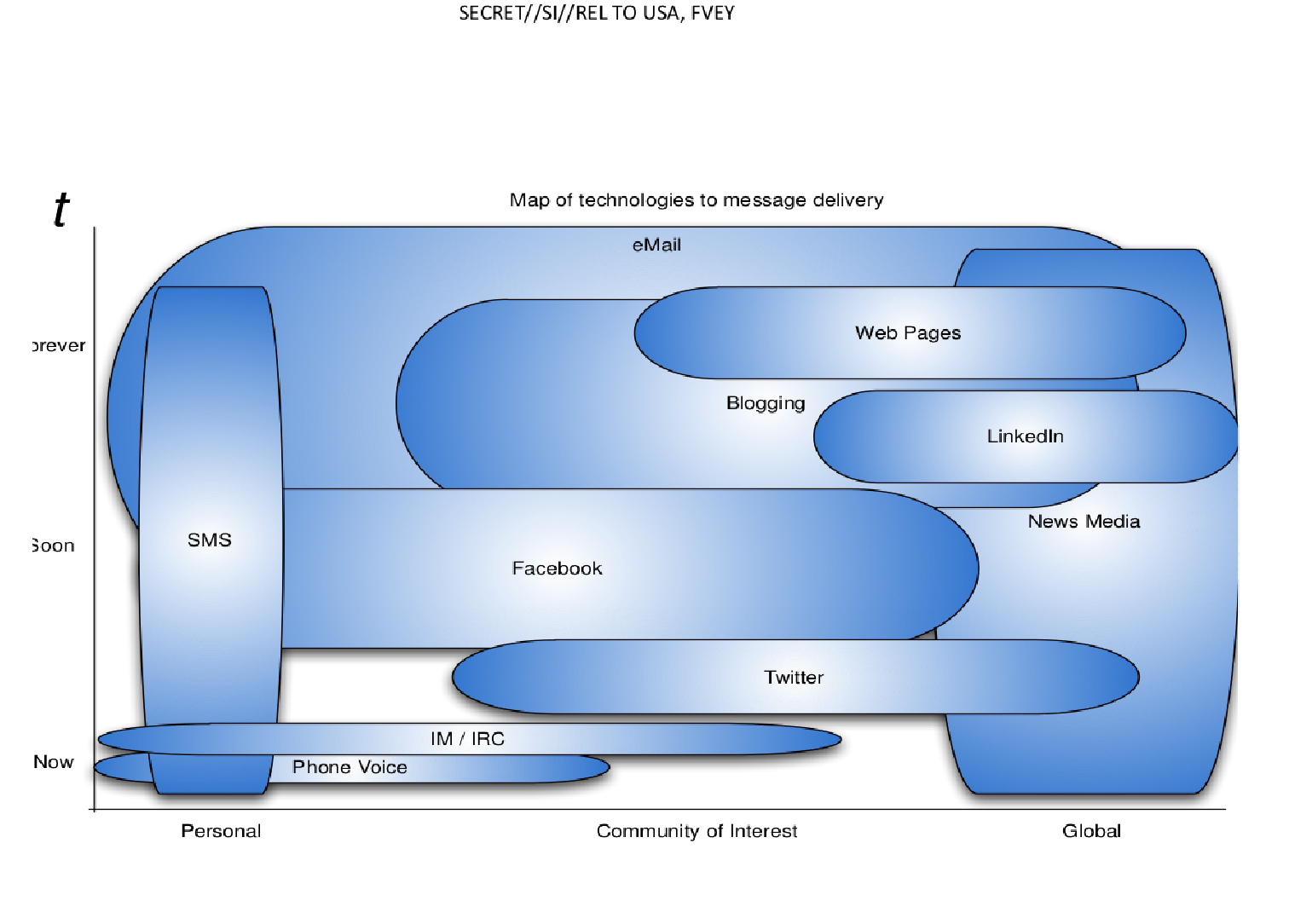
