It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
0
share:
I'm not sure about everyone else but it's getting real tiring watching as each new NSA surveillance crime come to light in the news. In this case
they're apparently using Google's cookies to home in on and target individual computers / users for targeted attack. This could be you, or me, or
anyone who makes their radar screen.
NSA uses Google cookies to pinpoint targets for hacking
We are pretty much all aware that Google, Yahoo, Microsoft, to name a few are working in collaboration with the NSA so I'll make quick suggestion. Turn off and disallow any cookies from those websites unless absolutely needed.
You probably know how to do this but if not, in Firefox just go to the Tools menu drop down, Select "Options" click the "Privacy" tab. In the "Cookies" section select "Exceptions" and enter the web site name. Click 'Block."
NSA uses Google cookies to pinpoint targets for hacking
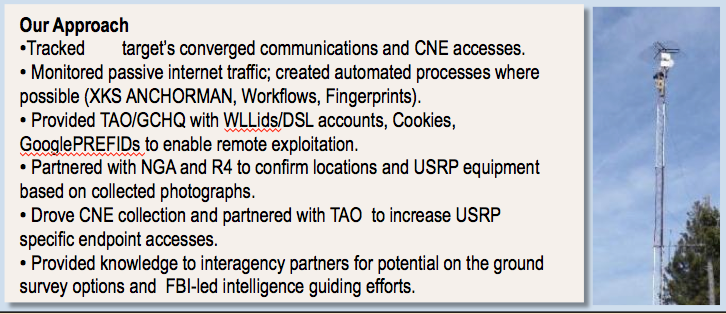
The National Security Agency is secretly piggybacking on the tools that enable Internet advertisers to track consumers, using "cookies" and location data to pinpoint targets for government hacking and to bolster surveillance.
The agency's internal presentation slides, provided by former NSA contractor Edward Snowden, show that when companies follow consumers on the Internet to better serve them advertising, the technique opens the door for similar tracking by the government. The slides also suggest that the agency is using these tracking techniques to help identify targets for offensive hacking operations.
We are pretty much all aware that Google, Yahoo, Microsoft, to name a few are working in collaboration with the NSA so I'll make quick suggestion. Turn off and disallow any cookies from those websites unless absolutely needed.
You probably know how to do this but if not, in Firefox just go to the Tools menu drop down, Select "Options" click the "Privacy" tab. In the "Cookies" section select "Exceptions" and enter the web site name. Click 'Block."
reply to post by Bassago
I have a stupid question...
If the companies which make the browsers are in cahoots with the NSA...and we know they are to some level from past releases if nothing else? Then how can we be sure when we tell it not to take on anything from the outside (like cookies), it really is turned off? Wouldn't Chrome, IE or others be clever to code in just 1 or 2 lines among the millions to make sure the NSA-Tracker remains, even if it appears nothing else is?
Happy Thoughts, eh?
I have a stupid question...
If the companies which make the browsers are in cahoots with the NSA...and we know they are to some level from past releases if nothing else? Then how can we be sure when we tell it not to take on anything from the outside (like cookies), it really is turned off? Wouldn't Chrome, IE or others be clever to code in just 1 or 2 lines among the millions to make sure the NSA-Tracker remains, even if it appears nothing else is?
Happy Thoughts, eh?
reply to post by Wrabbit2000
Google Chrome is already compromised. Internet Explorer I wouldn't trust at all but as of now Mozilla Firefox hasn't shown up as in the NSA pocket yet as far as I know.
Google Chrome is already compromised. Internet Explorer I wouldn't trust at all but as of now Mozilla Firefox hasn't shown up as in the NSA pocket yet as far as I know.
reply to post by Wrabbit2000
Wrabbit,
You are ... CORRECT !!!
I don't trust my Windows-8 machine at all. Any program COULD/MIGHT be a culprit such as MS-Office (perhaps any after the 2005 version) including any Anti-Virus software.
However, I have a 2nd machine that is an XP.
This particular XP machine is NEVER allowed internet access ... ( this is where I do any final program compiling(s) ).
Wrabbit,
You are ... CORRECT !!!
I don't trust my Windows-8 machine at all. Any program COULD/MIGHT be a culprit such as MS-Office (perhaps any after the 2005 version) including any Anti-Virus software.
However, I have a 2nd machine that is an XP.
This particular XP machine is NEVER allowed internet access ... ( this is where I do any final program compiling(s) ).
reply to post by Bassago
The only thing I actually do trust, I don't have much use for at the moment. The encryption on the Wiki file is a secure thing to use.
If it weren't, Assange wouldn't be free..and I think we'll know when that's broken within about 24 hours. So will he.
Anything else, I assume is compromised unless I wrote it or have seen the source..and then? Well...It's running within an operating system I haven't seen the source for ..or couldn't spend the time debugging (in the case of linux) to be certain it's not compromised.
It seems easier to me to assume everything is and just do nothing electronically which isn't fit for the public to view or hear in a worst case scenario. Much less stress in life that way, IMO.
The only thing I actually do trust, I don't have much use for at the moment. The encryption on the Wiki file is a secure thing to use.
