It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
share:
a reply to: pavil
Exactly, apparently liberals think Russians are herp-derps when it comes to hacking.
Unfortunately the glaring herp-derps are libs themselves in buying hook line and sinker into anything the media says and every circumstantial thing that may favor them, even though they were exposed to evidence that the 3 letter agencies employ those tactics.
Scary...that is to think about how many liberal voter there are.
Exactly, apparently liberals think Russians are herp-derps when it comes to hacking.
Unfortunately the glaring herp-derps are libs themselves in buying hook line and sinker into anything the media says and every circumstantial thing that may favor them, even though they were exposed to evidence that the 3 letter agencies employ those tactics.
Scary...that is to think about how many liberal voter there are.
a reply to: Vector99
And apparently so-called "conservatives" think that the Russians are incapable of playing the same double bluff games as the Americans. When it looked like the NSA hacked some voting machines, the resident experts here averred that it was impossible to spoof a hack and retrieve information. Now that it appears that Russians hacked the CIA as well as the DNC, it is now child's play for the American intelligence agencies to spoof a hack. Gotta love the consistency of online "experts."
Exactly, apparently liberals think Russians are herp-derps when it comes to hacking.
And apparently so-called "conservatives" think that the Russians are incapable of playing the same double bluff games as the Americans. When it looked like the NSA hacked some voting machines, the resident experts here averred that it was impossible to spoof a hack and retrieve information. Now that it appears that Russians hacked the CIA as well as the DNC, it is now child's play for the American intelligence agencies to spoof a hack. Gotta love the consistency of online "experts."
Prayers for Mr Assange today - hopefully Ecuador will get a new president who will stand up against corruption and wrongdoing in the world, and asylum
is continued. Godbless
a reply to: DJW001
You're delusional. I don't read ATS very often because of idiotic statements made by complete fools. It's sad that this site is attracting people like you. It's so obvious Russia had nothing to do with this and the people who continually push that they did are the same people who are ruining this world.
You're delusional. I don't read ATS very often because of idiotic statements made by complete fools. It's sad that this site is attracting people like you. It's so obvious Russia had nothing to do with this and the people who continually push that they did are the same people who are ruining this world.
a reply to: andrew778
True, but remember that the system is not broken, it was built this way.
A few years back I thought we might have crossed the line when the outcome became irreversible, today I claim with certainty, we are well passed the point of no return and heading for a huge downfall in almost every aspect of well being and the society. We once thought that World was not good, like in the 90s, But now that seems like a dream. We are so doomed one might consider suicide being an option to end this nonsense, cuz there is literally nothing left to fight for. TPTB won.
ATS also became frustrating to read as the only topics that get attention are Trump related, or maybe some religion promoted hatred or just nonsense about fake "terror attacks".
We do not strive for the stars anymore. We are done... also iťs useless to complain about that, it gets worse every day.
True, but remember that the system is not broken, it was built this way.
A few years back I thought we might have crossed the line when the outcome became irreversible, today I claim with certainty, we are well passed the point of no return and heading for a huge downfall in almost every aspect of well being and the society. We once thought that World was not good, like in the 90s, But now that seems like a dream. We are so doomed one might consider suicide being an option to end this nonsense, cuz there is literally nothing left to fight for. TPTB won.
ATS also became frustrating to read as the only topics that get attention are Trump related, or maybe some religion promoted hatred or just nonsense about fake "terror attacks".
We do not strive for the stars anymore. We are done... also iťs useless to complain about that, it gets worse every day.
edit on 2-4-2017 by
Necrose because: (no reason given)
edit on 2-4-2017 by Necrose because: (no reason given)
originally posted by: andrew778
a reply to: DJW001
You're delusional. I don't read ATS very often because of idiotic statements made by complete fools. It's sad that this site is attracting people like you. It's so obvious Russia had nothing to do with this and the people who continually push that they did are the same people who are ruining this world.
Do you have anything to contribute to the conversation beside ad hominem attacks? Still, thank you for illustrating how Russia uses trolls to undercut reasoned debate.
ETA: You are, of course, welcome to stop visiting this site if some members refuse to reinforce your personal beliefs.
edit on 2-4-2017 by DJW001 because: (no reason given)
edit on 2-4-2017 by DJW001 because: (no reason given)
a reply to: DJW001
Leaks?
