It looks like you're using an Ad Blocker.
Please white-list or disable AboveTopSecret.com in your ad-blocking tool.
Thank you.
Some features of ATS will be disabled while you continue to use an ad-blocker.
9
share:
About two weeks ago i was going site to site looking for
something interesting to read and ended up on zerohedge
and saw this story on the page.

After i read the page i went to the comments below which
on that site are sometimes better than the story (sorry tyler)
and came across this link.
Now i was expecting a funny/stupid picture or something but
i got this warning from my computer.
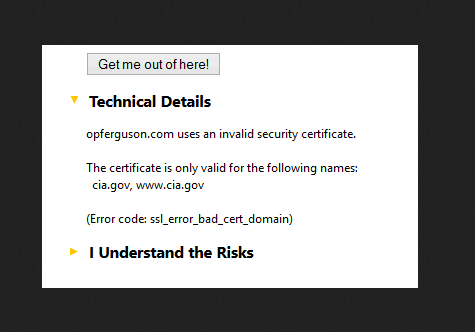
When i moved the arrow over the link it came up as i.imgur.com
not opfurguson.com and i.imgur.com came up in the address bar
as well.
But i did do a whois check and didn't see anything useful.

Now i did a little search on the opfurguson site and came up with
a story on it being used a honeypot to get peoples i.p. address
on Motherboard but I'm not sure whats happen on zerohedge
but it is a very anti wall street/government site so maybe the link
been added to find out the i.p. address of readers for some reason.
The link to the zerohedge page is below and that post is still there
doing the same thing so if anyone wants to give it a try.
Anyone know whats this about ?
[url=http://www.zerohedge.com/news/2014-08-14/us-and-israeli-military-tactics-used-against-american-citizens-%E2%80%A6-gazans-tweet-tips-h]zerohedge[/ url]
something interesting to read and ended up on zerohedge
and saw this story on the page.

After i read the page i went to the comments below which
on that site are sometimes better than the story (sorry tyler)
and came across this link.
Now i was expecting a funny/stupid picture or something but
i got this warning from my computer.
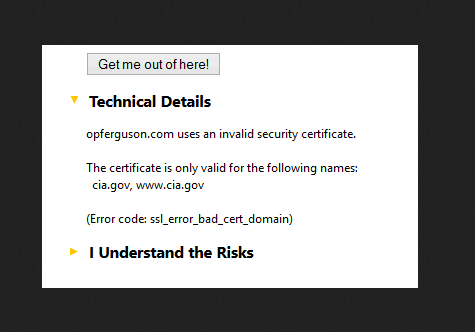
When i moved the arrow over the link it came up as i.imgur.com
not opfurguson.com and i.imgur.com came up in the address bar
as well.
But i did do a whois check and didn't see anything useful.

Now i did a little search on the opfurguson site and came up with
a story on it being used a honeypot to get peoples i.p. address
on Motherboard but I'm not sure whats happen on zerohedge
but it is a very anti wall street/government site so maybe the link
been added to find out the i.p. address of readers for some reason.
The link to the zerohedge page is below and that post is still there
doing the same thing so if anyone wants to give it a try.
Anyone know whats this about ?
[url=http://www.zerohedge.com/news/2014-08-14/us-and-israeli-military-tactics-used-against-american-citizens-%E2%80%A6-gazans-tweet-tips-h]zerohedge[/ url]
edit on 7/9/2014 by skuly because: (no reason given)
Hmmm. I went to Conternation Security. Not sure, but maybe a CIA front to gather cyber information. But, is
has a .us and below is their Whois.
Domain Name: CONSTERNATION.US
Registry Domain ID: D38891731-US
Registrar WHOIS Server: whois.godaddy.com
Registrar URL: www.godaddy.com...
Update Date: 2014-01-19 11:35:25
Creation Date: 2013-01-19 09:05:41
Registrar Registration Expiration Date: 2015-01-18 23:59:59
Registrar: GoDaddy.com, LLC
Registrar IANA ID: 146
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.480-624-2505
Domain Status: ok
Registry Registrant ID: CR134772081
Registrant Name: David Heine
Registrant Organization: Consternation Security
Registrant Street: 4424 Gaines Ranch Loop
Registrant Street: apt 206
Registrant City: Austin
Registrant State/Province: Texas
Registrant Postal Code: 78735
Registrant Country: United States
Registrant Phone: +1.3476704638
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID: CR134772083
Admin Name: David Heine
Admin Organization: Consternation Security
Admin Street: 4424 Gaines Ranch Loop
Admin Street: apt 206
Admin City: Austin
Admin State/Province: Texas
Admin Postal Code: 78735
Admin Country: United States
Admin Phone: +1.3476704638
Admin Phone Ext:
Admin Fax:
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID: CR134772082
Tech Name: David Heine
Tech Organization: Consternation Security
Tech Street: 4424 Gaines Ranch Loop
Tech Street: apt 206
Tech City: Austin
Tech State/Province: Texas
Tech Postal Code: 78735
Tech Country: United States
Tech Phone: +1.3476704638
Tech Phone Ext:
Tech Fax:
Tech Fax Ext:
Tech Email: [email protected]
Name Server: NS03.DOMAINCONTROL.COM
Name Server: NS04.DOMAINCONTROL.COM
DNSSEC: unsigned
The domaincontrol and use of Ops like OpsFerguson seems like a gov/military, intel person at least is thinking like one to use those names. I don't know at this point as I have been out of IT since 2005.