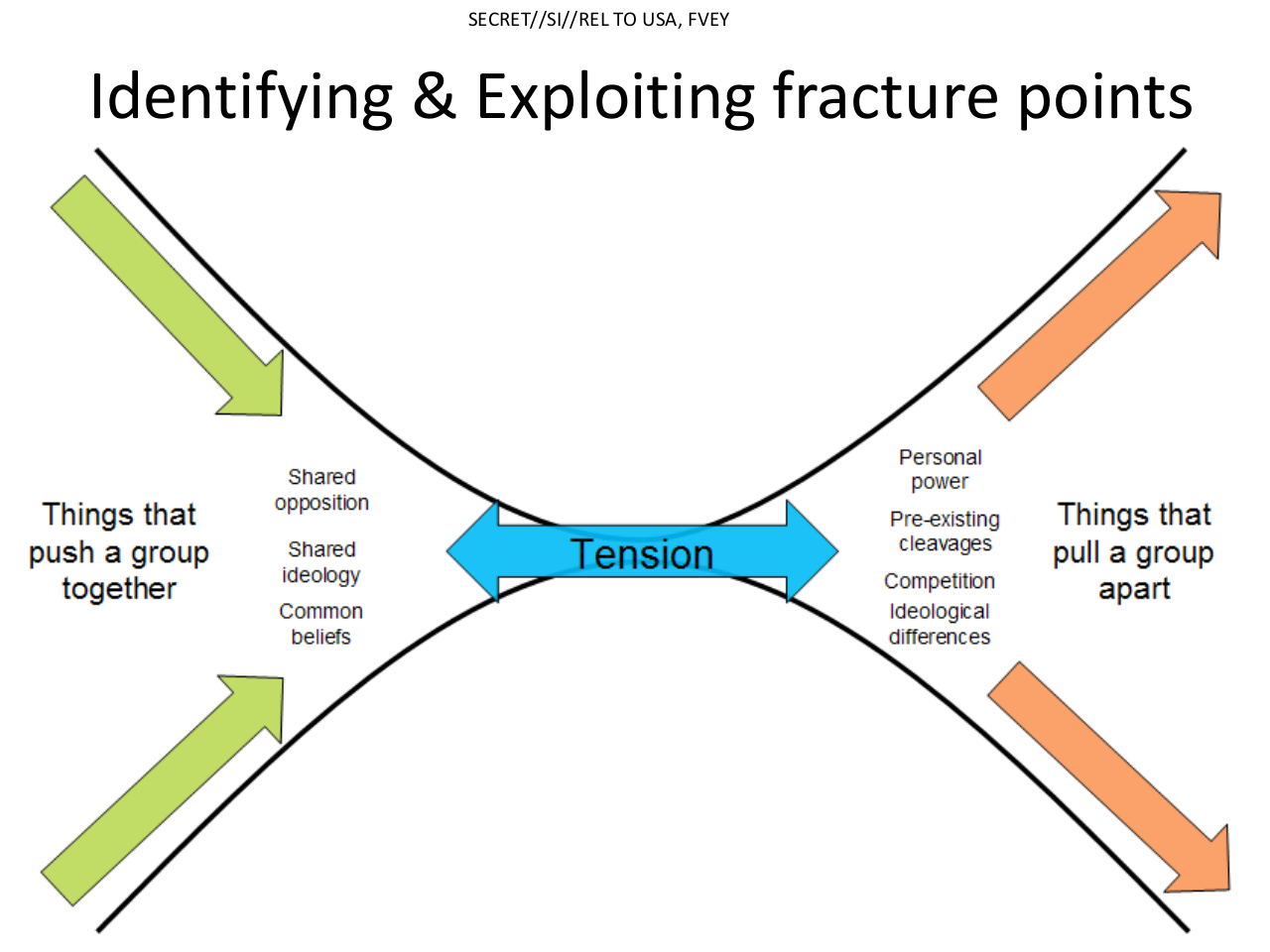
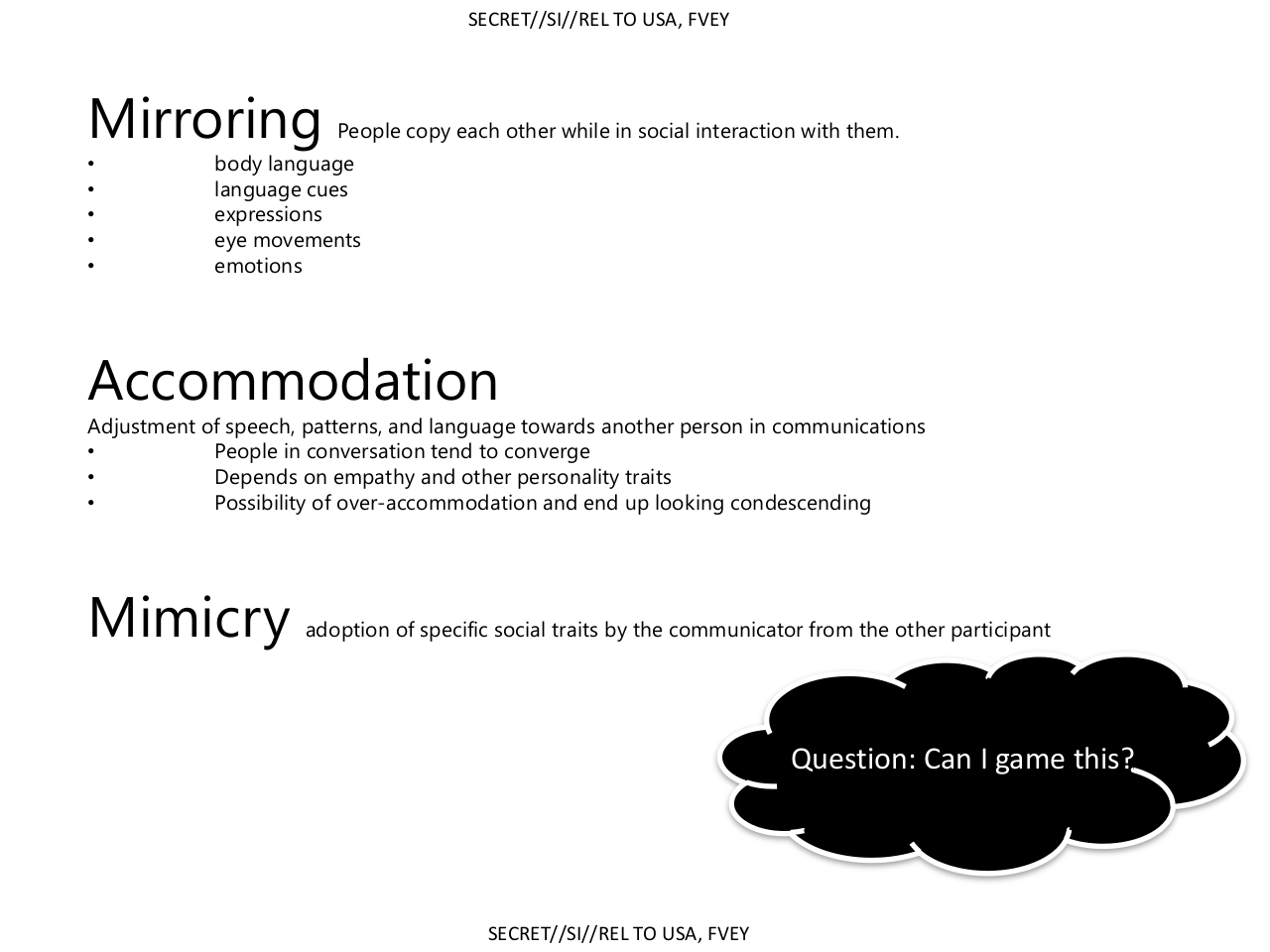
More on Deception(last three shared).