Before he became President, there was information doing the rounds, legitimate information that expressed and detailed in exacting fashion, the many reasons why Trump was never fit to lead a conga line, leave alone a nation. The hot mic recording (which, regardless of opinions to the contrary from the gutter dwellers in the world, SHOULD have been the bullet that put the presidency beyond his reach), the history of his business practices (which ARE a solid indicator of his methodology as a man, his lack of moral fortitude and an indicator of just how poor of a resource manager he actually is).
These were not LEAKS, because they did not come by way of an intelligence service or a clandestine operation of any kind. They were simply the result of weaponised, but albeit legitimate journalism. These are things that anyone could have found out, if they had been willing to bother to do so, and also things that many people voting in the election ought to REMEMBER, because his failures are common knowledge in places affected by them, and to those living near to those who lost out to one of his dodgy investments, or to one of the property developments that he put his name on, despite them being bound for failure from the get go, costing investors their life savings.
Anyone could have found out, and many people if they were being honest with themselves, would have remembered, that Trump has been in and out of court more times than a bailiff with ADHD and a stimulant abuse problem, that he uses his money and access to lawyers, to bully those he has harmed into silence, that he is essentially a gangster without an army, the sort of man who does with paper what many have to resort to a bullet to resolve. He is a disgusting individual, with a disgusting empire, and far from being a successful man, has squandered a great deal of his fortune on compensating for the size of his "hands". He is a morally defunct, mentally deficient con artist and little else besides, and again, this is a truth one could come to after even the most perfunctory examination of his character over the years.
This required no leaks to discover, this required no special access, no dirty tricks, no secret recording devices or clever manipulation of a records clerk to uncover. It is simply the conclusion than any reasonable, compassionate, decent and moral person would come to, upon examining the slightest bit of his history and behaviour.
Leaks?
Before he became President, there was information doing the rounds, legitimate information that expressed and detailed in exacting fashion, the many reasons why Trump was never fit to lead a conga line, leave alone a nation. The hot mic recording (which, regardless of opinions to the contrary from the gutter dwellers in the world, SHOULD have been the bullet that put the presidency beyond his reach), the history of his business practices (which ARE a solid indicator of his methodology as a man, his lack of moral fortitude and an indicator of just how poor of a resource manager he actually is).
These were not LEAKS, because they did not come by way of an intelligence service or a clandestine operation of any kind. They were simply the result of weaponised, but albeit legitimate journalism. These are things that anyone could have found out, if they had been willing to bother to do so, and also things that many people voting in the election ought to REMEMBER, because his failures are common knowledge in places affected by them, and to those living near to those who lost out to one of his dodgy investments, or to one of the property developments that he put his name on, despite them being bound for failure from the get go, costing investors their life savings.
Anyone could have found out, and many people if they were being honest with themselves, would have remembered, that Trump has been in and out of court more times than a bailiff with ADHD and a stimulant abuse problem, that he uses his money and access to lawyers, to bully those he has harmed into silence, that he is essentially a gangster without an army, the sort of man who does with paper what many have to resort to a bullet to resolve. He is a disgusting individual, with a disgusting empire, and far from being a successful man, has squandered a great deal of his fortune on compensating for the size of his "hands". He is a morally defunct, mentally deficient con artist and little else besides, and again, this is a truth one could come to after even the most perfunctory examination of his character over the years.
This required no leaks to discover, this required no special access, no dirty tricks, no secret recording devices or clever manipulation of a records clerk to uncover. It is simply the conclusion than any reasonable, compassionate, decent and moral person would come to, upon examining the slightest bit of his history and behaviour.
a reply to: TrueBrit
In case someone suggests the Russians hacked the CIA :
Former CIA Deputy Director Mike Morell: CIA leak 'absolutely' an 'inside job'
In case someone suggests the Russians hacked the CIA :
Former CIA Deputy Director Mike Morell: CIA leak 'absolutely' an 'inside job'
originally posted by: theultimatebelgianjoke
a reply to: TrueBrit
In case someone suggests the Russians hacked the CIA :
Former CIA Deputy Director Mike Morell: CIA leak 'absolutely' an 'inside job'
It could be the work of a mole, working as a subcontractor, so, no, the Russians are not ruled out.
a reply to: TrueBrit
Exactly. The people who starred you need to re-read what you said. No one obtained classified information about Trump and released it to WikiLeaks. Remember, we now know there was a dossier compiled but it was not used. We now know that intelligence agencies may have been watching Trump's associates, but what they found was not leaked. This suggests that the leaks that did happen were tactical in nature, and favored Trump over Clinton. That is all anyone has been saying.