If it weren't, Assange wouldn't be free..and I think we'll know when that's broken within about 24 hours. So will he.
Anything else, I assume is compromised unless I wrote it or have seen the source..and then? Well...It's running within an operating system I haven't seen the source for ..or couldn't spend the time debugging (in the case of linux) to be certain it's not compromised.
It seems easier to me to assume everything is and just do nothing electronically which isn't fit for the public to view or hear in a worst case scenario. Much less stress in life that way, IMO.
reply to post by Wrabbit2000
I read some where that Snowden communicated the information via PGP ... ( it's not real easy to setup; generally not for casual users ).
HOWEVER
It appears that Wiki has Destroyed the Snowden Data.
HOWEVER
Wiki had already distributed the data to others ( perhaps unknown and known).
Hope that helps.
I read some where that Snowden communicated the information via PGP ... ( it's not real easy to setup; generally not for casual users ).
HOWEVER
It appears that Wiki has Destroyed the Snowden Data.
HOWEVER
Wiki had already distributed the data to others ( perhaps unknown and known).
Hope that helps.
edit on 10-12-2013 by FarleyWayne because: (no reason given)
reply to post by Wrabbit2000
I agree to a point but I'm also sure that political dissidents fall into the category of targets. ATS has quite a few unhappy campers in this regard. Don't forget the NSA creepy crawling WoW.
I'm simply saying don't make it any easier for them, there is a multi-pronged assault taking place. We should implement anything that slows or hinders that.
It seems easier to me to assume everything is and just do nothing electronically which isn't fit for the public to view or hear in a worst case scenario. Much less stress in life that way, IMO.
I agree to a point but I'm also sure that political dissidents fall into the category of targets. ATS has quite a few unhappy campers in this regard. Don't forget the NSA creepy crawling WoW.
I'm simply saying don't make it any easier for them, there is a multi-pronged assault taking place. We should implement anything that slows or hinders that.
The problem is this (I am a cyber security /network guy who is paid for my skills and is the core of my own private business) this is probably the
tip of the iceberg , I always suspected that in the whole process of vetting public releases of OS's there are regulations that these (The Microsoft,
Google other vendors) are subject to under U.S. law, especially if they will be used in government offices and for official communications, that for
emergency purposes there are key-ways through any firewall and encryption all the way into your local OS that a 3 letter agency already has access to
prior to any release of the version or device.
We know that an app called Monkey Puzzle was also used to gain access to emails and other messaging on Windows, the main thing is there are things like access, that will never be released to the public purposely because they are protected under security classifications "Above Top Secret" no pun, or compartmentalized to infinity, but to anyone that thinks that this Google revelation is the only way, you probably have not been keeping up with cyber security or the history of it in recent times which involves ISP's and other resources that are linked via the internet backbone also working with 3 letter agencies.
We know that an app called Monkey Puzzle was also used to gain access to emails and other messaging on Windows, the main thing is there are things like access, that will never be released to the public purposely because they are protected under security classifications "Above Top Secret" no pun, or compartmentalized to infinity, but to anyone that thinks that this Google revelation is the only way, you probably have not been keeping up with cyber security or the history of it in recent times which involves ISP's and other resources that are linked via the internet backbone also working with 3 letter agencies.
edit on 10-12-2013 by phinubian because: (no reason given)
reply to post by phinubian
Network, Cloud ... where ever, etc.
Thats "The-Why?" I think it important to Encrypt 1st.
BUT
Because there can be Key-Loggers, the Encrypted-File(s) should be performed on a computer that NEVER touches ANY Network (internal NOR external) ... then copy the encrypted file to a floppy or usb stick AFTER a fresh format.
Stuff's ... Crazy !?!?!?
Network, Cloud ... where ever, etc.
Thats "The-Why?" I think it important to Encrypt 1st.
BUT
Because there can be Key-Loggers, the Encrypted-File(s) should be performed on a computer that NEVER touches ANY Network (internal NOR external) ... then copy the encrypted file to a floppy or usb stick AFTER a fresh format.
Stuff's ... Crazy !?!?!?
reply to post by phinubian
All true however there's no reason not to plug every security hole we are aware of. Snowdens document revelations are a free gift, people should use them.
The internet backbone issue is a separate problem but related in a way. If you don't have the cookie data to scoop up on the backbone then that's one less thing to worry about.
All true however there's no reason not to plug every security hole we are aware of. Snowdens document revelations are a free gift, people should use them.
The internet backbone issue is a separate problem but related in a way. If you don't have the cookie data to scoop up on the backbone then that's one less thing to worry about.
reply to post by Bassago
You could use TWO BROWSER simultaneously ... Example:
Internet Explorer - Cookies ON
FireFox- - - - - - - - Cookies OFF
That's what I'm doing ... except, just the opposite; I.E.=Cookies OFF, F.F.=Cookies=ON.
AND
I Clear-My-CACHES (on both) ... Regularly !
AND
I've got to call it quits ... It's been a long day for me ... ( all the news everywhere has been ridiculously overwhelming ).
You could use TWO BROWSER simultaneously ... Example:
Internet Explorer - Cookies ON
FireFox- - - - - - - - Cookies OFF
That's what I'm doing ... except, just the opposite; I.E.=Cookies OFF, F.F.=Cookies=ON.