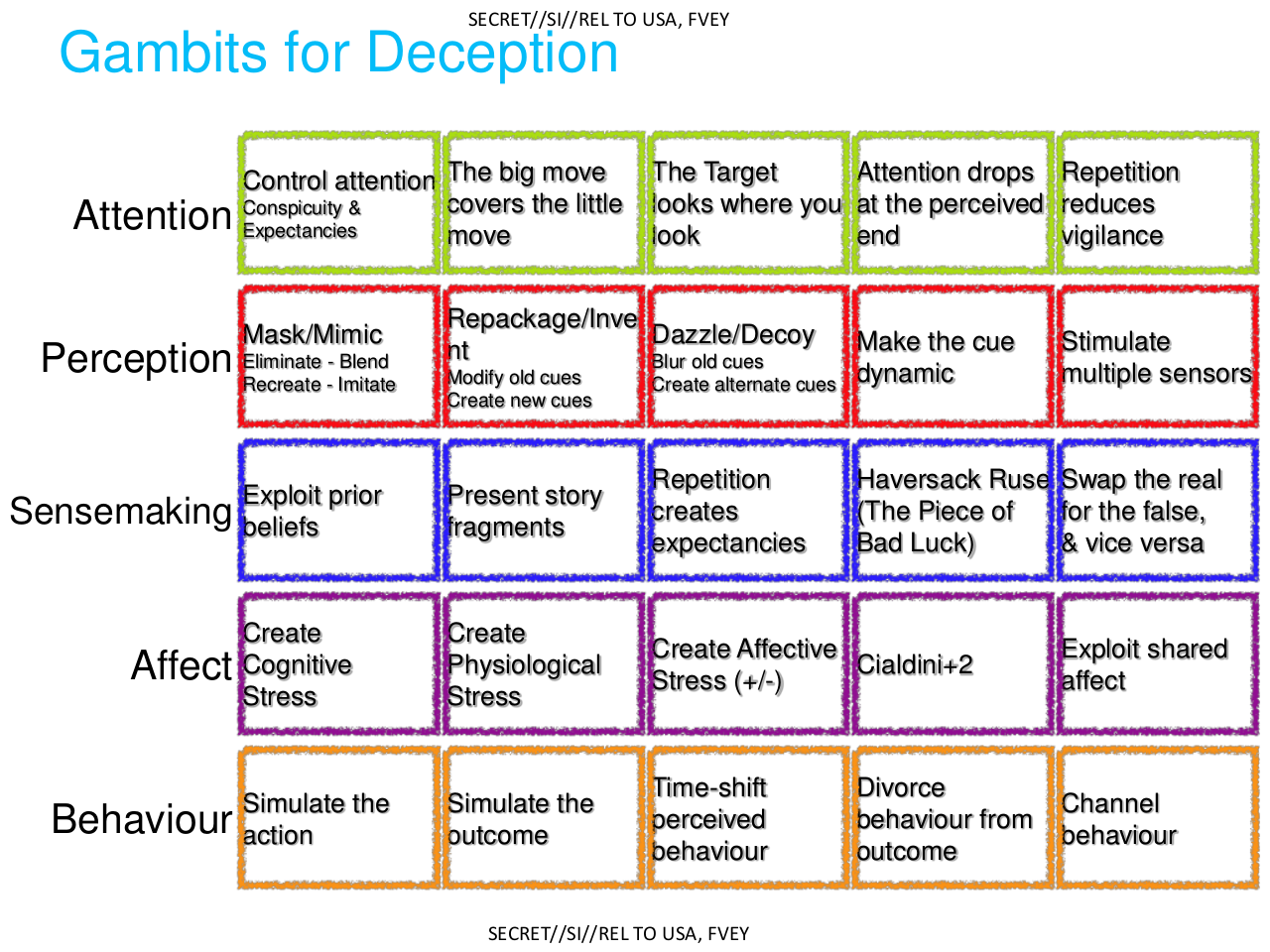
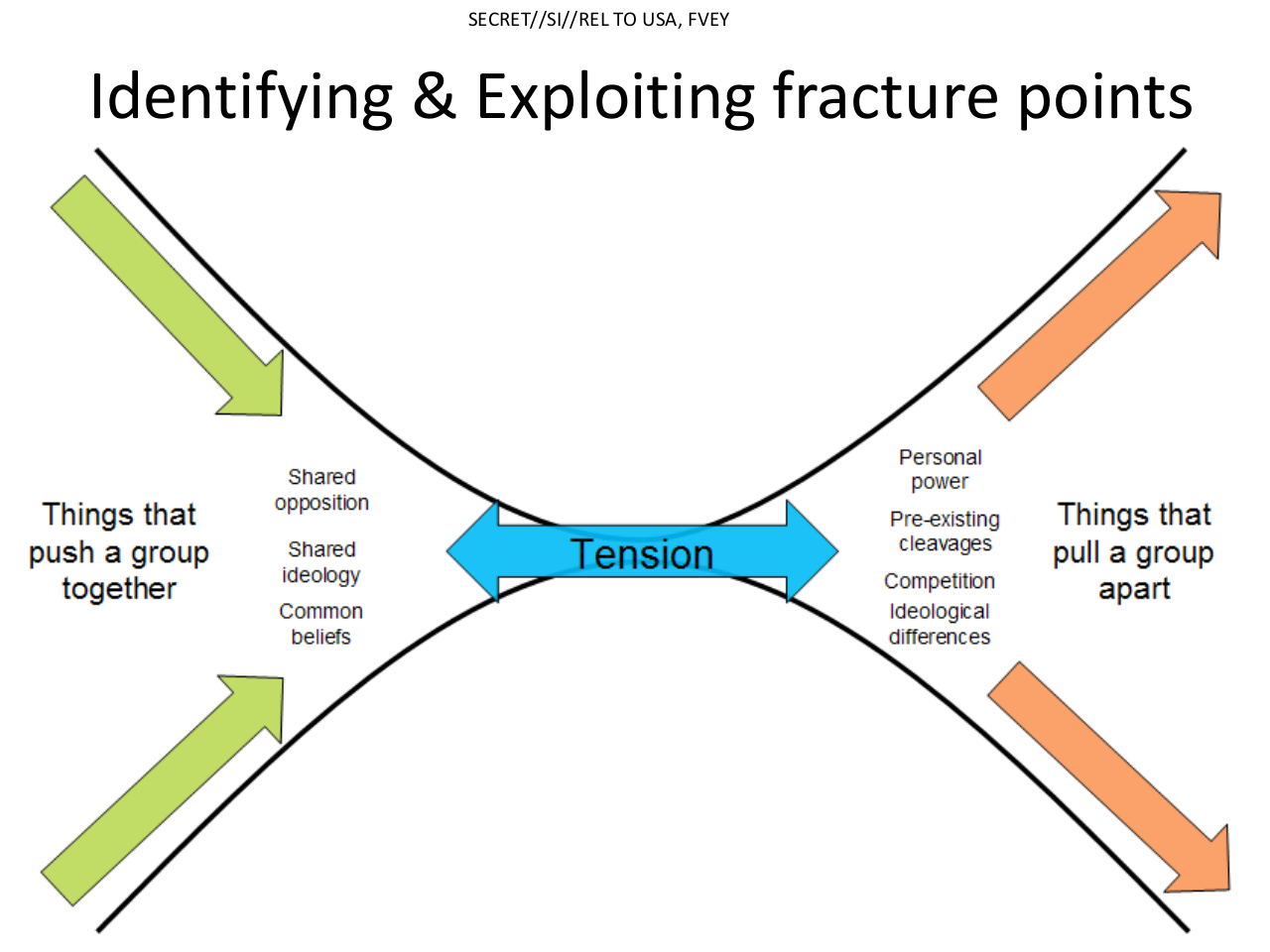