I agree that anyone paying attention could see that Trump was completely unsuitable for high office. The Clinton campaign relied on this, yet lost.
Exactly. The people who starred you need to re-read what you said. No one obtained classified information about Trump and released it to WikiLeaks. Remember, we now know there was a dossier compiled but it was not used. We now know that intelligence agencies may have been watching Trump's associates, but what they found was not leaked. This suggests that the leaks that did happen were tactical in nature, and favored Trump over Clinton. That is all anyone has been saying.
I agree that anyone paying attention could see that Trump was completely unsuitable for high office. The Clinton campaign relied on this, yet lost.
a reply to: DJW001
I diagnosed your psychosis as of mid december :
4 months later, you are stuck in the denial phase.
Do you need to erase of your mind the content of the OP : the ability for the US to frame anyone (with the exemple provided : RUSSIA of couse !) with their stolen malware.
I can't wait for AV companies to come of with cross-analysis between the Marble framework and their existing virus signature files in order to have a better view of what percentage of Viruses were actually released in the wild thanks to US taxpayers money for the sole promotion of US (or is it DNC) hegemony.
Crowdstrike removed his previous antirussian report because they try to save their credibility ... (head in the sand).
The CIA itself says its insiders leaks. NO ! DJW knows the CIA better than the previous director what do you imagine ! They must be Russians, they can only be Russian, they HAVE to be Russian otherwise it is not Russia ... (head in the sand).
The US has the biggest collection of election tampering, political ingerence in the world ... STFU you anti-american ! ... It's Russia who must have done it, can't you understand (head in the sand).
...

I diagnosed your psychosis as of mid december :
originally posted by: theultimatebelgianjoke
Your neo-McCarthyism has reached pathological levels.
4 months later, you are stuck in the denial phase.
Do you need to erase of your mind the content of the OP : the ability for the US to frame anyone (with the exemple provided : RUSSIA of couse !) with their stolen malware.
I can't wait for AV companies to come of with cross-analysis between the Marble framework and their existing virus signature files in order to have a better view of what percentage of Viruses were actually released in the wild thanks to US taxpayers money for the sole promotion of US (or is it DNC) hegemony.
Crowdstrike removed his previous antirussian report because they try to save their credibility ... (head in the sand).