Domain Name: CONSTERNATION.US
Registry Domain ID: D38891731-US
Registrar WHOIS Server: whois.godaddy.com
Registrar URL: www.godaddy.com...
Update Date: 2014-01-19 11:35:25
Creation Date: 2013-01-19 09:05:41
Registrar Registration Expiration Date: 2015-01-18 23:59:59
Registrar: GoDaddy.com, LLC
Registrar IANA ID: 146
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.480-624-2505
Domain Status: ok
Registry Registrant ID: CR134772081
Registrant Name: David Heine
Registrant Organization: Consternation Security
Registrant Street: 4424 Gaines Ranch Loop
Registrant Street: apt 206
Registrant City: Austin
Registrant State/Province: Texas
Registrant Postal Code: 78735
Registrant Country: United States
Registrant Phone: +1.3476704638
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID: CR134772083
Admin Name: David Heine
Admin Organization: Consternation Security
Admin Street: 4424 Gaines Ranch Loop
Admin Street: apt 206
Admin City: Austin
Admin State/Province: Texas
Admin Postal Code: 78735
Admin Country: United States
Admin Phone: +1.3476704638
Admin Phone Ext:
Admin Fax:
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID: CR134772082
Tech Name: David Heine
Tech Organization: Consternation Security
Tech Street: 4424 Gaines Ranch Loop
Tech Street: apt 206
Tech City: Austin
Tech State/Province: Texas
Tech Postal Code: 78735
Tech Country: United States
Tech Phone: +1.3476704638
Tech Phone Ext:
Tech Fax:
Tech Fax Ext:
Tech Email: [email protected]
Name Server: NS03.DOMAINCONTROL.COM
Name Server: NS04.DOMAINCONTROL.COM
DNSSEC: unsigned
The domaincontrol and use of Ops like OpsFerguson seems like a gov/military, intel person at least is thinking like one to use those names. I don't know at this point as I have been out of IT since 2005.
edit on 7/9/14 by spirit_horse because: (no reason given)
(post by Maluhia removed for a serious terms and conditions violation)
Wow. Good eye, OP. It seems you may have found something. I would say that it's a safe bet to say that many government agencies have websites up to
steer the sheep. I'll also have to check this 'Zero Hedge' site out because it sounds right up my alley.
a reply to: spirit_horse and Maluhia
Thanks for the info.
But what i don't get is the redirect from zerohedge i mean if
its happening there then its probably happening on other
sites too without people knowing.
If Heine just after Anonymous then why the CIA warning on
a site that not got much to do with anon unless they spreading
out to other anti government sites.
Thanks for the info.
But what i don't get is the redirect from zerohedge i mean if
its happening there then its probably happening on other
sites too without people knowing.
If Heine just after Anonymous then why the CIA warning on
a site that not got much to do with anon unless they spreading
out to other anti government sites.
edit on 7/9/2014 by skuly because: typo
It looks like a joke to me.
But if you visit sites like ATS, ZH, AJ, etc. you have been profiled already. People who don`t visit such sites are almost automatically regarded as "safe".
But if you visit sites like ATS, ZH, AJ, etc. you have been profiled already. People who don`t visit such sites are almost automatically regarded as "safe".
a reply to: skuly
Yes, honeypot...
Joseph Cox @josephcox
Pastebin 1
Pastebin 2
And Heine's Twitter shows he has a history of such activity
ETA:
Consternation Security About
CN's Go Get Funding
An email list subscribed to associated [email protected] address that intrestingly has this email address subscribed "c.nicke2-radium.ncsc.mil" associated with Information Assurance
ETA:
and
As taken from information from the following PDF's here and here respectively.