AND
I Clear-My-CACHES (on both) ... Regularly !
AND
I've got to call it quits ... It's been a long day for me ... ( all the news everywhere has been ridiculously overwhelming ).
edit on
10-12-2013 by FarleyWayne because: (no reason given)
Wrabbit2000
reply to post by Bassago
Then how can we be sure when we tell it not to take on anything from the outside (like cookies), it really is turned off? Wouldn't Chrome, IE or others be clever to code in just 1 or 2 lines among the millions to make sure the NSA-Tracker remains, even if it appears nothing else is?
It is not so complicated to check if these options really work. You can easily watch your network traffic on a low level and inspect any TCP/IP flag if you wish. If you don't trust your OS get a cheap barebone pc with a relatively unknown open source linux without any additional software (not one of those standard distributions). Then hock it up to your internal network so that all other traffic has to pass though this hub (non switching). Now you can use tcpdump or other solutions to monitor every bit in the network and watch what your PCs/Macs/... are transferring.
But always remember: As long as your computer has a real time clock (they all have) along with it unique inaccuracy over time it may still be possible to identify your computer as every IP packet has a timestamp. No cookies or special software needed.
Apologies folks, to block these cookies use the following steps instead:
Block cookies for a single site - Firefox
Using the exception option under the privacy tab only appears to work for a single session.
Block cookies for a single site - Firefox
Using the exception option under the privacy tab only appears to work for a single session.
new topics
-
2024 Pigeon Forge Rod Run - On the Strip (Video made for you)
Automotive Discussion: 13 minutes ago -
Gaza Terrorists Attack US Humanitarian Pier During Construction
Middle East Issues: 39 minutes ago -
The functionality of boldening and italics is clunky and no post char limit warning?
ATS Freshman's Forum: 1 hours ago -
Meadows, Giuliani Among 11 Indicted in Arizona in Latest 2020 Election Subversion Case
Mainstream News: 2 hours ago -
Massachusetts Drag Queen Leads Young Kids in Free Palestine Chant
Social Issues and Civil Unrest: 2 hours ago -
Weinstein's conviction overturned
Mainstream News: 3 hours ago -
Supreme Court Oral Arguments 4.25.2024 - Are PRESIDENTS IMMUNE From Later Being Prosecuted.
Above Politics: 5 hours ago -
Krystalnacht on today's most elite Universities?
Social Issues and Civil Unrest: 5 hours ago -
Chris Christie Wishes Death Upon Trump and Ramaswamy
Politicians & People: 6 hours ago -
University of Texas Instantly Shuts Down Anti Israel Protests
Education and Media: 8 hours ago
top topics
-
Krystalnacht on today's most elite Universities?
Social Issues and Civil Unrest: 5 hours ago, 8 flags -
Weinstein's conviction overturned
Mainstream News: 3 hours ago, 6 flags -
Electrical tricks for saving money
Education and Media: 17 hours ago, 5 flags -
Supreme Court Oral Arguments 4.25.2024 - Are PRESIDENTS IMMUNE From Later Being Prosecuted.
Above Politics: 5 hours ago, 5 flags -
University of Texas Instantly Shuts Down Anti Israel Protests
Education and Media: 8 hours ago, 5 flags -
Meadows, Giuliani Among 11 Indicted in Arizona in Latest 2020 Election Subversion Case
Mainstream News: 2 hours ago, 4 flags -
Massachusetts Drag Queen Leads Young Kids in Free Palestine Chant
Social Issues and Civil Unrest: 2 hours ago, 3 flags -
Chris Christie Wishes Death Upon Trump and Ramaswamy
Politicians & People: 6 hours ago, 2 flags -
Any one suspicious of fever promotions events, major investor Goldman Sachs card only.
The Gray Area: 10 hours ago, 2 flags -
God's Righteousness is Greater than Our Wrath
Religion, Faith, And Theology: 14 hours ago, 1 flags
active topics
-
University of Texas Instantly Shuts Down Anti Israel Protests
Education and Media • 177 • : theatreboy -
The functionality of boldening and italics is clunky and no post char limit warning?
ATS Freshman's Forum • 8 • : grey580 -
Breaking Baltimore, ship brings down bridge, mass casualties
Other Current Events • 487 • : Threadbarer -
2024 Pigeon Forge Rod Run - On the Strip (Video made for you)
Automotive Discussion • 1 • : chiefsmom -
Gaza Terrorists Attack US Humanitarian Pier During Construction
Middle East Issues • 9 • : Asher47 -
Fossils in Greece Suggest Human Ancestors Evolved in Europe, Not Africa
Origins and Creationism • 84 • : whereislogic -
Ditching physical money
History • 21 • : SprocketUK -
Meadows, Giuliani Among 11 Indicted in Arizona in Latest 2020 Election Subversion Case
Mainstream News • 4 • : ElitePlebeian2 -
Is there a hole at the North Pole?
ATS Skunk Works • 38 • : Therealbeverage -
One Flame Throwing Robot Dog for Christmas Please!
Weaponry • 10 • : ATruGod
0