The CIA itself says its insiders leaks. NO ! DJW knows the CIA better than the previous director what do you imagine ! They must be Russians, they can only be Russian, they HAVE to be Russian otherwise it is not Russia ... (head in the sand).
The US has the biggest collection of election tampering, political ingerence in the world ... STFU you anti-american ! ... It's Russia who must have done it, can't you understand (head in the sand).
...

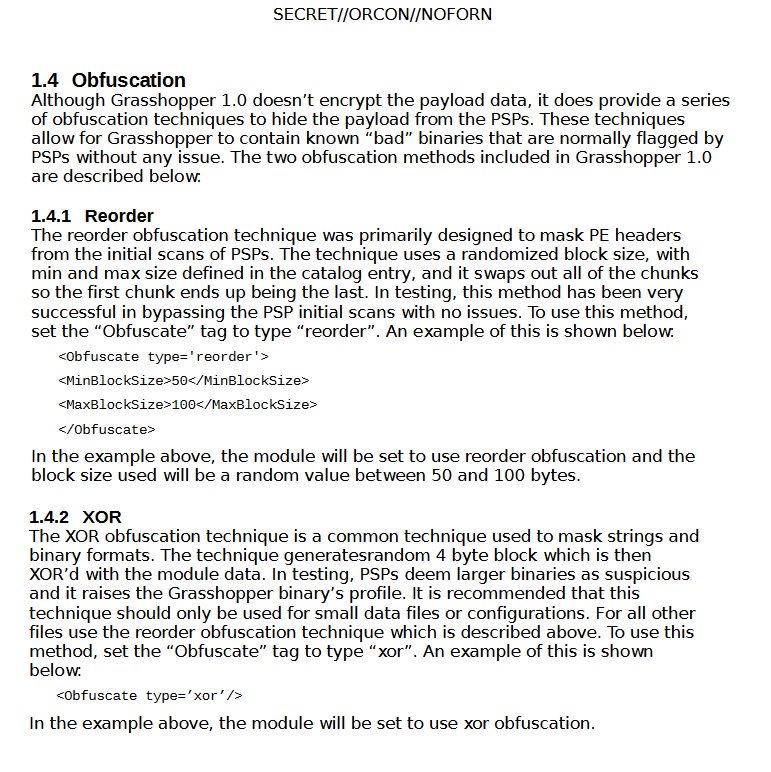
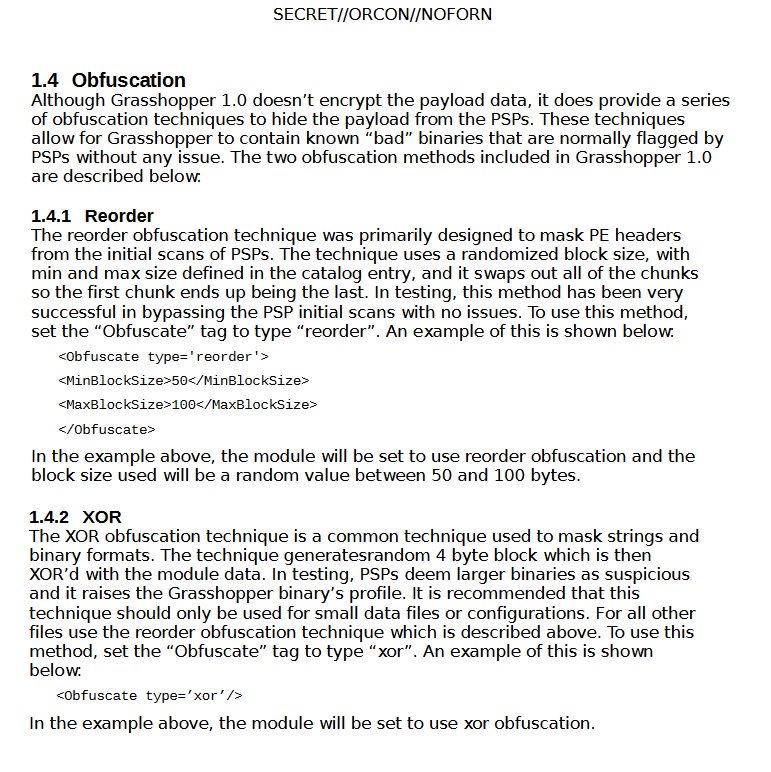
Wikileaks releases "Grasshoper" CIA malware :
Twitter
Grasshopper
7 April, 2017
Today, April 7th 2017, WikiLeaks releases Vault 7 "Grasshopper" -- 27 documents from the CIA's Grasshopper framework, a platform used to build customized malware payloads for Microsoft Windows operating systems.
Grasshopper is provided with a variety of modules that can be used by a CIA operator as blocks to construct a customized implant that will behave differently, for example maintaining persistence on the computer differently, depending on what particular features or capabilities are selected in the process of building the bundle. Additionally, Grasshopper provides a very flexible language to define rules that are used to "perform a pre-installation survey of the target device, assuring that the payload will only [be] installed if the target has the right configuration". Through this grammar CIA operators are able to build from very simple to very complex logic used to determine, for example, if the target device is running a specific version of Microsoft Windows, or if a particular Antivirus product is running or not.
Grasshopper allows tools to be installed using a variety of persistence mechanisms and modified using a variety of extensions (like encryption). The requirement list of the Automated Implant Branch (AIB) for Grasshopper puts special attention on PSP avoidance, so that any Personal Security Products like 'MS Security Essentials', 'Rising', 'Symantec Endpoint' or 'Kaspersky IS' on target machines do not detect Grasshopper elements.
One of the persistence mechanisms used by the CIA here is 'Stolen Goods' - whose "components were taken from malware known as Carberp, a suspected Russian organized crime rootkit." confirming the recycling of malware found on the Internet by the CIA. "The source of Carberp was published online, and has allowed AED/RDB to easily steal components as needed from the malware.". While the CIA claims that "[most] of Carberp was not used in Stolen Goods" they do acknowledge that "[the] persistence method, and parts of the installer, were taken and modified to fit our needs", providing a further example of reuse of portions of publicly available malware by the CIA, as observed in their analysis of leaked material from the italian company "HackingTeam".
