It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
3
share:
GCHQ challenges codebreakers via social networks
www.bbc.co.uk
(visit the link for the full news article)
UK intelligence agency GCHQ has launched a code-cracking competition to help attract new talent.
The organisation has invited potential applicants to solve a visual code posted at an unbranded standalone website.
The challenge has also be "seeded" to social media sites, blogs and forums.
I found it interesting to see a British intelligence agency using social networks in this way.
That's pretty innovative by the standards of the usually rather traditional British civil sevice.
The relevant challenge is at:
www.canyoucrackit.co.uk...
I'll embed the code below for anyone interested:
www.bbc.co.uk
(visit the link for the full news article)
The story is also on various other news websites, including:
www.telegraph.co.uk...
That's pretty innovative by the standards of the usually rather traditional British civil sevice.
The relevant challenge is at:
www.canyoucrackit.co.uk...
I'll embed the code below for anyone interested:
www.bbc.co.uk
(visit the link for the full news article)
The story is also on various other news websites, including:
www.telegraph.co.uk...
It lacks the romance of a furtive meeting in an Oxbridge college quad. But secret service chiefs hope this will be a far more effective method of recruiting the spies of the future.
...
Players who can crack a code are directed to the GCHQ website and invited to apply for a job.
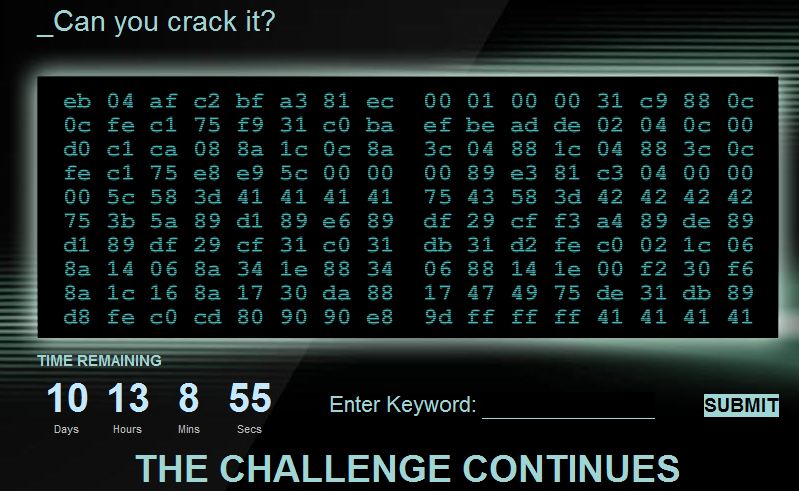
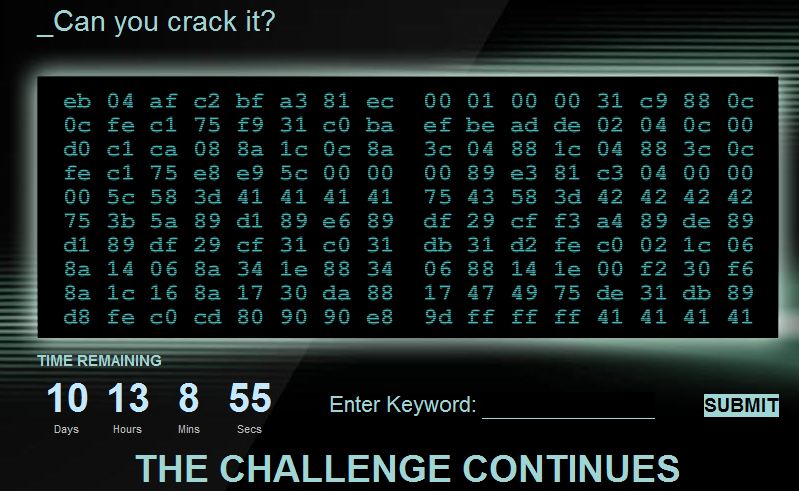
After following a link to canyoucrackit.co.uk, players are presented with a seemingly meaningless grid of 160 pairs of letters and numbers, and a countdown clock. They are given seven hours to unscramble the numbers and correctly identify a secret word.
The game contains no reference to GCHQ, but those players who get the word right are put on a fast-track to a secret service career.
edit on 1-12-2011 by IsaacKoi because: (no reason given)
Hello people,
yes, it's a very interesting task. I've already posted some info that might help in THIS THREAD, which was started by member "definity" around 0730 UTC today -- namely over 3 1/2 hours ago.
In short, you need to extract the two halves of the shellcode from both the .png image and from the "comment" that goes with the image, put the halves together and then find a GET request to obtain a _javascript file.
But as the thread I referred to appears to be the first I'd prefer to continue there.
Best regards,
Mike
yes, it's a very interesting task. I've already posted some info that might help in THIS THREAD, which was started by member "definity" around 0730 UTC today -- namely over 3 1/2 hours ago.