With that in mind, as noted, if you visit sites like this you are likely highly profiled. You only have one choice, make your beliefs, opinions, philosophies, and thoughts as clear as possible. They want to know, so let them the know. Surely don't let them intimidate/scare you away from your lawful activities, otherwise, they win. The more people who openly let them know how they feel, the more the operators will come to realize they are working for the wrong side. The more people who cross the realm from lawful into extremist, the operators will feel justified. Being caught in a honeytrap when you are lawfully expressing/protesting while doing so in a manner that others are openly able to see those activities is a loss in the hearts and minds to TPTB, it is one of the reasons why more people are waking up faster.
Yes, honeypot...
Joseph Cox @josephcox
This guy is harvesting the IP addresses of #OpFerguson to hand to the police motherboard.vice.com... … #anonymous
Pastebin 1
www.opferguson.com suspected honeypot ( domain bought 8/12/13
[email protected]
email linked to
www.consternation.us...
Registrant Name: David Heine
Registrant Organization: Consternation Security
Thought they were gone, but still reging sites.
Pastebin 2
And Heine's Twitter shows he has a history of such activity
#NYPD if you want help, email us at [email protected] we are very interested assisting/collaborating ideas. Reply Retweet Favorite 5:05 PM - 21 Apr 2012
ETA:
Consternation Security About
The purpose of this site is to express our repulsive urge to vomit from the lawless acts done by hackers day after day. if there ever was a code of ethics in the world, it has been thrown out the window. Never should private consumer data be made public.
Anonymous has stated many times that they are fighting for the people, but time after time they violate the very right they claim to be protecting. and so we will remain here exposing the truth behind the scenes.
Content for our articles are created from conversations we monitor, while they may contain some amusement, the topic really has been discussed somewhere on Internet Relay Chat.
CN's Go Get Funding
Donations allow operations for Consternation Security.
This includes anti-Hacker campaigns, anti-pedo campaigns, Honeypot hosting, Software Development, Domain Registrations, Outsourcing when needed, Utilities, and other general expenses needed to operate.
Donations can be made Anonymously. You will be provided an option, be sure to select it to keep your name from being shown if you wish to remain a mystery.
Another method of anonymous donations is using GreenDot Reload MoneyPak.
An email list subscribed to associated [email protected] address that intrestingly has this email address subscribed "c.nicke2-radium.ncsc.mil" associated with Information Assurance
ETA:
National Security Agency
Ms. Christine M. Nickell
Chief, Academic Outreach (I02E)
I02E Ste 6744, 9800 Savage Rd, Ft. Meade, MD 20755-6744
(comm) 410-854-6206, (fax) 410-854-7043
[email protected]
and
Christine Nickell
Co-Leader Department of Defense
9800 Savage Road Suite 6722
Ft. Meade, MD 20755
1.410.854.6206
[email protected]
As taken from information from the following PDF's here and here respectively.
With that in mind, as noted, if you visit sites like this you are likely highly profiled. You only have one choice, make your beliefs, opinions, philosophies, and thoughts as clear as possible. They want to know, so let them the know. Surely don't let them intimidate/scare you away from your lawful activities, otherwise, they win. The more people who openly let them know how they feel, the more the operators will come to realize they are working for the wrong side. The more people who cross the realm from lawful into extremist, the operators will feel justified. Being caught in a honeytrap when you are lawfully expressing/protesting while doing so in a manner that others are openly able to see those activities is a loss in the hearts and minds to TPTB, it is one of the reasons why more people are waking up faster.
edit on 9/7/2014 by AllSourceIntel because: (no reason
given)
edit on 9/7/2014 by AllSourceIntel because: add bold
edit on 9/7/2014 by AllSourceIntel because: (no reason
given)
a reply to: AllSourceIntel
Wow your really good at this sort of thing .
Pity i could only give you one star for all that work so
i went though your last 20 posts and gave a star for each
as a thank you.
Wow your really good at this sort of thing .
Pity i could only give you one star for all that work so
i went though your last 20 posts and gave a star for each
as a thank you.
a reply to: skuly
Um, thank you and you are most welcome. No need to give me all those stars though, but it is appreciated. Next time, you just might want send an email to the agency that the honeypot is working for and state your intentions of "public interest to information" and "academic freedom" with the added line "if you are going to be so interested in my activity, you can cut out the middle man and just ask for it, in this case, I'll just give it to you since you are getting it anyway." It would be humorous I think, I've actually have done it...and told them to say hello to some former co-workers
Um, thank you and you are most welcome. No need to give me all those stars though, but it is appreciated. Next time, you just might want send an email to the agency that the honeypot is working for and state your intentions of "public interest to information" and "academic freedom" with the added line "if you are going to be so interested in my activity, you can cut out the middle man and just ask for it, in this case, I'll just give it to you since you are getting it anyway." It would be humorous I think, I've actually have done it...and told them to say hello to some former co-workers
edit on 9/7/2014 by AllSourceIntel because: spelling
Early on opfurguson.com was noted to be collecting IPs. Good to let this info out for those who didn't catch the warning.