The documents WikiLeaks publishes today provide an insights into the process of building modern espionage tools and insights into how the CIA maintains persistence over infected Microsoft Windows computers, providing directions for those seeking to defend their systems to identify any existing compromise
edit on 7-4-2017 by theultimatebelgianjoke because: Added text
Wikileaks releases 'Hive', CIA virus control system.
Twitter
Today, April 14th 2017, WikiLeaks publishes six documents from the CIA's HIVE project created by its "Embedded Development Branch" (EDB).
HIVE is a back-end infrastructure malware with a public-facing HTTPS interface which is used by CIA implants to transfer exfiltrated information from target machines to the CIA and to receive commands from its operators to execute specific tasks on the targets. HIVE is used across multiple malware implants and CIA operations. The public HTTPS interface utilizes unsuspicious-looking cover domains to hide its presence.
Anti-Virus companies and forensic experts have noticed that some possible state-actor malware used such kind of back-end infrastructure by analyzing the communication behaviour of these specific implants, but were unable to attribute the back-end (and therefore the implant itself) to operations run by the CIA. In a recent blog post by Symantec, that was able to attribute the "Longhorn" activities to the CIA based on the Vault 7, such back-end infrastructure is described:
For C&C servers, Longhorn typically configures a specific domain and IP address combination per target. The domains appear to be registered by the attackers; however they use privacy services to hide their real identity. The IP addresses are typically owned by legitimate companies offering virtual private server (VPS) or webhosting services. The malware communicates with C&C servers over HTTPS using a custom underlying cryptographic protocol to protect communications from identification.
The documents from this publication might further enable anti-malware researchers and forensic experts to analyse this kind of communication between malware implants and back-end servers used in previous illegal activities.
a reply to: theultimatebelgianjoke
The only source you believe, Joke.
“It’s time to call out WikiLeaks for what it really is, a non-state hostile intelligence service, often abetted by state actors like Russia,” Pompeo told the audience.
The only source you believe, Joke.
originally posted by: theultimatebelgianjoke
a reply to: DJW001
I don't believe Mike Pompeo ... why should I ?
And I don't believe RT, but even a broken clock is right twice a day.
a reply to: Necrose
So they can run eMule to share child porn on your computer, and you will get the blame for it if the CIA gets too angry at a activist?
I've heard about the eMule virus.
www.infowars.com...
web.archive.org...://americanlivewire.com/the-government-is-planting-child-porn-on-your-computer/
The url malformed so this url should work correctly from the Wayback Machine since article was disappeared: ur1.ca...
The eMule virus reported by USWGO Alternative News, before he was arrested by Special Agent Brian Dexter of the U.S. Department of Homeland Security (U.S. DHS), HSI Homeland Security Investigators. They arrested Brian and then he was put on suicide watch in Winston Salem, NC, they stripped him butt naked and video taped him and the jail guards ordered him to touch himself while they videotaped him and giggled.
Brian D. Hill of USWGO Alternative News was reporting truth and he was taken down.
We Are Change thinks it is the HackingTeam's Remote Control System (RCS) that set him up but it could also be Vault 7 from the CIA.
Maybe Brian should file a FOIA request with the CIA, which could put his life in danger, but if he doesn't he will continue being framed for the crime that he didn't commit, being intimidated by corrupt Federal Judges.
People can be set up, and this leak on Wikileaks helps to prove it.
We should bring up Vault 7 at Jury Trials in child porn cases, we need to start bringing up CIA connections to any claimed child porn set up claims. We need to start demanding that the CIA stop setting up activists and enemies with child porn.
So they can run eMule to share child porn on your computer, and you will get the blame for it if the CIA gets too angry at a activist?
I've heard about the eMule virus.
www.infowars.com...
web.archive.org...://americanlivewire.com/the-government-is-planting-child-porn-on-your-computer/
The url malformed so this url should work correctly from the Wayback Machine since article was disappeared: ur1.ca...
The Government Is Planting Child Porn On Your Computer
A new virus has been catalogued, and it appears to be planting and distributing child pornography files. Hackers? No. The government is planting child porn on your computer, or so an alert published today indicates.