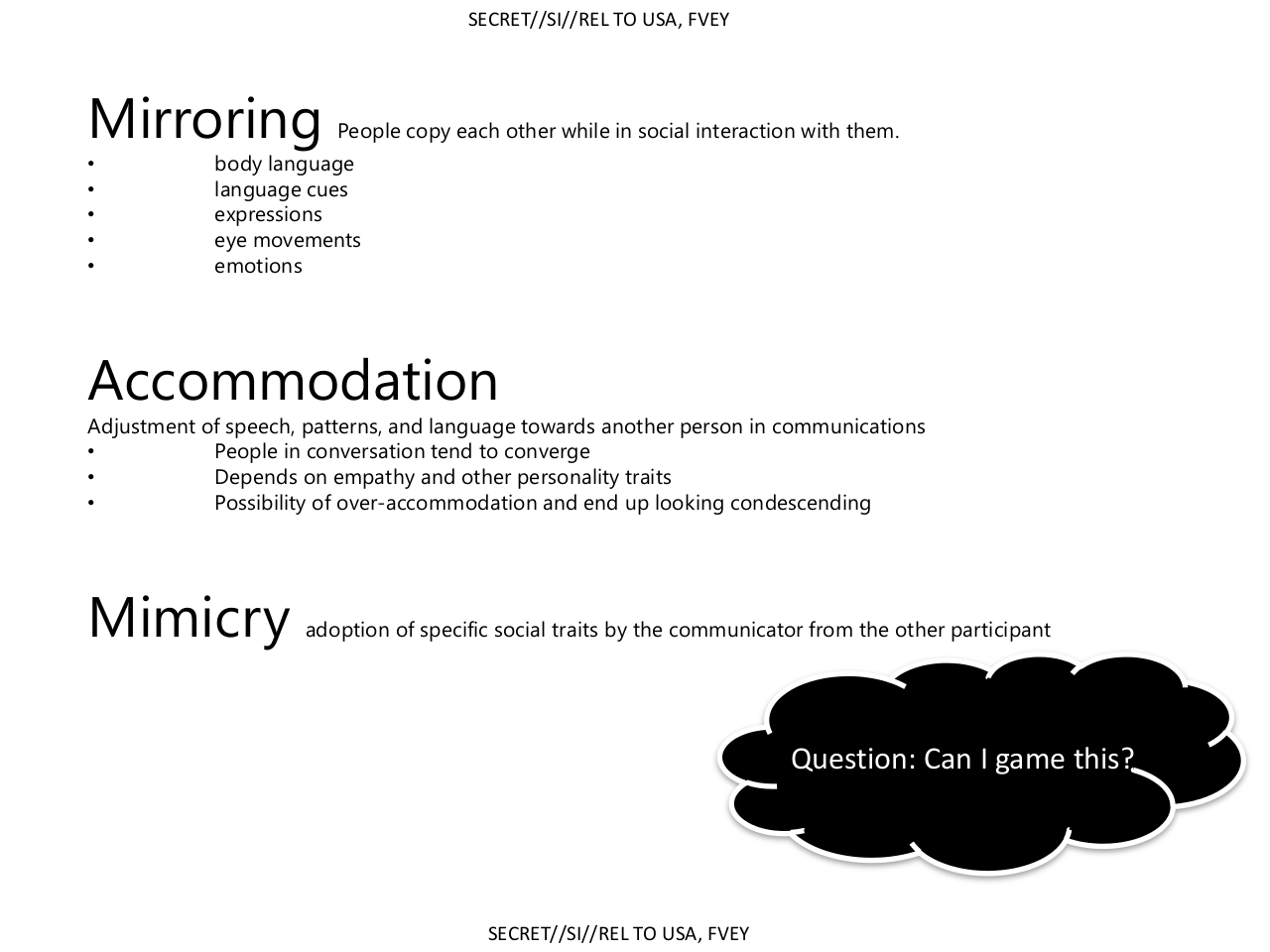
Please see article descriptions as well
-OP sources.
Please see article descriptions as well
-OP sources.