Biggest question is, how many other similar sites (appearing for a protest, demonstration,etc) are operating with intent of IP collection.
Biggest question is, how many other similar sites (appearing for a protest, demonstration,etc) are operating with intent of IP collection.
reply to: skuly
I've been going between 3 main sites for some time. They are:
ATS
ZeroHedge
Infowars
I find ATS to be the most...public. Still has many shills, but good intelligence as well.
ZeroHedge is ....interesting. They have good stuff. Sometimes it seems to be too good. Tyler Durden works 24/7 it seems.
Infowars takes their news from ZH quite often. And doesn't hide that fact. And I honestly don't trust Infowars, seeing as doom porn is their bread and butter.
Not sure what to think of any of it. Interesting to say the least.
I've been going between 3 main sites for some time. They are:
ATS
ZeroHedge
Infowars
I find ATS to be the most...public. Still has many shills, but good intelligence as well.
ZeroHedge is ....interesting. They have good stuff. Sometimes it seems to be too good. Tyler Durden works 24/7 it seems.
Infowars takes their news from ZH quite often. And doesn't hide that fact. And I honestly don't trust Infowars, seeing as doom porn is their bread and butter.
Not sure what to think of any of it. Interesting to say the least.
new topics
-
The Democrats Take Control the House - Look what happened while you were sleeping
US Political Madness: 32 minutes ago -
Sheetz facing racial discrimination lawsuit for considering criminal history in hiring
Social Issues and Civil Unrest: 37 minutes ago -
In an Historic First, In N Out Burger Permanently Closes a Location
Mainstream News: 2 hours ago -
MH370 Again....
Disaster Conspiracies: 3 hours ago -
Are you ready for the return of Jesus Christ? Have you been cleansed by His blood?
Religion, Faith, And Theology: 5 hours ago -
Chronological time line of open source information
History: 6 hours ago -
A man of the people
Diseases and Pandemics: 7 hours ago -
Ramblings on DNA, blood, and Spirit.
Philosophy and Metaphysics: 8 hours ago -
4 plans of US elites to defeat Russia
New World Order: 9 hours ago
top topics
-
Israeli Missile Strikes in Iran, Explosions in Syria + Iraq
World War Three: 16 hours ago, 17 flags -
In an Historic First, In N Out Burger Permanently Closes a Location
Mainstream News: 2 hours ago, 14 flags -
Thousands Of Young Ukrainian Men Trying To Flee The Country To Avoid Conscription And The War
Other Current Events: 13 hours ago, 7 flags -
The Democrats Take Control the House - Look what happened while you were sleeping
US Political Madness: 33 minutes ago, 6 flags -
Iran launches Retalliation Strike 4.18.24
World War Three: 16 hours ago, 6 flags -
4 plans of US elites to defeat Russia
New World Order: 9 hours ago, 4 flags -
12 jurors selected in Trump criminal trial
US Political Madness: 15 hours ago, 4 flags -
A man of the people
Diseases and Pandemics: 7 hours ago, 4 flags -
Chronological time line of open source information
History: 6 hours ago, 2 flags -
Are you ready for the return of Jesus Christ? Have you been cleansed by His blood?
Religion, Faith, And Theology: 5 hours ago, 2 flags
active topics
-
4 plans of US elites to defeat Russia
New World Order • 34 • : Oldcarpy2 -
The Democrats Take Control the House - Look what happened while you were sleeping
US Political Madness • 5 • : ImagoDei -
12 jurors selected in Trump criminal trial
US Political Madness • 56 • : ImagoDei -
Israeli Missile Strikes in Iran, Explosions in Syria + Iraq
World War Three • 84 • : Oldcarpy2 -
Sheetz facing racial discrimination lawsuit for considering criminal history in hiring
Social Issues and Civil Unrest • 2 • : Hecate666 -
Fossils in Greece Suggest Human Ancestors Evolved in Europe, Not Africa
Origins and Creationism • 71 • : Consvoli -
MH370 Again....
Disaster Conspiracies • 5 • : billxam1 -
SC Jack Smith is Using Subterfuge Tricks with Donald Trumps Upcoming Documents Trial.
Dissecting Disinformation • 99 • : matafuchs -
Are you ready for the return of Jesus Christ? Have you been cleansed by His blood?
Religion, Faith, And Theology • 15 • : 19Bones79 -
New Photo's reveal Railway System underneathe the Pyramids
Breaking Alternative News • 30 • : jshdnl
9