Political Dissenters, Beware
Before Its News has interviewed a person, who spoke on condition of anonymity, that has been a victim of the virus implantation. The person was engaged in journalistic exposure of political corruption, and suddenly police appeared on his doorstep with a search warrant specifying a search for evidence of possessing and distributing child pornography. The story is a bit convoluted here, but basically the gentleman did a little more investigation and found rogue .exe files on his computer that appeared as normal emule sharing directories but contained hundreds to thousands of child pornography files. The potential whistleblower claims the virus was deliberately planted on his computer in order to stop his activity.
The article surmises the Internet Crimes Against Children task force may be behind the virus planting, though why is unclear.
Are You A Victim?
According to a USWGO Virus Report:
I believe it was surrounded by comine.exe??along with another exe file that had??random characters so I dont remember that file name since it had??a certain kind of random characters and I believe it may have??been in the TEMP folder.
It came with three rogue P2P file sharing applications that were not stored in??the usual file directories for programs or even portable programs. Those files are called ares.exe,??emule.exe, and shareaza.exe. They share possibly illegal files and files with Trojans embedded without the computer owners??permission despite invalid claims by law enforcement that no one can force a user to download and share files on P2P networks. When the user discovers them and attempts to shut down??the program using process termination on Task Manager(taskmgr.exe) the rogue??Trojan control program attempts to revive the operation of the rogue??P2P programs and will fully operate within 3-5 seconds or even??up to 10 seconds depending on??processing speed from CPU. No matter how many times the user continues stopping the program it comes right back. When the user attempts to end the task then quickly remove the files even with certain software, the Trojan that controls the rogue programs seems to regenerate the rogue programs which continues to share and??download illegal material which can get??the user in trouble
ESET Virus Radar has recognized the virus, and calls it??Win32/MoliVampire. The short description indicates, Win32/MoliVampire.A is a trojan which tries to download other malware from the Internet. Win32/MoliVampire.A may be spread via peer-to-peer networks.
The trojan contains an URL address. It tries to download a file from the address. Files are copied into a??shared folder of various instant messengers and P2P applications, according to the description.
In a hurried article posted on Before Its News, a reporter emoted:
So anyone whom receives this virus or variants of Trojans similar to this virus, is at risk of being accused of distributing and possessing child pornography then having the computers and family photos, videos, and other personal data taken away forever. Then will likely end up years in federal or state prison then receives a lifetime sex offender record, isn???t that just great!!!!!
ICE Pads Their Stats
Evidently, it isnt only alternative-news journalists who are being targeted. ??According to a Facebook page supporting 17-year-old autistic youth Andrew Rose:
Operation Flicker was started By ICE [Immigration and Customs Enforcement Agency]. U.S. Immigration and Customs Enforcement is the principal investigative arm of the U.S. Department of Homeland Security (DHS) and the second largest investigative agency in the federal government. Created in 2003 through a merger of the investigative and interior enforcement elements of the U.S. Customs Service and the Immigration and Naturalization Service,?????Operation Flicker??? is part of Project Predator, a nationwide ICE initiative to protect children from sexual predators, including instances of sex tourism with minors, Internet child pornographers, criminal alien sex offenders, and child sex traffickers, according to the agency. Unfortunately, due to the system being used to net these predators, many children are being exposed to the the same Child Porn they were trying to stop.
Apparently, in an effort to catch these dangerous internet predators, ICE attached child pornography images to .mp3 files on P2P sharing sites like LimeWire. Young Andrew Rose downloaded two songs that came with little surprise packages attached. Scandalously and shamefully, Andrew is actually being prosecuted. His lawyer, on the support page, stated:
The FBI and ICE are the ones who exposed Andrew Rose to Child Pornography .. They were the Traffickers and became That which they Seek.
What Can You Do?
Computer users, especially those who use P2P file sharing programs and messaging, are encouraged to use ESET of McAfee virus scan/destroy software as both recognize the virus. It is noted that virus protection is not bulletproof with regard to this virus, and certainly will not protect against hidden attached files in normal sharing operations. If the government is planting child porn on your computer as some people have claimed, taking any and all steps possible to protect yourself and your family, including ceasing use of P2P applications, is advisable.
The Government Is Planting Child Porn On Your Computer.