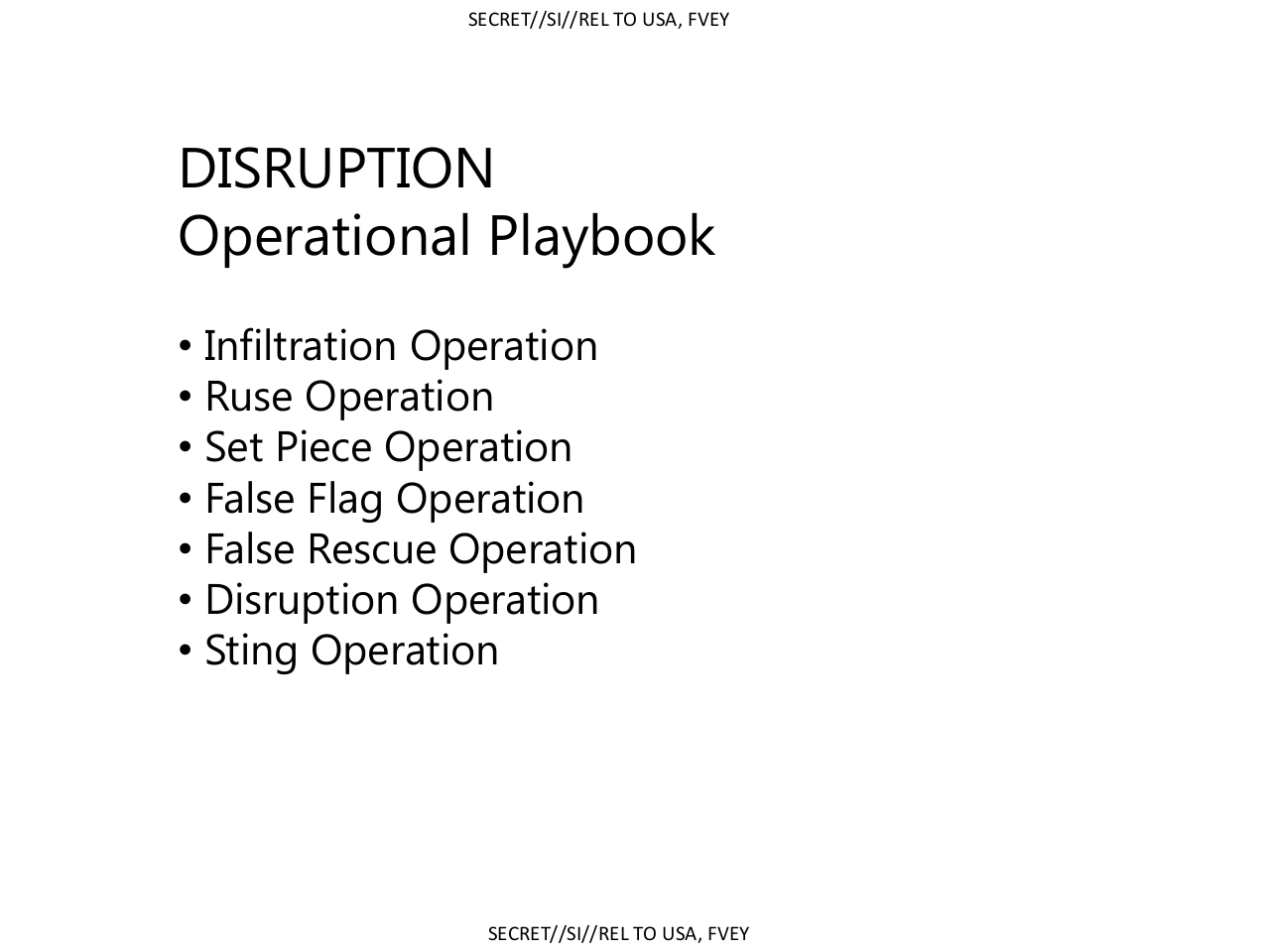
GCHQ
The questions were ignored.
More at OP source/ Greenwald's Firstlook
Lastly,
We submitted numerous questions to GCHQ including: (1) Does GCHQ in fact engage in “false flag operations” where material is posted to the Internet and falsely attributed to someone else?; (2) Does GCHQ engage in efforts to influence or manipulate political discourse online?; and (3) Does GCHQ’s mandate include targeting common criminals (such as boiler room operators), or only foreign threats?
The questions were ignored.
More at OP source/ Greenwald's Firstlook
Lastly,
Whatever else is true, no government should be able to engage in these tactics: what justification is there for having government agencies target people – who have been charged with no crime – for reputation-destruction, infiltrate online political communities, and develop techniques for manipulating online discourse? But to allow those actions with no public knowledge or accountability is particularly unjustifiable.
edit on 24-2-2014 by dreamingawake because: (no reason given)
snypwsd
reply to post by dreamingawake
I see that those slides come from the Five Eyes.... interesting..