In short, you need to extract the two halves of the shellcode from both the .png image and from the "comment" that goes with the image, put the halves together and then find a GET request to obtain a _javascript file.
But as the thread I referred to appears to be the first I'd prefer to continue there.
Best regards,
Mike
Originally posted by PurpleDog UK
www.abovetopsecret.com...
Thanks. I did a search based on the BBC news article title, and nothing came up. I don't visit that forum on ATS.
Have you tried yet ?
Just giving it a quick go now.
To save everyone else time, here is a transcription of the hex code I found online:
http:///0y0B4vCT
eb 04 af c2 bf a3 81 ec 00 01 00 00 31 c9 88 0c
0c fe c1 75 f9 31 c0 ba ef be ad de 02 04 0c 00
d0 c1 ca 08 8a 1c 0c 8a 3c 04 88 1c 04 88 3c 0c
fe c1 75 e8 e9 5c 00 00 00 89 e3 81 c3 04 00 00
00 5c 58 3d 41 41 41 41 75 43 58 3d 42 42 42 42
75 3b 5a 89 d1 89 e6 89 df 29 cf f3 a4 89 de 89
d1 89 df 29 cf 31 c0 31 db 31 d2 fe c0 02 1c 06
8a 14 06 8a 34 1e 88 34 06 88 14 1e 00 f2 30 f6
8a 1c 16 8a 17 30 da 88 17 47 49 75 de 31 db 89
d8 fe c0 cd 80 90 90 e8 9d ff ff ff 41 41 41 41
erm... one minor flaw that can see with that idea...
What happens if the one who cracks it is from the 'other' side ? Do they still get hired or summarily executed ?
What happens if the one who cracks it is from the 'other' side ? Do they still get hired or summarily executed ?
Probably a stupid question, but couldn't you just brute force guess the pass phrase? Not exactly in the spirit of things but it get's the job done.
new topics
-
Has Tesla manipulated data logs to cover up auto pilot crash?
Automotive Discussion: 1 hours ago -
whistleblower Captain Bill Uhouse on the Kingman UFO recovery
Aliens and UFOs: 6 hours ago -
1980s Arcade
General Chit Chat: 8 hours ago -
Deadpool and Wolverine
Movies: 9 hours ago -
Teenager makes chess history becoming the youngest challenger for the world championship crown
Other Current Events: 10 hours ago -
CIA botched its handling of sexual assault allegations, House intel report says
Breaking Alternative News: 11 hours ago
top topics
-
Lawsuit Seeks to ‘Ban the Jab’ in Florida
Diseases and Pandemics: 13 hours ago, 20 flags -
Starburst galaxy M82 - Webb Vs Hubble
Space Exploration: 15 hours ago, 13 flags -
The Superstition of Full Moons Filling Hospitals Turns Out To Be True!
Medical Issues & Conspiracies: 17 hours ago, 8 flags -
CIA botched its handling of sexual assault allegations, House intel report says
Breaking Alternative News: 11 hours ago, 8 flags -
15 Unhealthiest Sodas On The Market
Health & Wellness: 15 hours ago, 6 flags -
whistleblower Captain Bill Uhouse on the Kingman UFO recovery
Aliens and UFOs: 6 hours ago, 6 flags -
1980s Arcade
General Chit Chat: 8 hours ago, 4 flags -
Deadpool and Wolverine
Movies: 9 hours ago, 3 flags -
Teenager makes chess history becoming the youngest challenger for the world championship crown
Other Current Events: 10 hours ago, 3 flags -
Has Tesla manipulated data logs to cover up auto pilot crash?
Automotive Discussion: 1 hours ago, 0 flags
active topics
-
Lawsuit Seeks to ‘Ban the Jab’ in Florida
Diseases and Pandemics • 23 • : burritocat -
Has Tesla manipulated data logs to cover up auto pilot crash?
Automotive Discussion • 1 • : andy06shake -
15 Unhealthiest Sodas On The Market
Health & Wellness • 36 • : tanstaafl -
My wife just had a very powerful prophetic dream - massive war in Israel...
The Gray Area • 12 • : SchrodingersRat -
-@TH3WH17ERABB17- -Q- ---TIME TO SHOW THE WORLD--- -Part- --44--
Dissecting Disinformation • 606 • : burritocat -
"We're All Hamas" Heard at Columbia University Protests
Social Issues and Civil Unrest • 199 • : FlyersFan -
It takes One to Be; Two to Tango; Three to Create.
Philosophy and Metaphysics • 7 • : Terpene -
Take it to the Media when you protest.. Don't let them ignore you!
Education and Media • 4 • : SchrodingersRat -
They Killed Dr. Who for Good
Rant • 62 • : FlyersFan -
Definitive 9.11 Pentagon EVIDENCE.
9/11 Conspiracies • 421 • : Lazy88
3