The eMule virus reported by USWGO Alternative News, before he was arrested by Special Agent Brian Dexter of the U.S. Department of Homeland Security (U.S. DHS), HSI Homeland Security Investigators. They arrested Brian and then he was put on suicide watch in Winston Salem, NC, they stripped him butt naked and video taped him and the jail guards ordered him to touch himself while they videotaped him and giggled.
Brian D. Hill of USWGO Alternative News was reporting truth and he was taken down.
We Are Change thinks it is the HackingTeam's Remote Control System (RCS) that set him up but it could also be Vault 7 from the CIA.
Maybe Brian should file a FOIA request with the CIA, which could put his life in danger, but if he doesn't he will continue being framed for the crime that he didn't commit, being intimidated by corrupt Federal Judges.
People can be set up, and this leak on Wikileaks helps to prove it.
We should bring up Vault 7 at Jury Trials in child porn cases, we need to start bringing up CIA connections to any claimed child porn set up claims. We need to start demanding that the CIA stop setting up activists and enemies with child porn.
edit on 16-5-2017 by StanleyBolten because: (no
reason given)
new topics
-
Electrical tricks for saving money
Education and Media: 41 minutes ago -
VP's Secret Service agent brawls with other agents at Andrews
Mainstream News: 2 hours ago -
Sunak spinning the sickness figures
Other Current Events: 2 hours ago -
Nearly 70% Of Americans Want Talks To End War In Ukraine
Political Issues: 2 hours ago -
Late Night with the Devil - a really good unusual modern horror film.
Movies: 4 hours ago -
Cats Used as Live Bait to Train Ferocious Pitbulls in Illegal NYC Dogfighting
Social Issues and Civil Unrest: 6 hours ago -
The Good News According to Jesus - Episode 1
Religion, Faith, And Theology: 7 hours ago -
HORRIBLE !! Russian Soldier Drinking Own Urine To Survive In Battle
World War Three: 10 hours ago
top topics
-
SETI chief says US has no evidence for alien technology. 'And we never have'
Aliens and UFOs: 16 hours ago, 8 flags -
Cats Used as Live Bait to Train Ferocious Pitbulls in Illegal NYC Dogfighting
Social Issues and Civil Unrest: 6 hours ago, 8 flags -
Florida man's trip overseas ends in shock over $143,000 T-Mobile phone bill
Social Issues and Civil Unrest: 12 hours ago, 8 flags -
VP's Secret Service agent brawls with other agents at Andrews
Mainstream News: 2 hours ago, 6 flags -
Former Labour minister Frank Field dies aged 81
People: 15 hours ago, 4 flags -
Bobiverse
Fantasy & Science Fiction: 12 hours ago, 3 flags -
HORRIBLE !! Russian Soldier Drinking Own Urine To Survive In Battle
World War Three: 10 hours ago, 3 flags -
Nearly 70% Of Americans Want Talks To End War In Ukraine
Political Issues: 2 hours ago, 3 flags -
Sunak spinning the sickness figures
Other Current Events: 2 hours ago, 3 flags -
Late Night with the Devil - a really good unusual modern horror film.
Movies: 4 hours ago, 2 flags
active topics
-
Sunak spinning the sickness figures
Other Current Events • 4 • : annonentity -
Cats Used as Live Bait to Train Ferocious Pitbulls in Illegal NYC Dogfighting
Social Issues and Civil Unrest • 12 • : Hakaiju -
HORRIBLE !! Russian Soldier Drinking Own Urine To Survive In Battle
World War Three • 28 • : budzprime69 -
Huge ancient city found in the Amazon.
Ancient & Lost Civilizations • 61 • : Therealbeverage -
The Reality of the Laser
Military Projects • 43 • : 5thHead -
VP's Secret Service agent brawls with other agents at Andrews
Mainstream News • 16 • : matafuchs -
Should Biden Replace Harris With AOC On the 2024 Democrat Ticket?
2024 Elections • 49 • : Therealbeverage -
WF Killer Patents & Secret Science Vol. 1 | Free Energy & Anti-Gravity Cover-Ups
General Conspiracies • 32 • : Arbitrageur -
Is there a hole at the North Pole?
ATS Skunk Works • 38 • : Therealbeverage -
SETI chief says US has no evidence for alien technology. 'And we never have'
Aliens and UFOs • 41 • : TheMisguidedAngel