Indeed. More in short on the Five Eyes
The "Five Eyes", often abbreviated as "FVEY", refer to an anglophonic alliance comprising Australia, Canada, New Zealand, the United Kingdom and the United States. These countries are bound by the multilateral UKUSA Agreement - a treaty for joint cooperation in signals intelligence.[1][2][3]
The origins of the FVEY can be traced back to World War II, when the Atlantic Charter was issued by the Allies to lay out their goals for a post-war world. During the course of the Cold War, the ECHELON surveillance system was initially developed by the FVEY to monitor the communications of the former Soviet Union and the Eastern Bloc, although it was later used to monitor billions of private communications worldwide.[4][5]
Wiki
reply to post by dreamingawake
I would expect an official handbook, even a top secret one, to be proofread ... "offsensive"?
I would expect an official handbook, even a top secret one, to be proofread ... "offsensive"?
edit on 24-2-2014 by InvisibleOwl because: (no
reason given)
so these are dirty tricks used in going after anonymous members. Interesting.
Well, we all sort of knew it was happening anyway. I would expect our government to be involved in this. I expect some big businesses also do this,
the government is not the only entity that would have an interest in this kind of thing. S%F
reply to post by Bassago
I'm pretty sure that CoIntel operatives will stay miles away from this thread as far as participation goes (especially after your comment). They will observe, though.
I'm pretty sure that CoIntel operatives will stay miles away from this thread as far as participation goes (especially after your comment). They will observe, though.
new topics
-
Former Labour minister Frank Field dies aged 81
People: 1 hours ago -
SETI chief says US has no evidence for alien technology. 'And we never have'
Aliens and UFOs: 3 hours ago -
This is our Story
General Entertainment: 6 hours ago -
President BIDEN Vows to Make Americans Pay More Federal Taxes in 2025 - Political Suicide.
2024 Elections: 8 hours ago -
Ode to Artemis
General Chit Chat: 9 hours ago
top topics
-
University student disciplined after saying veganism is wrong and gender fluidity is stupid
Education and Media: 17 hours ago, 14 flags -
President BIDEN Vows to Make Americans Pay More Federal Taxes in 2025 - Political Suicide.
2024 Elections: 8 hours ago, 12 flags -
Should Biden Replace Harris With AOC On the 2024 Democrat Ticket?
2024 Elections: 14 hours ago, 6 flags -
One Flame Throwing Robot Dog for Christmas Please!
Weaponry: 13 hours ago, 6 flags -
SETI chief says US has no evidence for alien technology. 'And we never have'
Aliens and UFOs: 3 hours ago, 4 flags -
Ditching physical money
History: 12 hours ago, 4 flags -
Don't take advantage of people just because it seems easy it will backfire
Rant: 13 hours ago, 4 flags -
Ode to Artemis
General Chit Chat: 9 hours ago, 3 flags -
Former Labour minister Frank Field dies aged 81
People: 1 hours ago, 3 flags -
This is our Story
General Entertainment: 6 hours ago, 2 flags
active topics
-
Police clash with St George’s Day protesters at central London rally
Social Issues and Civil Unrest • 41 • : BedevereTheWise -
President BIDEN Vows to Make Americans Pay More Federal Taxes in 2025 - Political Suicide.
2024 Elections • 19 • : CriticalStinker -
"We're All Hamas" Heard at Columbia University Protests
Social Issues and Civil Unrest • 268 • : HopeForTheFuture -
Tucker Carlson UFOs are piloted by spiritual entities with bases under the ocean and the ground
Aliens and UFOs • 43 • : Xtrozero -
Thousands Of Young Ukrainian Men Trying To Flee The Country To Avoid Conscription And The War
Other Current Events • 127 • : Consvoli -
University student disciplined after saying veganism is wrong and gender fluidity is stupid
Education and Media • 41 • : BedevereTheWise -
1980s Arcade
General Chit Chat • 25 • : confuzedcitizen -
So this is what Hamas considers 'freedom fighting' ...
War On Terrorism • 241 • : HopeForTheFuture -
Don't take advantage of people just because it seems easy it will backfire
Rant • 6 • : crayzeed -
New whistleblower Jason Sands speaks on Twitter Spaces last night.
Aliens and UFOs • 50 • : baablacksheep1
